Can I Deploy a batch file with Group Policy to run as administrator?
Solution 1
Yes, you can deploy batch files via Group Policy that will run under the context of Local System. A very common way of doing so is Computer Startup scripts. (As opposed to User Logon scripts.)
Also, this is probably the worst possible way imaginable of blocking Facebook.

From http://technet.microsoft.com/en-us/library/cc770556.aspx
Startup scripts are run under the Local System account, and they have the full rights that are associated with being able to run under the Local System account.
The Local System account is essentially even more powerful than Administrator.
Solution 2
I know this is an old post, but what the heck. I'm not sure what's up with the naysayers. Pointing the objectionable domain to the local loopback address seems like a perfectly fine way to block access. It'll prevent DNS from returning the real address of the Facebook site, and if the user is not a local administrator, even if they know about the hosts file, which they probabaly don't, they won't have permissions to change it.
The problem I see with your approach is that if you got it running, you'll be appending that same line to your hosts file over and over again indefinitely.
If you're going to do this, you should have a script that looks for that line in the file, and only appends it if it doesn't already exist (and perhaps edits it if it doesn't say what you want it to).
Finally, running as the local SYSTEM account won't work if the script needs network access, unless you grant adequate permissions to the AD "Domain Computers" group and are prepared to do a little debugging.
Solution 3
You might want to change this to:
0.0.0.0 www.facebook.com
If you use the loopback address you'll have to wait for a timeout unless there is a local web server.
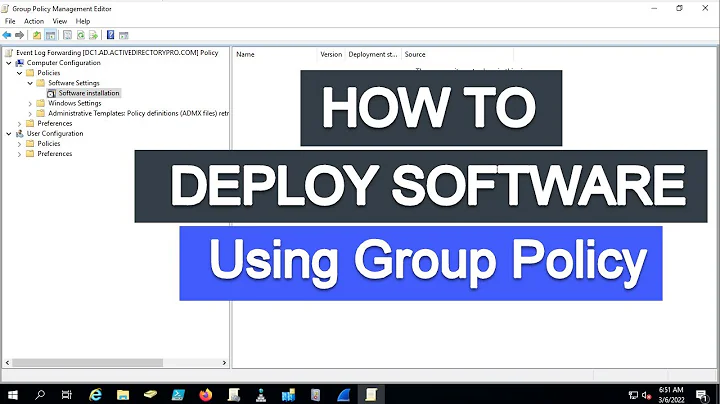
Related videos on Youtube
pgunston
Web Developer / Desktop Support / System Administrator
Updated on September 18, 2022Comments
-
 pgunston over 1 year
pgunston over 1 yearI have created a batch script which will block Facebook by amending the
hostsfile in this locationC:\windows\system32\drivers\etc\hostsThis is the contents of the batch file:
@echo off echo 127.0.0.1 www.facebook.com >> C:\windows\system32\drivers\etc\hosts exitI have tested this batch file on my local machine and it works however, it will only work when I run it as Administrator.
Is it possible to deploy this batch file to all computers on my network, running as administrator using Group Policy?
I am using Windows Server 2012.
-
 pgunston over 9 yearsThanks, The reason I want to use Group Policy to block facebook is because I need granularity. I want to only block it for particular users.
pgunston over 9 yearsThanks, The reason I want to use Group Policy to block facebook is because I need granularity. I want to only block it for particular users. -
 030 over 9 years@pgunston this information would clarify the question.
030 over 9 years@pgunston this information would clarify the question. -
 pgunston over 9 yearsI achieved my goal by using Symantec Endpoint Protection Management Server rather than using DNS.
pgunston over 9 yearsI achieved my goal by using Symantec Endpoint Protection Management Server rather than using DNS. -
Jonas Lear over 8 yearsI know I'm a year late, just wanted to iterate a bit on what Ryan said. This is the worst way of blocking Facebook because it relies on a lot and only works on IE. So if someone were to download another browser, that hosts file becomes pointless. However, if your network is locked down, everyone is domain user and downloads of Chrome are disabled, and you have all proxies blocked, then you should be fine, lol.
-
 Craig Tullis about 7 yearsJonas, that completely wrong. The DNS client on every operating system looks at the hosts file before running a query against the configured DNS servers. Every program running on the operating system, certainly all of the web browsers, use the operating system's DNS client to find hosts on the network. This is not just an IE fix, it will affect every program running on the machine that uses DNS normally.
Craig Tullis about 7 yearsJonas, that completely wrong. The DNS client on every operating system looks at the hosts file before running a query against the configured DNS servers. Every program running on the operating system, certainly all of the web browsers, use the operating system's DNS client to find hosts on the network. This is not just an IE fix, it will affect every program running on the machine that uses DNS normally. -
 Craig Tullis about 7 yearsAre you sure about that? If you ping 127.0.0.1, it will respond immediately UNLESS that mechanism has been subverted somehow on your machine or your network.
Craig Tullis about 7 yearsAre you sure about that? If you ping 127.0.0.1, it will respond immediately UNLESS that mechanism has been subverted somehow on your machine or your network. -
 Dylan Knoll about 7 yearsYou're listening for ping on localhost, but likely not for http traffic. Try again with http-ping or ping an unreachable host.
Dylan Knoll about 7 yearsYou're listening for ping on localhost, but likely not for http traffic. Try again with http-ping or ping an unreachable host. -
 Craig Tullis about 7 yearsThat might be a fair point. But if the objective is to block access to an objectionable website, why worry about a timeout? I have a ready answer, of course, which is that you get Facebook assets (tracking scripts, primarily) injected into other web pages all over the web, and a timeout accessing the facebook.com domain would impact the load time of every such page.
Craig Tullis about 7 yearsThat might be a fair point. But if the objective is to block access to an objectionable website, why worry about a timeout? I have a ready answer, of course, which is that you get Facebook assets (tracking scripts, primarily) injected into other web pages all over the web, and a timeout accessing the facebook.com domain would impact the load time of every such page. -
 Dylan Knoll about 7 yearsWhy ask the question if you already know the answer? ;)
Dylan Knoll about 7 yearsWhy ask the question if you already know the answer? ;) -
 Craig Tullis about 7 yearshaha, well, one the one hand I don't care if they experience a timeout trying to access something I'm blocking. On the other hand... the law of unintended consequences. ;)
Craig Tullis about 7 yearshaha, well, one the one hand I don't care if they experience a timeout trying to access something I'm blocking. On the other hand... the law of unintended consequences. ;) -
 Dylan Knoll about 7 yearsYes, even this site has Facebook assets. My responses here and elsewhere are based upon experience and research... those two tend to mitigate unintended consequences.
Dylan Knoll about 7 yearsYes, even this site has Facebook assets. My responses here and elsewhere are based upon experience and research... those two tend to mitigate unintended consequences. -
 Craig Tullis about 7 yearsSo... going back to the research issue. You will definitely experience a timeout trying to reach an IP address that doesn't respond immediately. Trying to reach a specific non-existent service on a live host, however, should result in an immediate rejection, as the host will explicitly refuse the connection. Unless the host is just dropping packets, of course, but it's unlikely that an edge device other than a firewall is doing that.
Craig Tullis about 7 yearsSo... going back to the research issue. You will definitely experience a timeout trying to reach an IP address that doesn't respond immediately. Trying to reach a specific non-existent service on a live host, however, should result in an immediate rejection, as the host will explicitly refuse the connection. Unless the host is just dropping packets, of course, but it's unlikely that an edge device other than a firewall is doing that. -
 Dylan Knoll about 7 yearsTest it and let me know... the answer may surprise you! :)
Dylan Knoll about 7 yearsTest it and let me know... the answer may surprise you! :) -
 Craig Tullis about 7 yearsInformally (as tests go), I just tried 127.0.0.1 using a web browser, on my machine which is not currently configured as a development web server, and the ERR_CONNECTION_REFUSED result was immediate. To be fair, I've actually seen and done this in the past using hosts files that were intentionally full of objectionable (porn, gambling, etc.) dns names.
Craig Tullis about 7 yearsInformally (as tests go), I just tried 127.0.0.1 using a web browser, on my machine which is not currently configured as a development web server, and the ERR_CONNECTION_REFUSED result was immediate. To be fair, I've actually seen and done this in the past using hosts files that were intentionally full of objectionable (porn, gambling, etc.) dns names. -
 Dylan Knoll about 7 yearsImmediate by your own sight, or 0ms?
Dylan Knoll about 7 yearsImmediate by your own sight, or 0ms? -
raja about 7 yearsWelcome to serverfault. There are a lot of "head scratching" answers here.
-
 Craig Tullis about 7 yearsAs there are everywhere, I suppose. And thank you for the welcome. ;-)
Craig Tullis about 7 yearsAs there are everywhere, I suppose. And thank you for the welcome. ;-)