How to see full HTTPS URL in wireShark
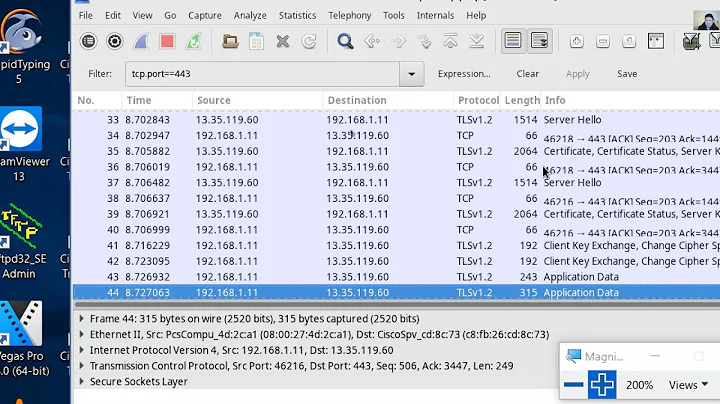
The problem is that you are using https. That means that the only informations that you have directly are the peer address and the ports used. All exchanged data is encrypted, including the request itself that should be GET /v0/item/12345.json
TL/DR: you cannot. That is one of the goals of the https protocol: wireshark acts as a man in the middle and https protects your privacy.
Related videos on Youtube
sapy
Competitive algorithm expert, Big data Ninja, An engineer by heart. Geek. I work for "The bank that runs the world" Enterprise Web Application Architect. Full Stack Engineer with expertise in web security, performance, Spark, MemSql, Kafka, Java8, Spring Boot, HDFS, and HBase. Author, speaker, Blogger, and a geek. 10+ Years of experience in Full-stack Web Technologies.
Updated on June 04, 2022Comments
-
 sapy almost 2 years
sapy almost 2 yearsI did enough research and failed to find a conclusive answer(version 1.12.7).
My local server is making a get call to
https://hacker-news.firebaseio.com/v0/item/12345.jsonwhen I see this packet inwiresharkI see thedestination URLashacker-news.firebaseio.com. My ask is simple1) how can I see the entire URI including
/v0/item/12345.jsonpart.2) Why are somany dots in the following TCP stream and what does this TCP stream actually trying to say with jabbered English letters.
...........Z..d.2......j.q..n8..{."RE...wT...../.+.0.,...'.g.(.k.$... .........j.i.h.9.8.7.6.2...*.&.......=.5.#...........@.?.>.3.2.1.0.1.-.).% .....f.........localhost......... .......3t......5...1..W:....".q.........m....r.>?t w..............#.................0...0..|.......%e.x.#s.0 ..*.H.. .....0I1.0...U....US1.0...U. . Google Inc1%0#..U....Google Internet Authority G20.. 151217200354Z. 161216000000Z0j1.0...U....US1.0...U... California1.0...U... Mountain View1.0...U. ..{.<...[L.......V..7.`?Yb.oF.z.....aC#..FtqyG0..p....-s...........d0.pe....3....5s.....T..y.F.I..w{.zX!...ou.db..j <..+......y.]..`.{V ..q..z"P<T.,<.}.. ..........._j.B.*F.\.0 gJa.E..........V).-z...][email protected]!n......<......`...........>....:QAnd description
244 19.329480000 sapy hacker-news.firebaseio.com TCP 435 47965→https [PSH, ACK] Seq=471 Ack=3948 Win=40576 Len=369 TSval=20106775 TSecr=4020547278 hacker-news.firebaseio.com 244-
zaph almost 8 yearsTry using Charles Proxy, it is HTTP/HTTPS only and can install a proxy so you can see the unencrypted data as long as the certificate is not pinned. It is also much easier to use and has a 30-day free trial.
-
 grochmal almost 8 yearsAnother option is to use Tamper Data (or Tamper Chrome), it is a completely free software proxy inside the browser. Although it has the downside that it cannot export PCAP files.
grochmal almost 8 yearsAnother option is to use Tamper Data (or Tamper Chrome), it is a completely free software proxy inside the browser. Although it has the downside that it cannot export PCAP files.
-
-
 sapy almost 8 yearswhen we make a
sapy almost 8 yearswhen we make aHTTPScall from browser, it encrypts the data , But when I'm making the call from my node server , who is doing the task of hiding all data to an outgoing request which is hittingwireshirkfirst before hitting any DNS server ? Is there any other way I can see the entire URI ? -
 Serge Ballesta almost 8 years@sapy: at the moment the TCP packet is built, data is already encrypted. The only thing you can do is to log (of display anywhere the url you use to build the request before it is actually sent.
Serge Ballesta almost 8 years@sapy: at the moment the TCP packet is built, data is already encrypted. The only thing you can do is to log (of display anywhere the url you use to build the request before it is actually sent. -
 sapy almost 8 yearsI changed the end point to a different
sapy almost 8 yearsI changed the end point to a differentHTTPapihttp://api.open-notify.org/still can't see the full url -
 Serge Ballesta almost 8 years@sapy: When using a
Serge Ballesta almost 8 years@sapy: When using ahttpprotocol, wireshark does show the full URL. You should look in wireshark at the HTTP or TCP level.