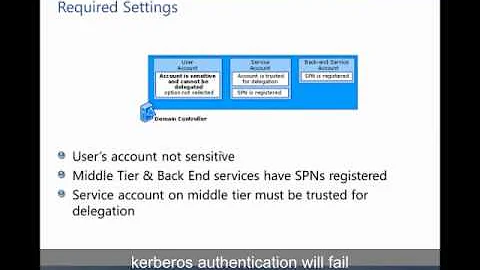
Apache Kerberos Authentication - Client didn't delegate us their credential
The KRB5KDC_ERR_S_PRINCIPAL_UNKNOWN error is due to a bad generated map file with ktpass.exe in the AD server.
Generate a correct map file with ktpass.exe as this:
ktpass -princ HTTP/[email protected] -mapuser username\HTTP-hesl035 -crypto ALL -ptype KRB5_NT_PRINCIPAL -mapop set -pass password -out c:\tem
p\krb5.keytab
And assign the user a SPN with setspn.exe in the AD server:
setspn -s HTTP/example.es HTTP-hesl035
- HTTP-hesl035 is apache server username created in AD.
Related videos on Youtube
Packet Tracer
tcpdump -xi eth0 | grep "(([0-9]{1,3}\.?)){4}" > packets_traced
Updated on September 15, 2022Comments
-
 Packet Tracer over 1 year
Packet Tracer over 1 yearI'm trying to use mod_auth_kerb to log in users into my website automatically against an AD server running on W2008 Server. Users are already logged in a windows network, and access to the website.
My virtual server conf is:
<Location /> Order allow,deny Satisfy Any AuthType Kerberos AuthName "Kerberos Login ORN" KrbMethodNegotiate On KrbMethodK5Passwd Off KrbServiceName Any KrbAuthRealms EXAMPLE.ES Krb5KeyTab /etc/krb5.keytab require valid-user </Location>I succesfully login via kinit from apache:
kinit -t /etc/HTTP-hesl035.keytab Password for [email protected]: klist Ticket cache: FILE:/tmp/krb5cc_0 Default principal: [email protected] Valid starting Expires Service principal 11/07/13 17:55:46 11/08/13 03:55:51 krbtgt/[email protected] renew until 11/08/13 03:55:46or
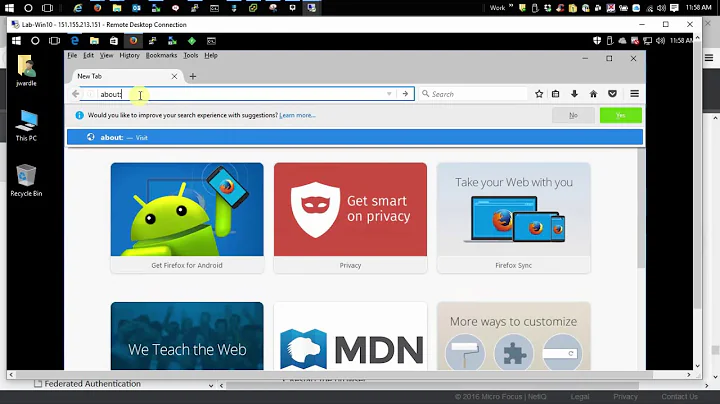
kinit HTTP-hesl035 Password for [email protected]: klist Ticket cache: FILE:/tmp/krb5cc_0 Default principal: [email protected] Valid starting Expires Service principal 11/07/13 17:57:26 11/08/13 03:57:26 krbtgt/[email protected] renew until 11/08/13 03:57:26I configure firefox with the settings:
network.negotiate-auth.delegation.uris = testing.example.es network.negotiate-auth.trusted.uris = testing.example.esWhen I access to the site I get an Authoritation Required.
1st Header sent by browser is:
GET Host: testing.example.es1st Header response by server is:
401 Authorization required WWW-authenticate: Negotiate2nd header sent by browser is:
GET Host: testing.example.es Authentication: Negotiate {TOKEN}2nd header sent by server is:
401 Athorization requiredApache log saying the following:
Thu Nov 07 18:06:09 2013] [debug] src/mod_auth_kerb.c(1939): [client 192.168.4.16] kerb_authenticate_user entered with user (NULL) and auth_type Kerberos [Thu Nov 07 18:06:09 2013] [debug] src/mod_auth_kerb.c(1939): [client 192.168.4.16] kerb_authenticate_user entered with user (NULL) and auth_type Kerberos [Thu Nov 07 18:06:09 2013] [debug] src/mod_auth_kerb.c(1691): [client 192.168.4.16] Verifying client data using KRB5 GSS-API [Thu Nov 07 18:06:09 2013] [debug] src/mod_auth_kerb.c(1707): [client 192.168.4.16] Client didn't delegate us their credential [Thu Nov 07 18:06:09 2013] [debug] src/mod_auth_kerb.c(1735): [client 192.168.4.16] Warning: received token seems to be NTLM, which isn't supported by the Kerberos module. Check your IE configuration. [Thu Nov 07 18:06:09 2013] [debug] src/mod_auth_kerb.c(1138): [client 192.168.4.16] GSS-API major_status:00010000, minor_status:00000000 [Thu Nov 07 18:06:09 2013] [error] [client 192.168.4.16] gss_accept_sec_context() failed: An unsupported mechanism was requested (, Unknown error)Using krbtray.exe on the users windows machine i see the following tickets:
EXAMPLE.ES - host/minit-bn-example.es - krbtgt/EXAMPLE.ESI get the krbtgt/EXAMPLE.ES when I visit the apache app.
Seems that the client is sending the kerberos ticket, but not sure of it. Anyone knows about this issue??
EDIT:
If I set KrbMethodK5Passwd to On in my apache conf, I get a popup with user/pass form when accessing the web app. But I cannot login with user credentials.
Apache log says:
[Thu Nov 07 17:41:34 2013] [debug] src/mod_auth_kerb.c(1939): [client 192.168.4.16] kerb_authenticate_user entered with user (NULL) and auth_type Kerberos [Thu Nov 07 17:41:34 2013] [error] [client 192.168.4.16] Error parsing server name (Any): Hostname cannot be canonicalized [Thu Nov 07 17:41:34 2013] [debug] src/mod_auth_kerb.c(1110): [client 192.168.4.16] kerb_authenticate_user_krb5pwd ret=401 user=(NULL) authtype=(NULL)If I use wireshark in windows client to fetch packets, I get 2 kerberos errors from the AD to the windows client:
KRB Error: KRB5KRB_ERR_RESPONSE_TOO_BIG KRB Error: KRB5KDC_ERR_S_PRINCIPAL_UNKNOWN