Capture TCP communication on a specific port using wireshark
Solution 1
Well, you can always (asuming you have a Linux box) tcpdump traffic. For example:
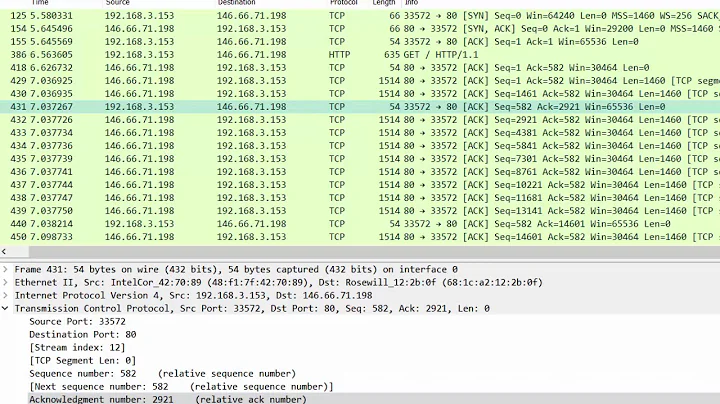
tcpdump -i eth0 net 202.168.66.1 'port 9999' -s 65535 -w dump.pcap
Assuming your interface is eth0 that you are listening on.
Start the client, send/receive messages, and then just open that dump.pcap file with Wireshark to see the communication.
Solution 2
Are you using the IP address to connect, or localhost / host name? In that case I guess it could resolve it to the internal IP address (like 127.0.0.1) and the traffic would never be put on a physical interface, and thus not seen by Wireshark.
If the traffic was there, your filter seems like it should pick it up.
Related videos on Youtube
Comments
-
Dakait over 1 year
I have build a simple TCP server which listens on port 9999, and it has IP address
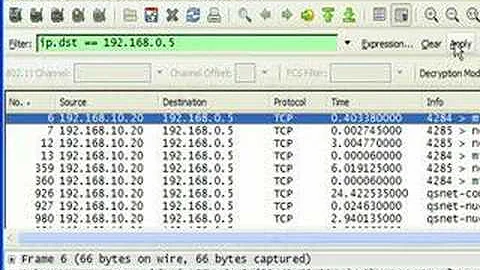
202.168.66.1. I have a TCP client which has the same IP address and connects to the server on the said port.Now when I start up the server and open Wireshark with display filter
tcp.port==9999and start the client and send/receive a message nothing get displayed in the capture window in Wireshark...What am I doing wrong here?
I'm using Windows 7.
-
HABO almost 11 yearsAre the client and server running on the same system?
-
Dakait almost 11 yearsyup they are both on the same sys
-
HABO almost 11 yearsWireshark can capture traffic that goes in and out of a system, but traffic that never leaves the box can be a problem. If you can separate the client and server, or force the network traffic to run through a gateway or router, then Wireshark should see it.
-
-
Dakait almost 11 years+1 for the info but im using windows machine
-
 Admin almost 11 yearsThen you can use WinDump (which is tcpdump ported to Windows, so most of the options are the same, although finding the right interface for the
Admin almost 11 yearsThen you can use WinDump (which is tcpdump ported to Windows, so most of the options are the same, although finding the right interface for the-iflag is more effort) or Wireshark (which also works on various UN*Xes, as does tcpdump) or Microsoft Network Monitor or any of a number of other packet analyzers.