Check for packets MARKed by iptables
Probably, they are not: your routing commands are wrong: you use
ip route add default via 192.168.0.0 dev eth0 table routeTcp
ip route add default via 192.168.1.0 dev wlan0 table routeUdp
while they should be
ip route add default via 192.168.0.1 dev eth0 table routeTcp
ip route add default via 192.168.1.1 dev wlan0 table routeUdp
if your gateways are 192.168.0.1 and 192.168.1.1, respectively; if not, pls adjust accordingly.
As for checking,
tcpdump -i eth0 -n udp
in one terminal, and
tcpdump -i wlan0 -n tcp
in another terminal; they should both return no crossing packets.
EDIT:
Sorry, I forgot we need to distinguish between incoming and outgoing packets, only the outgoing ones are segregated. Pls use
tcpdump -i wlan0 -n tcp and src host The_IP_ADDRESS_of_Wlan0
tcpdump -i eth0 -n udp and src host The_IP_ADDRESS_of_eth00
Related videos on Youtube
Comments
-
Giancarlo over 1 year
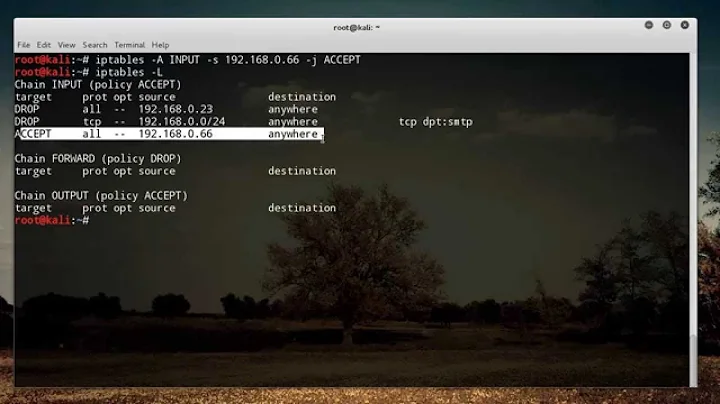
I am marking TCP and UDP packets in order to send them to two different interfaces (say wlan0 and eth0), I did this by following this answer.
Assuming this configuration:
eth0 address: 192.168.0.84 wlan0 address: 192.168.1.22I am setting the following rules/routes:
#!/bin/bash iptables -A PREROUTING -t mangle -p tcp -j MARK --set-mark 1 echo 201 routeTcp >> /etc/iproute2/rt_tables ip rule add fwmark 1 table routeTcp ip route add default via 192.168.0.0 dev eth0 table routeTcp iptables -A PREROUTING -t mangle -p udp -j MARK --set-mark 2 echo 202 routeUdp >> /etc/iproute2/rt_tables ip rule add fwmark 2 table routeUdp ip route add default via 192.168.1.0 dev wlan0 table routeUdp
route -noutput:Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 192.168.0.1 0.0.0.0 UG 0 0 0 eth0 192.168.0.0 0.0.0.0 255.255.255.0 U 1 0 0 eth0 192.168.1.0 0.0.0.0 255.255.255.0 U 9 0 0 wlan0
ip route showoutput:default via 192.168.0.1 dev eth0 proto static 192.168.0.0/24 dev eth0 proto kernel scope link src 192.168.0.84 metric 1 192.168.1.0/24 dev wlan0 proto kernel scope link src 192.168.1.22 metric 9
ip route show table routeUdp:default via 192.168.1.1 dev wlan0
ip route show table routeTcp:default via 192.168.0.1 dev eth0
iptables -nL -v --line-numbers -t mangleoutput:Chain PREROUTING (policy ACCEPT 388K packets, 474M bytes) num pkts bytes target prot opt in out source destination 1 360K 464M MARK tcp -- * * 0.0.0.0/0 0.0.0.0/0 MARK set 0x1 2 27269 11M MARK udp -- * * 0.0.0.0/0 0.0.0.0/0 MARK set 0x2 Chain INPUT (policy ACCEPT 385K packets, 474M bytes) num pkts bytes target prot opt in out source destination Chain FORWARD (policy ACCEPT 0 packets, 0 bytes) num pkts bytes target prot opt in out source destination Chain OUTPUT (policy ACCEPT 290K packets, 33M bytes) num pkts bytes target prot opt in out source destination Chain POSTROUTING (policy ACCEPT 290K packets, 33M bytes) num pkts bytes target prot opt in out source destinationHow can I check that the packets are actually being sent by the right interface?
I've been struggling with tcpdump with no success.
Thank you guys.
-
Giancarlo over 8 yearswell... you almost made my day... I see no TCP packets on wlan but I can still see some UDP packets on eth. Adding gateways does not change the situation: pastebin.com/pyRXRFmX
-
 MariusMatutiae over 8 years@Giancarlo incoming or outgoing? pls read my edit
MariusMatutiae over 8 years@Giancarlo incoming or outgoing? pls read my edit -
Giancarlo over 8 yearsOps, I forgot to say outgoing... I am gonna test it again after a reboot ;)
-
Giancarlo over 8 yearsNothing to do... eth0: lots of UDP (NOK), all the TCP(OK) wlan0 just some UDP (NOK, just five packets) and no TCP (OK)
![IPTABLES [PART-1] : "UNDERSTANDING THE CONCEPT"](https://i.ytimg.com/vi/vbhr4csDeI4/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLBovKYd5heeT0eQFP4enqBJ_GCa1Q)