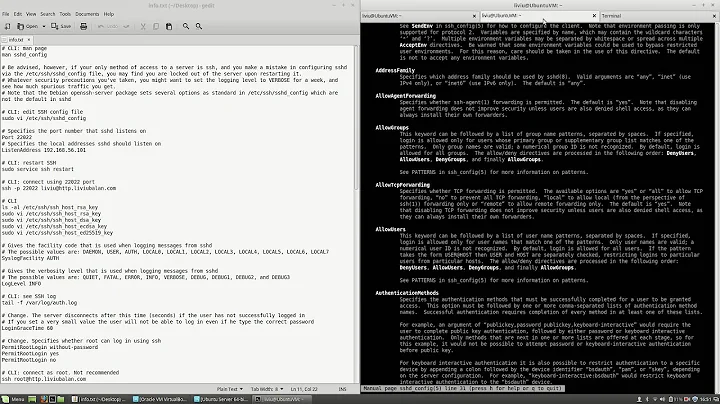
Can't get sshd_config Match User to work
See @Otheus comments for the solution - in order to have one user use key login and another user (pwtest) password login, the relevant parameters in /etc/ssh/sshd_config are below. Previously I had UsePAM no and when pwtest entered their password they would get the message: Permission denied, please try again.
ChallengeResponseAuthentication no
PasswordAuthentication no
UsePAM yes
UsePrivilegeSeparation sandbox # default setting
Match User pwtest
PasswordAuthentication yes
Related videos on Youtube
Fordpark
Haven't learned a computer language before, was reading brettterpstra.com where Brett recommended Python so here I am. I seemed to have taken a detour into regular expressions.
Updated on September 18, 2022Comments
-
 Fordpark over 1 year
Fordpark over 1 yearAm exploring ssh on my el capitan laptop and have managed to get key-based login to work (using an account called adminuser). I now want to see if I can get another administrator account (called pwtest) to work using password-based login.
I've just discovered Match User and added it sshd_config but when I ssh [email protected] and then enter the password I just get "Permission denied, please try again."
sshd_config:
# $OpenBSD: sshd_config,v 1.95 2015/04/27 21:42:48 djm Exp $ # This is the sshd server system-wide configuration file. See # sshd_config(5) for more information. # This sshd was compiled with PATH=/usr/bin:/bin:/usr/sbin:/sbin # The strategy used for options in the default sshd_config shipped with # OpenSSH is to specify options with their default value where # possible, but leave them commented. Uncommented options override the # default value. # See sshd_config(5) for details on setting the Port and Listen values on Mac OS X #Port 22 #AddressFamily any #ListenAddress 0.0.0.0 #ListenAddress :: # The default requires explicit activation of protocol 1 #Protocol 2 # HostKey for protocol version 1 #HostKey /etc/ssh/ssh_host_key # HostKeys for protocol version 2 #HostKey /etc/ssh/ssh_host_rsa_key #HostKey /etc/ssh/ssh_host_dsa_key #HostKey /etc/ssh/ssh_host_ecdsa_key #HostKey /etc/ssh/ssh_host_ed25519_key # Lifetime and size of ephemeral version 1 server key #KeyRegenerationInterval 1h #ServerKeyBits 1024 # Ciphers and keying #RekeyLimit default none # Logging # obsoletes QuietMode and FascistLogging SyslogFacility AUTHPRIV #LogLevel INFO # Authentication: #LoginGraceTime 2m #PermitRootLogin no #StrictModes yes #MaxAuthTries 6 #MaxSessions 10 #RSAAuthentication yes #PubkeyAuthentication yes # The default is to check both .ssh/authorized_keys and .ssh/authorized_keys2 # but this is overridden so installations will only check .ssh/authorized_keys AuthorizedKeysFile .ssh/authorized_keys #AuthorizedPrincipalsFile none #AuthorizedKeysCommand none #AuthorizedKeysCommandUser nobody # For this to work you will also need host keys in /etc/ssh/ssh_known_hosts #RhostsRSAAuthentication no # similar for protocol version 2 #HostbasedAuthentication no # Change to yes if you don't trust ~/.ssh/known_hosts for # RhostsRSAAuthentication and HostbasedAuthentication #IgnoreUserKnownHosts no # Don't read the user's ~/.rhosts and ~/.shosts files #IgnoreRhosts yes # To disable tunneled clear text passwords both PasswordAuthentication and # ChallengeResponseAuthentication must be set to "no". PasswordAuthentication no #PermitEmptyPasswords no # Change to no to disable s/key passwords ChallengeResponseAuthentication no # Kerberos options #KerberosAuthentication no #KerberosOrLocalPasswd yes #KerberosTicketCleanup yes #KerberosGetAFSToken no # GSSAPI options #GSSAPIAuthentication no #GSSAPICleanupCredentials yes #GSSAPIStrictAcceptorCheck yes #GSSAPIKeyExchange no # Set this to 'yes' to enable PAM authentication, account processing, # and session processing. If this is enabled, PAM authentication will # be allowed through the ChallengeResponseAuthentication and # PasswordAuthentication. Depending on your PAM configuration, # PAM authentication via ChallengeResponseAuthentication may bypass # the setting of "PermitRootLogin without-password". # If you just want the PAM account and session checks to run without # PAM authentication, then enable this but set PasswordAuthentication # and ChallengeResponseAuthentication to 'no'. # Also, PAM will deny null passwords by default. If you need to allow # null passwords, add the " nullok" option to the end of the # securityserver.so line in /etc/pam.d/sshd. UsePAM no #AllowAgentForwarding yes #AllowTcpForwarding yes #GatewayPorts no #X11Forwarding no #XauthLocation xauth # Default is to search $PATH (set by launchd(8)). It is recommended that a full path be provided. #X11DisplayOffset 10 #X11UseLocalhost yes #PermitTTY yes #PrintMotd yes #PrintLastLog yes #TCPKeepAlive yes #UseLogin no UsePrivilegeSeparation sandbox # Default for new installations. #PermitUserEnvironment no #Compression delayed #ClientAliveInterval 0 #ClientAliveCountMax 3 #UseDNS no #PidFile /var/run/sshd.pid #MaxStartups 10:30:100 #PermitTunnel no #ChrootDirectory none #VersionAddendum none # pass locale information AcceptEnv LANG LC_* # no default banner path #Banner none # override default of no subsystems Subsystem sftp /usr/libexec/sftp-server # Example of overriding settings on a per-user basis #Match User anoncvs # X11Forwarding no # AllowTcpForwarding no # PermitTTY no # ForceCommand cvs server Match User pwtest PasswordAuthentication yesssh -vv [email protected] output:
Unknown-58-b0-35-63-5c-67:~ davidpark$ ssh -vv [email protected] OpenSSH_6.9p1, LibreSSL 2.1.7 debug1: Reading configuration data /etc/ssh/ssh_config debug1: /etc/ssh/ssh_config line 20: Applying options for * debug2: ssh_connect: needpriv 0 debug1: Connecting to dplaptop.local [fe80::5ab0:35ff:fe63:5c67%en1] port 22. debug1: Connection established. debug1: key_load_public: No such file or directory debug1: identity file /Users/davidpark/.ssh/id_rsa type -1 debug1: key_load_public: No such file or directory debug1: identity file /Users/davidpark/.ssh/id_rsa-cert type -1 debug1: key_load_public: No such file or directory debug1: identity file /Users/davidpark/.ssh/id_dsa type -1 debug1: key_load_public: No such file or directory debug1: identity file /Users/davidpark/.ssh/id_dsa-cert type -1 debug1: key_load_public: No such file or directory debug1: identity file /Users/davidpark/.ssh/id_ecdsa type -1 debug1: key_load_public: No such file or directory debug1: identity file /Users/davidpark/.ssh/id_ecdsa-cert type -1 debug1: key_load_public: No such file or directory debug1: identity file /Users/davidpark/.ssh/id_ed25519 type -1 debug1: key_load_public: No such file or directory debug1: identity file /Users/davidpark/.ssh/id_ed25519-cert type -1 debug1: Enabling compatibility mode for protocol 2.0 debug1: Local version string SSH-2.0-OpenSSH_6.9 debug1: Remote protocol version 2.0, remote software version OpenSSH_6.9 debug1: match: OpenSSH_6.9 pat OpenSSH* compat 0x04000000 debug2: fd 5 setting O_NONBLOCK debug1: Authenticating to dplaptop.local:22 as 'pwtest' debug1: SSH2_MSG_KEXINIT sent debug1: SSH2_MSG_KEXINIT received debug2: kex_parse_kexinit: [email protected],ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group-exchange-sha1,diffie-hellman-group14-sha1,diffie-hellman-group1-sha1 debug2: kex_parse_kexinit: [email protected],[email protected],[email protected],ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521,[email protected],[email protected],[email protected],[email protected],[email protected],ssh-ed25519,ssh-rsa,ssh-dss debug2: kex_parse_kexinit: [email protected],aes128-ctr,aes192-ctr,aes256-ctr,[email protected],[email protected],arcfour256,arcfour128,aes128-cbc,3des-cbc,blowfish-cbc,cast128-cbc,aes192-cbc,aes256-cbc,arcfour,[email protected] debug2: kex_parse_kexinit: [email protected],aes128-ctr,aes192-ctr,aes256-ctr,[email protected],[email protected],arcfour256,arcfour128,aes128-cbc,3des-cbc,blowfish-cbc,cast128-cbc,aes192-cbc,aes256-cbc,arcfour,[email protected] debug2: kex_parse_kexinit: [email protected],[email protected],[email protected],[email protected],[email protected],[email protected],[email protected],hmac-sha2-256,hmac-sha2-512,hmac-sha1,[email protected],[email protected],[email protected],[email protected],hmac-md5,hmac-ripemd160,[email protected],hmac-sha1-96,hmac-md5-96 debug2: kex_parse_kexinit: [email protected],[email protected],[email protected],[email protected],[email protected],[email protected],[email protected],hmac-sha2-256,hmac-sha2-512,hmac-sha1,[email protected],[email protected],[email protected],[email protected],hmac-md5,hmac-ripemd160,[email protected],hmac-sha1-96,hmac-md5-96 debug2: kex_parse_kexinit: none,[email protected],zlib debug2: kex_parse_kexinit: none,[email protected],zlib debug2: kex_parse_kexinit: debug2: kex_parse_kexinit: debug2: kex_parse_kexinit: first_kex_follows 0 debug2: kex_parse_kexinit: reserved 0 debug2: kex_parse_kexinit: [email protected],ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group14-sha1 debug2: kex_parse_kexinit: ssh-rsa,ssh-dss,ecdsa-sha2-nistp256,ssh-ed25519 debug2: kex_parse_kexinit: [email protected],aes128-ctr,aes192-ctr,aes256-ctr,[email protected],[email protected] debug2: kex_parse_kexinit: [email protected],aes128-ctr,aes192-ctr,aes256-ctr,[email protected],[email protected] debug2: kex_parse_kexinit: [email protected],[email protected],[email protected],[email protected],[email protected],[email protected],[email protected],hmac-sha2-256,hmac-sha2-512,hmac-sha1 debug2: kex_parse_kexinit: [email protected],[email protected],[email protected],[email protected],[email protected],[email protected],[email protected],hmac-sha2-256,hmac-sha2-512,hmac-sha1 debug2: kex_parse_kexinit: none,[email protected] debug2: kex_parse_kexinit: none,[email protected] debug2: kex_parse_kexinit: debug2: kex_parse_kexinit: debug2: kex_parse_kexinit: first_kex_follows 0 debug2: kex_parse_kexinit: reserved 0 debug1: kex: server->client [email protected] <implicit> none debug1: kex: client->server [email protected] <implicit> none debug1: expecting SSH2_MSG_KEX_ECDH_REPLY debug1: Server host key: ecdsa-sha2-nistp256 SHA256:pZ9I3OlB5kUmeKHq4PWADSigAPIAmO7VWK10Pn5Vau4 debug1: Host 'dplaptop.local' is known and matches the ECDSA host key. debug1: Found key in /Users/davidpark/.ssh/known_hosts:1 debug2: set_newkeys: mode 1 debug1: SSH2_MSG_NEWKEYS sent debug1: expecting SSH2_MSG_NEWKEYS debug2: set_newkeys: mode 0 debug1: SSH2_MSG_NEWKEYS received debug1: Roaming not allowed by server debug1: SSH2_MSG_SERVICE_REQUEST sent debug2: service_accept: ssh-userauth debug1: SSH2_MSG_SERVICE_ACCEPT received debug2: key: /Users/davidpark/.ssh/id_rsa (0x0), debug2: key: /Users/davidpark/.ssh/id_dsa (0x0), debug2: key: /Users/davidpark/.ssh/id_ecdsa (0x0), debug2: key: /Users/davidpark/.ssh/id_ed25519 (0x0), debug1: Authentications that can continue: publickey,password debug1: Next authentication method: publickey debug1: Trying private key: /Users/davidpark/.ssh/id_rsa debug2: we sent a publickey packet, wait for reply debug1: Authentications that can continue: publickey,password debug1: Trying private key: /Users/davidpark/.ssh/id_dsa debug1: Trying private key: /Users/davidpark/.ssh/id_ecdsa debug1: Trying private key: /Users/davidpark/.ssh/id_ed25519 debug2: we did not send a packet, disable method debug1: Next authentication method: password [email protected]'s password: debug2: we sent a password packet, wait for reply debug1: Authentications that can continue: publickey,password Permission denied, please try again. [email protected]'s password: debug2: we sent a password packet, wait for reply debug1: Authentications that can continue: publickey,password Permission denied, please try again. [email protected]'s password: debug2: we sent a password packet, wait for reply debug1: Authentications that can continue: publickey,password debug2: we did not send a packet, disable method debug1: No more authentication methods to try. Permission denied (publickey,password).ssh_config:
# $OpenBSD: ssh_config,v 1.28 2013/09/16 11:35:43 sthen Exp $ # This is the ssh client system-wide configuration file. See # ssh_config(5) for more information. This file provides defaults for # users, and the values can be changed in per-user configuration files # or on the command line. # Configuration data is parsed as follows: # 1. command line options # 2. user-specific file # 3. system-wide file # Any configuration value is only changed the first time it is set. # Thus, host-specific definitions should be at the beginning of the # configuration file, and defaults at the end. # Site-wide defaults for some commonly used options. For a comprehensive # list of available options, their meanings and defaults, please see the # ssh_config(5) man page. # Apple: Host * SendEnv LANG LC_* # AskPassGUI yes # ForwardAgent no # ForwardX11 no # RhostsRSAAuthentication no # RSAAuthentication yes # PasswordAuthentication no # HostbasedAuthentication yes # GSSAPIAuthentication no # GSSAPIDelegateCredentials no # BatchMode no # CheckHostIP yes # AddressFamily any # ConnectTimeout 0 # StrictHostKeyChecking ask # IdentityFile ~/.ssh/identity # IdentityFile ~/.ssh/id_rsa # IdentityFile ~/.ssh/id_dsa # Port 22 # Protocol 2,1 # Cipher 3des # Ciphers aes128-ctr,aes192-ctr,aes256-ctr,arcfour256,arcfour128,aes128-cbc,3des-cbc # MACs hmac-md5,hmac-sha1,[email protected],hmac-ripemd160 # EscapeChar ~ # Tunnel no # TunnelDevice any:any # PermitLocalCommand no # VisualHostKey no # ProxyCommand ssh -q -W %h:%p gateway.example.com # RekeyLimit 1G 1hsystem.log content:
Nov 9 15:07:28 Unknown-58-b0-35-63-5c-67 sshd[1868]: Failed password for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49985 ssh2 Nov 9 15:07:51 --- last message repeated 2 times --- Nov 9 15:07:51 Unknown-58-b0-35-63-5c-67 sshd[1868]: Connection closed by fe80::5ab0:35ff:fe63:5c67%en1 [preauth] Nov 9 15:07:51 Unknown-58-b0-35-63-5c-67 com.apple.xpc.launchd[1] (com.openssh.sshd.CC0FA77D-7484-4138-96BA-7BC748771FA1[1868]): Service exited with abnormal code: 255Following @Otheus suggestions:
When I use a plain vanilla sshd_config file i.e.
sudo /usr/sbin/sshd -D -d -f /etc/ssh/sshd_config.plain -p 2020I can successfullyssh -p 2020 [email protected]- see debug output below:... debug1: expecting SSH2_MSG_KEX_ECDH_INIT [preauth] debug1: SSH2_MSG_NEWKEYS sent [preauth] debug1: expecting SSH2_MSG_NEWKEYS [preauth] debug1: SSH2_MSG_NEWKEYS received [preauth] debug1: KEX done [preauth] debug1: userauth-request for user pwtest service ssh-connection method none [preauth] debug1: attempt 0 failures 0 [preauth] debug1: PAM: initializing for "pwtest" debug1: PAM: setting PAM_RHOST to "fe80::5ab0:35ff:fe63:5c67%en1" debug1: userauth-request for user pwtest service ssh-connection method publickey [preauth] debug1: attempt 1 failures 0 [preauth] debug1: temporarily_use_uid: 503/20 (e=0/0) debug1: trying public key file /Users/pwtest/.ssh/authorized_keys debug1: Could not open authorized keys '/Users/pwtest/.ssh/authorized_keys': No such file or directory debug1: restore_uid: 0/0 Failed publickey for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49288 ssh2: RSA SHA256:Y4oh+ZwNsE9hrnD+kCGYUkl48TypV0oQxXi9osTozE4 debug1: audit_event: unhandled event 6 debug1: userauth-request for user pwtest service ssh-connection method keyboard-interactive [preauth] debug1: attempt 2 failures 1 [preauth] debug1: keyboard-interactive devs [preauth] debug1: auth2_challenge: user=pwtest devs= [preauth] debug1: kbdint_alloc: devices 'pam' [preauth] debug1: auth2_challenge_start: trying authentication method 'pam' [preauth] Postponed keyboard-interactive for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49288 ssh2: RSA SHA256:Y4oh+ZwNsE9hrnD+kCGYUkl48TypV0oQxXi9osTozE4 [preauth] debug1: do_pam_account: called debug1: PAM: num PAM env strings 2 Postponed keyboard-interactive/pam for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49288 ssh2 [preauth] debug1: do_pam_account: called Accepted keyboard-interactive/pam for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49288 ssh2 debug1: monitor_child_preauth: pwtest has been authenticated by privileged process debug1: monitor_read_log: child log fd closed debug1: PAM: establishing credentials User child is on pid 473 debug1: PAM: establishing credentials debug1: permanently_set_uid: 503/20 debug1: ssh_packet_set_postauth: called debug1: Entering interactive session for SSH2. debug1: server_init_dispatch_20 debug1: server_input_channel_open: ctype session rchan 0 win 1048576 max 16384 debug1: input_session_request debug1: channel 0: new [server-session] debug1: session_new: session 0 debug1: session_open: channel 0 debug1: session_open: session 0: link with channel 0 debug1: server_input_channel_open: confirm session debug1: server_input_global_request: rtype [email protected] want_reply 0 debug1: server_input_channel_req: channel 0 request pty-req reply 1 debug1: session_by_channel: session 0 channel 0 debug1: session_input_channel_req: session 0 req pty-req debug1: Allocating pty. debug1: session_new: session 0 debug1: session_pty_req: session 0 alloc /dev/ttys002 debug1: server_input_channel_req: channel 0 request env reply 0 debug1: session_by_channel: session 0 channel 0 debug1: session_input_channel_req: session 0 req env debug1: server_input_channel_req: channel 0 request shell reply 1 debug1: session_by_channel: session 0 channel 0 debug1: session_input_channel_req: session 0 req shell Starting session: shell on ttys002 for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49288 debug1: Setting controlling tty using TIOCSCTTY.But when I use my modified ssh_config
sudo /usr/sbin/sshd -D -d -f /etc/ssh/sshd_config -p 2020,ssh -p 2020 [email protected]doesn't work - debug output below:... debug1: Client protocol version 2.0; client software version OpenSSH_6.9 debug1: match: OpenSSH_6.9 pat OpenSSH* compat 0x04000000 debug1: Enabling compatibility mode for protocol 2.0 debug1: Local version string SSH-2.0-OpenSSH_6.9 debug1: permanently_set_uid: 75/75 [preauth] debug1: list_hostkey_types: ssh-rsa,ssh-dss,ecdsa-sha2-nistp256,ssh-ed25519 [preauth] debug1: SSH2_MSG_KEXINIT sent [preauth] debug1: SSH2_MSG_KEXINIT received [preauth] debug1: kex: client->server [email protected] <implicit> none [preauth] debug1: kex: server->client [email protected] <implicit> none [preauth] debug1: expecting SSH2_MSG_KEX_ECDH_INIT [preauth] debug1: SSH2_MSG_NEWKEYS sent [preauth] debug1: expecting SSH2_MSG_NEWKEYS [preauth] debug1: SSH2_MSG_NEWKEYS received [preauth] debug1: KEX done [preauth] debug1: userauth-request for user pwtest service ssh-connection method none [preauth] debug1: attempt 0 failures 0 [preauth] debug1: user pwtest matched 'User pwtest' at line 146 debug1: userauth-request for user pwtest service ssh-connection method publickey [preauth] debug1: attempt 1 failures 0 [preauth] debug1: temporarily_use_uid: 503/20 (e=0/0) debug1: trying public key file /Users/pwtest/.ssh/authorized_keys debug1: Could not open authorized keys '/Users/pwtest/.ssh/authorized_keys': No such file or directory debug1: restore_uid: 0/0 Failed publickey for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49290 ssh2: RSA SHA256:Y4oh+ZwNsE9hrnD+kCGYUkl48TypV0oQxXi9osTozE4 debug1: audit_event: unhandled event 6 debug1: userauth-request for user pwtest service ssh-connection method password [preauth] debug1: attempt 2 failures 1 [preauth] Failed password for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49290 ssh2 debug1: userauth-request for user pwtest service ssh-connection method password [preauth] debug1: attempt 3 failures 2 [preauth] Failed password for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49290 ssh2 debug1: userauth-request for user pwtest service ssh-connection method password [preauth] debug1: attempt 4 failures 3 [preauth] Failed password for pwtest from fe80::5ab0:35ff:fe63:5c67%en1 port 49290 ssh2 Connection closed by fe80::5ab0:35ff:fe63:5c67%en1 [preauth] debug1: do_cleanup [preauth] debug1: monitor_read_log: child log fd closed debug1: do_cleanup debug1: Killing privsep child 497 debug1: audit_event: unhandled event 12-
Otheus over 8 yearsDo you know for certain that ssh works for that particular user with that particular password? Try the following: Start with a super-vanilla default sshd_config file -- name it
/etc/ssh/sshd_config.plainand start a new sshd with:/usr/sbin/sshd -f /etc/ssh/sshd_config.plain -p 2020. Now connect to it on port 2020 withssh -p 2020 pwtest@localhost. Does the password work? If not, the problem might be up the authentication chain (PAM, MacOS, or the password itself). If so, then this time, run sshd on your new configuration and with-Doption so you can see what it thinks is happening -
 Fordpark over 8 yearsThanks @Otheus, managed to login using the plain vanilla sshd_config.plain and have pasted the debug info from my modified sshd_config i.e.
Fordpark over 8 yearsThanks @Otheus, managed to login using the plain vanilla sshd_config.plain and have pasted the debug info from my modified sshd_config i.e./usr/sbin/sshd -D -d -f /etc/ssh/sshd_config -p 2020- does anything catch your eye? -
Otheus over 8 yearsYour vanilla installation is using
PAM, and your modified version is not. Now, I tested the posted configuration on a Linux box, but it does not know what to do with "UsePrivilegeSeparation" directive. Does your vanilla sshd configuration containUsePrivilegeSeparation sandbox? I can see how disabling PAM while instituting Privilege Spearation might be a problem: The latter has no way of (securely) authenticating using a password. But the BSD man page doesn't have enough details for me to be sure. -
 Fordpark over 8 yearsThanks @Otheus, in my modified sshd_cofig:
Fordpark over 8 yearsThanks @Otheus, in my modified sshd_cofig:UsePrivilegeSeparation sandbox usePAM noand when I change usePAM to yes, pwtest can successfully login using a password and adminuser can login with a key (and it doesn't ask for a password if it can't find the key) which is what I was looking for.
-
-
MrMas over 3 yearsI found that I adding
Match User ...failed when I put it in the middle of the file but worked when I added it to the end of the file.