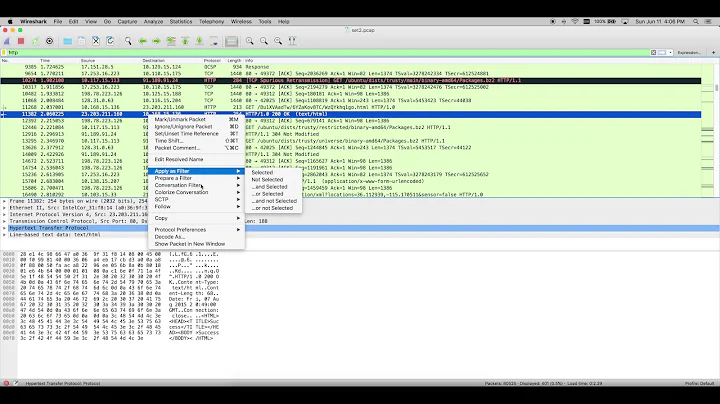
Best way to analyze pcap files from Wireshark?
23,649
by source address
tshark -T fields -e ip.src -r somefile.pcap
by dest address
tshark -T fields -e ip.dst -r somefile.pcap
pipe either of those to | sort | uniq -c | sort -n | tail -50
you can get the top src/dst pairs with
tshark -T fields -e ip.src -e ip.dst -r somefile.pcap
To get a list of fields you can work with
tshark -G fields
(warning, wireshark has an overwhelming list of fields)
Related videos on Youtube
Author by
Michael
Updated on September 18, 2022Comments
-
Michael over 1 year
I've got 50-100MB pcap files captured from Wireshark and need to analyze where most of the traffic is going to/coming from.
What's the best way of doing this? Ideally I'd like to end up with an Excel csv file showing the top 50 or so IP addresses so I can sort and analyze.
-
 Admin almost 13 yearsnot in front of my linux box to try but is there a way to have tshark analyze all the files at once? -r somefile.pcap somefile2.pcap somefile3.pcap?
Admin almost 13 yearsnot in front of my linux box to try but is there a way to have tshark analyze all the files at once? -r somefile.pcap somefile2.pcap somefile3.pcap?
-