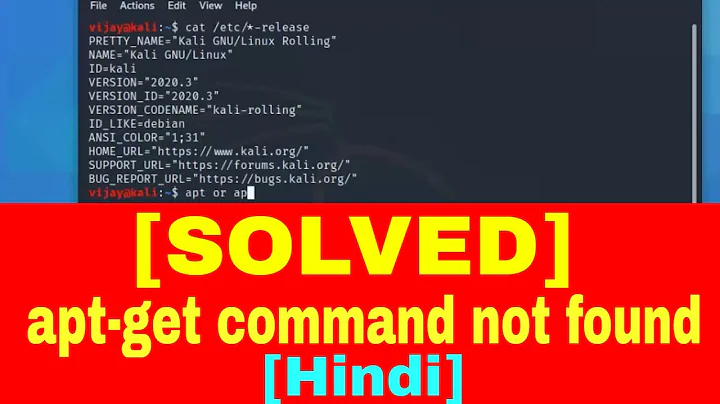
Can I get a virus by using "sudo apt-get install"?
Solution 1
apt on a default Ubuntu system will be very unlikely to get viruses. However, it doesn't mean it isn't possible:
-
Malicious PPA
One of the features of APT is the ability for admins to add Personal Package Archives (PPAs) or other software sources to the APT cache. These third-party APT sources are not necessarily trusted, and may carry viruses. However, it would take an intentional action of the machine's admin to add one of these infected sources, making it rather hard for one to add itself. -
Hacked Repository
In theory, a software repository may be hacked by a malicious party, causing downloaded.debfiles to potentially carry malicious payloads. However, official software repositories are very carefully watched and security for these repositories is pretty tight. A hacker would be hard-pressed to take down one of the official Ubuntu software sources, but third-party software sources (see above) may be compromised a lot easier. -
Active MITM/Network Attacks
If a network is compromised higher up (by, say, your ISP), it is possible to get a virus from official software sources. However, an attack of this caliber would require an extreme amount of effort and the ability to Man-In-The-Middle many sites, including GPG key distribution servers and the official repos. -
Poorly Written/Malicious Code
Vulnerabilities do exist in open source, peer-reviewed, and maintained code. While these things aren't technically considered "viruses" by definition, certain exploits hidden or never revealed in the code could allow a malicious attacker to place a virus on or pwn your system. One example of this type of issue would be Heartbleed from OpenSSL, or the much-more-recent Dirty CoW. Note that programs from theuniverseormultiverserepos are potential threats of this caliber, as explained here.
apt (due to its importance on Linux systems) is pretty heavily guarded against almost all of these types of attacks on both the client and server side. While they are possible, an admin who knows what they're doing and knows how to read error logs will be able to prevent any of these attacks from taking place.
Additionally, apt also enforces signature verification to ensure that the files downloaded are legitimate (and are downloaded correctly), making it even harder to sneak malware through apt, as these digital signatures cannot be faked.
As for responding to a malware infection incident, the absolute easiest path is to burn the system to the ground and start again from a recent (and known-clean) backup. Due to the nature of Linux, it can be very easy for malware to manifest itself so deep in the system that it can never be found or extracted. However, packages like clamav and rkhunter can be used to scan a system for infections.
Solution 2
apt-get will only install from the official Ubuntu repositories which are checked or from repositories you've added to your sources. If you add every repository you come across, you might end up installing something nasty. Don't do that.
Solution 3
Files downloaded by sudo apt-get are compared to a check sum / hash sum for that file to ensure it hasn't been tampered with and is virus free.
Indeed the problems people have encountered when you google "sudo apt get hash sum" is too much security against viruses.
Linux is not completely virus free by any means however incidents are probably 1000 times less than windows.
Then again judging by my screen name I might be biased :)
Comment on November 28, 2017 mentions how Windows has 1,000 more workstations than Linux so why bother hacking Linux. It brings up the fact Linux is running on all 500 of the faster Super-Computers now and most Webservers are running Linux which makes it the best way to hack all the Windows workstations that attach to the internet.
Google Chrome, Android and Windows 10 gives users ample opportunity to give away their privacy and probably some security at the same time.
Solution 4
Although apt-get will only install from the official Ubuntu repositories, it does not guarantee 100% the packaged you got is clean.
If the repository is hacked, hacker may inject harm code into packages. Linux Mint server as an example was hacked, and hacker injected malware into their ISO files. http://www.theregister.co.uk/2016/02/21/linux_mint_hacked_malwareinfected_isos_linked_from_official_site/
Related videos on Youtube
Tomas
Updated on September 18, 2022Comments
-
Tomas over 1 year
I would like to make sure it's safe to download software using
sudo apt-get install. Are the packages scanned somewhere? Are all packages downloaded using this command virus free?If there is no guarantee that they are not virus free, after installing a package that contains virus, would the attacker be fully able to control my machine? Is there any way I can check all the packages that were installed on my computer by me? (not by the system automatically. I would like to filter them to see all the packages that were installed by me manually, not by the system.)
-
 Wildcard over 7 yearsThe question is valid, but contains misconceptions about viruses. A blacklist as the only means of avoiding infection is a very bad method, despite its ubiquity thanks to Windows' inverted security model. "Scanning" a software package is a horrible way to prevent malicious actions.
Wildcard over 7 yearsThe question is valid, but contains misconceptions about viruses. A blacklist as the only means of avoiding infection is a very bad method, despite its ubiquity thanks to Windows' inverted security model. "Scanning" a software package is a horrible way to prevent malicious actions. -
jokerdino over 7 yearsTomas, your comment was removed by a moderator. Please do NOT post it over and over again.
-
-
 WinEunuuchs2Unix over 7 yearsEven NSA, DNC and bitcoin exchanges have been hacked recently. I think it's safe to say Ubuntu repositories are 99.99999% virus free which is the spirit of the question and our answers. Indeed no one has actually come forth with a Ubuntu virus in this Q&A. There is the long standing Linux virus/malware which KASLR fixes that most people don't even know about and I only read about on a non-MSM alternate website that is non-Linux based and solely global news based. I would like to say Linux has far fewer viruses than Windows and Ubuntu Update is secure. However as always be careful of websites.
WinEunuuchs2Unix over 7 yearsEven NSA, DNC and bitcoin exchanges have been hacked recently. I think it's safe to say Ubuntu repositories are 99.99999% virus free which is the spirit of the question and our answers. Indeed no one has actually come forth with a Ubuntu virus in this Q&A. There is the long standing Linux virus/malware which KASLR fixes that most people don't even know about and I only read about on a non-MSM alternate website that is non-Linux based and solely global news based. I would like to say Linux has far fewer viruses than Windows and Ubuntu Update is secure. However as always be careful of websites. -
Martin Bonner supports Monica over 7 years"burn the system to the ground" - for a really well-written virus, this is almost literally true. Physical destruction of the hardware is going to be safe; anything less is going to be hard work (eg, if the hard disk firmware has been rooted).
-
 el.pescado - нет войне over 7 yearsIt's worth noting that those three examples are not mutually exclusive. You could add third party PPA which has been hacked by means of MITM.
el.pescado - нет войне over 7 yearsIt's worth noting that those three examples are not mutually exclusive. You could add third party PPA which has been hacked by means of MITM. -
Federico Poloni over 7 yearsHow is (3) even possible? The packages are signed, and the public key for the Ubuntu official repos comes from the Ubuntu installation media. I don't think you can get infected unless you start from a fake installation media.
-
Falco over 7 yearsYou should add option number 4: Underhanded Code in an official package. Bugs like heartbleed show, that severe bugs can exist for years even openly in heavvily maintained open source software. So there is always a possibility for an attacker to inject malicious code into a repository in a way which may survive peer-reviewing. In this case you would just download the backdoor as a fully signed package from the original server.
-
Kaz Wolfe over 7 years@FedericoPoloni I'm dealing with the realms of theory here. While such an attack would be exceedingly hard to pull off successfully (someone would need to MITM key servers, the repos, and as you pointed out the ISO server), it could still theoretically be done by someone with enough time and desire to pull off this attack.
-
Charles Duffy over 7 yearsA checksum protects against accidental corruption, but not intentional tampering -- it's the OpenPGP signatures that protect against tampering.
-
Charles Duffy over 7 yearsThere's a big difference between injecting malicious code into an ISO and into the apt servers. The ISOs aren't fully signed -- there's modern tooling available that could be used for such signing (EFI signing to protect the bootloader, GRUB OpenPGP validation to protect the kernel and initrd, dm-verity to protect the root filesystem), but dm-verity isn't widely used outside ChromeOS yet. The contents of the apt servers, on the other hand, all have OpenPGP signatures -- you'd need to break into the workstation of one of the trusted developers to forge them.
-
Charles Duffy over 7 yearsEh? Checksum issues aren't so much about avoiding intentional modification as accidental corruption -- unless there's a signature on it (and yes, Debian packages do also have OpenPGP signatures), a checksum can be modified just as much as the raw data itself can be. If a checksum on a package doesn't match what was present at build time, there's no reasonable expectation that that package could be extracted to get the desired original contents.
-
Mason Wheeler over 7 years@Falco Heartbleed shoes the exact opposite. When the requirements of Linus's Law are not met, as they weren't with the OpenSSL project, the benefits will not be reaped. OpenSSL could be a textbook example of how not to run a major open source project!
-
 jpmc26 over 7 yearsNote that the situation is certainly no better that this on non-Linux systems. Quite the opposite, really. The standard way of getting software on Windows is quite literally download it from some random site and hope nothing bad has happened. What you describe is about the best you can do in terms of securely installing software. (I think this is worth explicitly mentioning in the answer, as someone who asks this question is at the novice level and may not realize that.)
jpmc26 over 7 yearsNote that the situation is certainly no better that this on non-Linux systems. Quite the opposite, really. The standard way of getting software on Windows is quite literally download it from some random site and hope nothing bad has happened. What you describe is about the best you can do in terms of securely installing software. (I think this is worth explicitly mentioning in the answer, as someone who asks this question is at the novice level and may not realize that.) -
Anwar over 7 yearsInjecting ISO and serving infected apt packages are completely different. A server can be hacked and infected iso can be served, but apt can't be distributed this way. there are signatures that will prevent it
-
Charles Duffy over 7 yearsThe question here is whether and to what extent the apt-get ecosystem is in fact secure, which I'm not sure this answer addresses head-on. As for "terrible idea" -- beyond distributing OpenPGP keys owned by trusted developers with the operating system (as is already done), and requiring explicit user action to enable additional keys (as when adding a PPA), what additional measures would or could you add if you were building your own software distribution system?
-
 mobileink over 7 yearsno, the question is very explicit. just read the op. "Can I get a virus?" yes, unequivocally. building your own software distribution system is a completely different question.
mobileink over 7 yearsno, the question is very explicit. just read the op. "Can I get a virus?" yes, unequivocally. building your own software distribution system is a completely different question. -
 mobileink over 7 yearsps. I said "I think" it is a terrible idea, which cannot be challenged. I do in fact it is a terrible idea for software distribution systems to require sudo.
mobileink over 7 yearsps. I said "I think" it is a terrible idea, which cannot be challenged. I do in fact it is a terrible idea for software distribution systems to require sudo. -
Charles Duffy over 7 yearsI'd argue that it's an even more terrible idea to allow an unprivileged user to install software in locations where it's in the default PATH for other unprivileged users. Homebrew is a severe offender here -- as soon as it's performed its setup, any compromised process running under the relevant uid can install software under
/usr/local/binwithout requiring the user to affirm that they intend to permit administrative activity. -
 mobileink over 7 years@Charles Duffy: you mean "facts" like "I'd argue it's even more terrible ... "? what exactly is your point - that it is not possible to acquire a virus by running sudo?
mobileink over 7 years@Charles Duffy: you mean "facts" like "I'd argue it's even more terrible ... "? what exactly is your point - that it is not possible to acquire a virus by running sudo? -
Charles Duffy over 7 yearsThe "even more terrible" was argument; the fact backing that argument was that allowing installation of software without privilege escalation requires unprivileged users to write to locations in PATH. That setting permissions that allow this makes it exceptionally easy for viruses, malicious code, &c. to infect a system should be a trivial matter of inference.
-
Charles Duffy over 7 yearsBacking up, the question here is about a "virus" -- inherently, then, something self-spreading, not arbitrary malicious code. Self-spreading code infecting a distribution server is a very plausible threat model, but self-spreading code infecting the workstation of a small set of trusted developers with a distribution OpenPGP key, and then that worm being advanced enough to recognize what it found and generate Debian release signatures with that key, and then copy that content back to an infected distribution server?
-
Charles Duffy over 7 yearsTheoretically possible, but much less likely. And this isn't Security SE where we're in the business of the theoretical -- it's Ask Ubuntu, focused on end-users with questions grounded in practice.
-
Andrea Lazzarotto over 7 yearsAssuming you trust the person who signed the package and you can check the key in a trustworthy way. Honestly though, every person sometimes downloads software from the web. The repositories are big but not infinite. Perfect security and trust is a bit of a dream.
-
Falco over 7 years@jpmc26 Microsoft tries to establish the Windows Store as the primary source of any installed software. And most people don't download software from random sites, but verify the origin over a valid HTTPs certificate or buy software vie a trusted platform (like steam) which also validates sources. - So I wouldn't call random downloads the standard way any more, but it is certainly still a wide spread practice.
-
Falco over 7 years@MasonWheeler Heartbleed doesn't show the exact opposite. I get you want to break a leg for open source development and Linus' Law - But my point is: Just because some code is in an officially signed core PPA, doesn't mean it is guaranteed to be free of bugs and viruses. You have a high chance, because submits are usually peer reviewed, but this is no guarantee (see various exploits, underhanded coding contests, NSA weak cipher keys...)
-
Jeremy over 6 yearsBut can you not add additional repositories?
-
 WinEunuuchs2Unix over 6 years@Jeremy Yet Linux is running the top 500 super-computers and most of the web servers which is a great way to hack all the Windows clients attached.
WinEunuuchs2Unix over 6 years@Jeremy Yet Linux is running the top 500 super-computers and most of the web servers which is a great way to hack all the Windows clients attached. -
 Marc over 6 years"If you add every repository you come across, you might end up installing something nasty. Don't do that."
Marc over 6 years"If you add every repository you come across, you might end up installing something nasty. Don't do that." -
Shayan about 4 yearsWould you recommend compiling a program from source using
makeor using a PPA? Does Package Manager offer any security check? -
Kaz Wolfe about 4 years@Shayan The way I've always heard this is using the "cake" analogy. With a PPA, it's like you're buying a cake from the store. Source code is getting the ingredients and making the cake yourself. In the former case, the store isn't going to check if the baker put poison into the cake batter.