Changing AuthorizedKeysFile in `sshd_config` not solving public key auth failure with encrypted home
You question is missing information from log produced by sshd:
/var/log/auth.log
Error message says something about wrong permissions on /home.
Manual page for sshd adds this condition:
~/.ssh/authorized_keysIf this file, the
~/.sshdirectory, or the user's home directory are writable by other users, then the file could be modified or replaced by unauthorized users. In this case,sshdwill not allow it to be used unless theStrictModesoption has been set to “no”.
So option is to fix permissions or if you need to have the /home group writable, use StrictModes no in your sshd_config.
Related videos on Youtube
bfrguci
Updated on September 18, 2022Comments
-
 bfrguci over 1 year
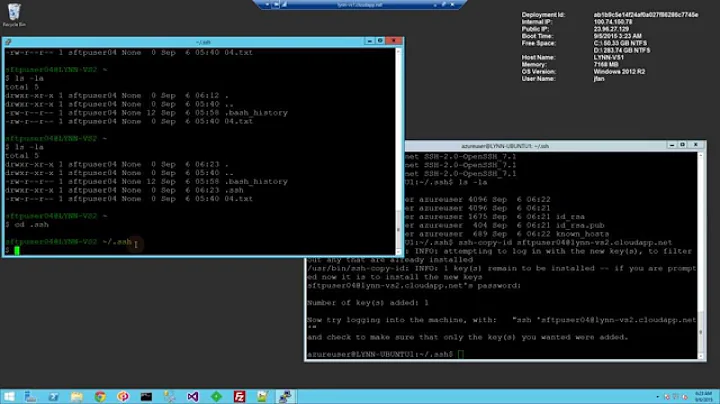
bfrguci over 1 yearThe case sounds simple. I have my home folder encrypted using eCryptFS on the "server", it looks like:
/home/<user_name>/.Private on /home/<user_name> type ecryptfs (ecryptfs_check_dev_ruid, ecryptfs_cipher=aes,ecryptfs_key_bytes=16,ecryptfs_unlink_sigs,ecryptfs_sig=<...>, ecryptfs_fnek_sig=<...>)Because the "authorized_keys" file is in
~/.sshby default, which is not decrypted before I actually login, I moved that file to/home/ssh/<user_name>/authorized_keys. The permissions of/home/ssh/<user_name>is 755, and that of theauthorized_keysfile is 644. The file contains the public key of the machine that I would like to login from.Then I changed the "AuthorizedKeysFile" option in
/etc/ssh/sshd_config, to/home/ssh/%u/authorized_keys. As is suggested by this manual: https://help.ubuntu.com/community/SSH/OpenSSH/Keys and this post: https://stephen.rees-carter.net/thought/encrypted-home-directories-ssh-key-authentication. I searched for this problem here but mostly got the same instructions. However, still I cannot log-in without a password.Then I did some tests, I generated a pair of SSH keys on the server (which I would like to SSH into), and copied the public key to
/home/ssh/<user_name>/authorized_keys. Then I found that I cannot even login tolocalhostwithout using my password, on that server machine. Therefore, I assume that for some reason SSH daemon didn't load the authorized_keys file at all. I also tried to put the file in the original location which is~/.ssh, still cannot do public key auth.Attached is my
sshd_config:# Package generated configuration file # See the sshd_config(5) manpage for details # What ports, IPs and protocols we listen for Port 22 # Use these options to restrict which interfaces/protocols sshd will bind to #ListenAddress :: #ListenAddress 0.0.0.0 Protocol 2 # HostKeys for protocol version 2 HostKey /etc/ssh/ssh_host_rsa_key HostKey /etc/ssh/ssh_host_dsa_key HostKey /etc/ssh/ssh_host_ecdsa_key HostKey /etc/ssh/ssh_host_ed25519_key #Privilege Separation is turned on for security UsePrivilegeSeparation yes # Lifetime and size of ephemeral version 1 server key KeyRegenerationInterval 3600 ServerKeyBits 1024 # Logging SyslogFacility AUTH LogLevel INFO # Authentication: LoginGraceTime 120 PermitRootLogin without-password StrictModes yes RSAAuthentication yes PubkeyAuthentication yes AuthorizedKeysFile /home/ssh/%u/authorized_keys # Don't read the user's ~/.rhosts and ~/.shosts files IgnoreRhosts yes # For this to work you will also need host keys in /etc/ssh_known_hosts RhostsRSAAuthentication no # similar for protocol version 2 HostbasedAuthentication no # Uncomment if you don't trust ~/.ssh/known_hosts for RhostsRSAAuthentication #IgnoreUserKnownHosts yes # To enable empty passwords, change to yes (NOT RECOMMENDED) PermitEmptyPasswords no # Change to yes to enable challenge-response passwords (beware issues with # some PAM modules and threads) ChallengeResponseAuthentication no # Change to no to disable tunnelled clear text passwords #PasswordAuthentication yes # Kerberos options #KerberosAuthentication no #KerberosGetAFSToken no #KerberosOrLocalPasswd yes #KerberosTicketCleanup yes # GSSAPI options #GSSAPIAuthentication no #GSSAPICleanupCredentials yes X11Forwarding yes X11DisplayOffset 10 PrintMotd no PrintLastLog yes TCPKeepAlive yes #UseLogin no #MaxStartups 10:30:60 #Banner /etc/issue.net # Allow client to pass locale environment variables AcceptEnv LANG LC_* Subsystem sftp /usr/lib/openssh/sftp-server # Set this to 'yes' to enable PAM authentication, account processing, # and session processing. If this is enabled, PAM authentication will # be allowed through the ChallengeResponseAuthentication and # PasswordAuthentication. Depending on your PAM configuration, # PAM authentication via ChallengeResponseAuthentication may bypass # the setting of "PermitRootLogin without-password". # If you just want the PAM account and session checks to run without # PAM authentication, then enable this but set PasswordAuthentication # and ChallengeResponseAuthentication to 'no'. UsePAM yesThe
authorized_keysfile is located here:$ ll total 24K drwx------ 2 root root 16K Feb 26 19:23 lost+found drwxrwxr-x 3 root root 4.0K Mar 1 13:12 ssh drwx------ 22 <user_name> <user_name> 4.0K Mar 1 13:42 <user_name> $ cd ssh $ ll total 4.0K drwxr-xr-x 2 <user_name> <user_name> 4.0K Mar 1 13:12 <user_name> $ cd <user_name> $ ll total 4.0K -rw-r--r-- 1 <user_name> <user_name> 790 Mar 1 13:32 authorized_keys $I also tried to change permissions (of the directory and the file) to 700 and 600, didn't work either...
-
Jakuje about 8 yearsdid you restart your
sshserver? Did you check for errors in the server log? Did you try to run server in more verbose mode? -
 bfrguci about 8 yearsRestarted. Where is the server log? @Jakuje
bfrguci about 8 yearsRestarted. Where is the server log? @Jakuje -
Jakuje about 8 yearsprobably in
/var/log/auth.log. If it will not help, setLogLevel DEBUG3and try again. -
 bfrguci about 8 years@Jakuje It says bad ownership or modes for
bfrguci about 8 years@Jakuje It says bad ownership or modes for/home... Now it is 775... Probably I need to move it somewhere else... -
Jakuje about 8 yearsNo. It is wrong to have 775 on
/home./homeshould be root owned with 755 if I am right. -
 bfrguci about 8 yearsI thought
bfrguci about 8 yearsI thoughtsshdonly required modes for the authorized_keys file and the folder containing it... Now it seems that it also requires that of all the upstream folders. @Jakuje I will try and will let you know if it works. -
Jakuje about 8 yearsYes. All the path to the
authorized_keysfile needs to satisfy this requirements. Also to the home folders. Does it work for you now or can I fill the answer? -
 bfrguci about 8 years@Jakuje Actually I moved the <user_name> folder to
bfrguci about 8 years@Jakuje Actually I moved the <user_name> folder to/etc/sshand changedsshd_configaccordingly. Now it works. You can surely fill in the answer :-) The weird part is, on another machine I also have/home775, but my home folder is not encrypted. SSH worked pretty fine with public key auth on that machine, though~/.sshis also under a 775/home...
-