ubuntu iptables NAT & Router & Port Forwarding
I could solve the problem. I did a mistake in the routing table of the target (192.168.0.16). Changing the gateway on this machine makes the port forwarding work.
Related videos on Youtube
pallago
Updated on September 18, 2022Comments
-
pallago over 1 year
I would like to forward the ssh port from ubuntu-fw (firewall) to ubuntu-server1.
| Internet | --- | Router (hardware) | --- | ubuntu-fw | ---- | ubuntu-server1 |
Router (hardware): Fritz-Box
ubuntu-fw: ubuntu 16 serving as firewall
ubuntu-server1: ubuntu 16 serving as ssh server
The Router(hardware) forwards the port to ubuntu-fw. However, for test purposes, I placed a computer in between:
| test-pc | --- | ubuntu-fw | ---- | ubuntu-server1 |
Now I would like to access from the test-pc to my ubuntu-server1 via ubuntu-fw by using:
ssh myuser@ubuntu-server1The network topology is as follows:
test-pc: 192.168.183.253/24
ubuntu-fw: eth0: 192.168.0.254/24 & eth2: 192.168.183.254/24
ubuntu-server: 192.168.0.16/24
My question is how I should forward the port 22 in the ubuntu-fw?
I enabled routing:
$ sysctl net.ipv4.ip_forward net.ipv4.ip_forward = 1I also created a rule which allows the ubuntu-server1 to connect to the internet using ubuntu-fw as NAT. This works fine. But I fail when I want to forward the port 22 to ubuntu-server1.
In order to generate the iptables-script I use fwbuilder.
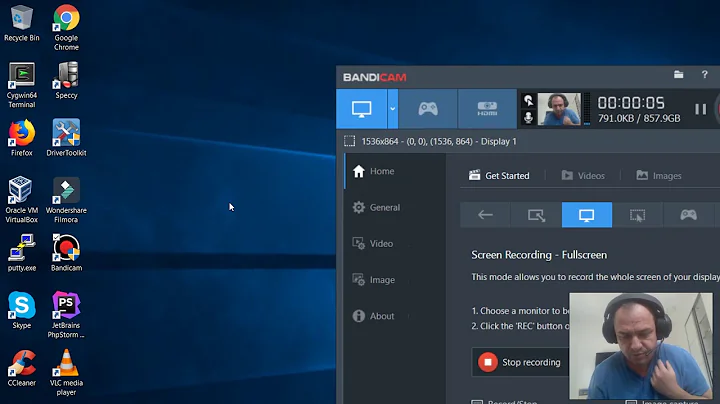
I created a nat rule resulting in (after compiling): Picture of fwbuilder NAT rule
$IPTABLES -t nat -A PREROUTING -p tcp -m tcp -d 192.168.183.254 --dport 22 -j DNAT --to-destination 192.168.0.16and I created a policy resulting in (after compiling): Picture of fwbuilder policy
$IPTABLES -A FORWARD -i eth2 -p tcp -m tcp -d 192.168.0.16 --dport 22 -m state --state NEW -j ACCEPTWhen I try to establish a connection from test-pc I see:
ssh: connect to host 192.168.183.254 port 22: Connection timed outDoes anybody have an idea what I am doing wrong?
Here is the output of iptables -v -x -n -L
Chain INPUT (policy DROP 417 packets, 49211 bytes) pkts bytes target prot opt in out source destination 28201 2294981 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 1 60 In_RULE_1 tcp -- eth0 * 192.168.0.0/24 192.168.0.254 tcp dpt:22 state NEW 0 0 In_RULE_2 tcp -- eth0 * 192.168.0.0/24 0.0.0.0/0 tcp multiport dports 21,80,443 state NEW 0 0 In_RULE_5 all -- eth2 * 0.0.0.0/0 192.168.183.254 Chain FORWARD (policy DROP 0 packets, 0 bytes) pkts bytes target prot opt in out source destination 3071 2805588 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 2 104 In_RULE_2 tcp -- eth0 * 192.168.0.0/24 0.0.0.0/0 tcp multiport dports 21,80,443 state NEW 7 420 ACCEPT tcp -- eth2 * 0.0.0.0/0 192.168.0.16 tcp dpt:22 state NEW Chain OUTPUT (policy DROP 8 packets, 480 bytes) pkts bytes target prot opt in out source destination 15619 310844265 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 0 0 Out_RULE_0 tcp -- * eth2 192.168.183.254 0.0.0.0/0 tcp multiport dports 80,443 state NEW Chain In_RULE_1 (1 references) pkts bytes target prot opt in out source destination 1 60 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 6 prefix "RULE 1 -- ACCEPT " 1 60 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 Chain In_RULE_2 (2 references) pkts bytes target prot opt in out source destination 2 104 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 6 prefix "RULE 2 -- ACCEPT " 2 104 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 Chain In_RULE_5 (1 references) pkts bytes target prot opt in out source destination 0 0 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 6 prefix "RULE 5 -- DENY " 0 0 DROP all -- * * 0.0.0.0/0 0.0.0.0/0 Chain Out_RULE_0 (1 references) pkts bytes target prot opt in out source destination 0 0 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 6 prefix "RULE 0 -- ACCEPT " 0 0 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0And the output of sudo iptables -t nat -v -x -n -L:
Chain PREROUTING (policy ACCEPT 1049 packets, 207739 bytes) pkts bytes target prot opt in out source destination 1 60 DNAT tcp -- * * 0.0.0.0/0 192.168.183.254 tcp dpt:22 to:192.168.0.16 Chain INPUT (policy ACCEPT 3 packets, 180 bytes) pkts bytes target prot opt in out source destination Chain OUTPUT (policy ACCEPT 22 packets, 1308 bytes) pkts bytes target prot opt in out source destination Chain POSTROUTING (policy ACCEPT 1 packets, 60 bytes) pkts bytes target prot opt in out source destination 2 104 SNAT all -- * eth2 192.168.0.0/24 0.0.0.0/0 to:192.168.183.254Since I have many other policies to add, I would like to use fwbuilder- also for the NAT rule.
Here is the output of tcpdump
sudo tcpdump -n -tttt -i eth2 port 22:2017-04-21 20:07:01.745154 IP 192.168.183.253.33774 > 192.168.183.254.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84033839 ecr 0,nop,wscale 6], length 0 2017-04-21 20:07:02.745098 IP 192.168.183.253.33774 > 192.168.183.254.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84034089 ecr 0,nop,wscale 6], length 0 2017-04-21 20:07:04.747111 IP 192.168.183.253.33774 > 192.168.183.254.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84034590 ecr 0,nop,wscale 6], length 0 2017-04-21 20:07:08.756022 IP 192.168.183.253.33774 > 192.168.183.254.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84035592 ecr 0,nop,wscale 6], length 0 2017-04-21 20:07:16.767457 IP 192.168.183.253.33774 > 192.168.183.254.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84037596 ecr 0,nop,wscale 6], length 0 2017-04-21 20:07:32.778145 IP 192.168.183.253.33774 > 192.168.183.254.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84041600 ecr 0,nop,wscale 6], length 0 2017-04-21 20:08:04.829078 IP 192.168.183.253.33774 > 192.168.183.254.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84049616 ecr 0,nop,wscale 6], length 0and from
sudo tcpdump -n -tttt -i eth0 port 22 | grep -v 192.168.0.47(actually 192.168.0.47 is my computer using ssh to 192.168.183.254 and 192.168.183.253 using another router to this net)2017-04-21 20:07:01.745195 IP 192.168.183.253.33774 > 192.168.0.16.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84033839 ecr 0,nop,wscale 6], length 0 2017-04-21 20:07:02.745136 IP 192.168.183.253.33774 > 192.168.0.16.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84034089 ecr 0,nop,wscale 6], length 0 2017-04-21 20:07:04.747139 IP 192.168.183.253.33774 > 192.168.0.16.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84034590 ecr 0,nop,wscale 6], length 0 2017-04-21 20:07:08.756068 IP 192.168.183.253.33774 > 192.168.0.16.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84035592 ecr 0,nop,wscale 6], length 0 2017-04-21 20:07:16.767486 IP 192.168.183.253.33774 > 192.168.0.16.22: Flags [S], seq 2118693960, win 29200, options [mss 1460,sackOK,TS val 84037596 ecr 0,nop,wscale 6], length 0-
 Doug Smythies about 7 yearsWe (or at least I) can not answer without the overall context of your entire iptables rule set. Edit your question adding the outputs for
Doug Smythies about 7 yearsWe (or at least I) can not answer without the overall context of your entire iptables rule set. Edit your question adding the outputs forsudo iptables -v -x -n -Landsudo iptables -t nat -v -x -n -L. In particular I am looking for your SNAT rule (or MASQUARADE rule, but for static IP addresses I'd suggest SNAT), and your default policies. Oh, and why just FORWARD for the NEW state? Always forward. -
 Doug Smythies about 7 yearsI'd suggest using tcpdump (or wireshark, if you prefer) to observe actual packet flow to help narrow down the issue. Also, perhaps, add some more logging rules to your iptables rule set, just while debugging. I see now why the "NEW" state only, because there was also a RELATED,ESTABLISHED rule, covering the not NEW case.
Doug Smythies about 7 yearsI'd suggest using tcpdump (or wireshark, if you prefer) to observe actual packet flow to help narrow down the issue. Also, perhaps, add some more logging rules to your iptables rule set, just while debugging. I see now why the "NEW" state only, because there was also a RELATED,ESTABLISHED rule, covering the not NEW case. -
pallago about 7 yearsHello and thank you for the replies. Actually I am trying to connect via ssh myuser@ubuntu-fw - corresponding to [email protected]
-
 Doug Smythies about 7 yearsYes, but it is not obvious to me what is wrong, thus the suggestion about using tcpdump to help. i.e. on ubuntu-fw:
Doug Smythies about 7 yearsYes, but it is not obvious to me what is wrong, thus the suggestion about using tcpdump to help. i.e. on ubuntu-fw:sudo tcpdump -n -tttt -i eth2 port 22andsudo tcpdump -n -tttt -i eth0 port 22. -
pallago about 7 yearsDear Dough, just an idea which came up to my mind. I also use another router between 192.168.0.0 and 192.168.183.0. Maybe thats the reason, because 192.168.183.254 is not the gateway in 192.168.0.16. I will check this.
-