Complete masquerading NAT example using nftables on Linux?
Solution 1
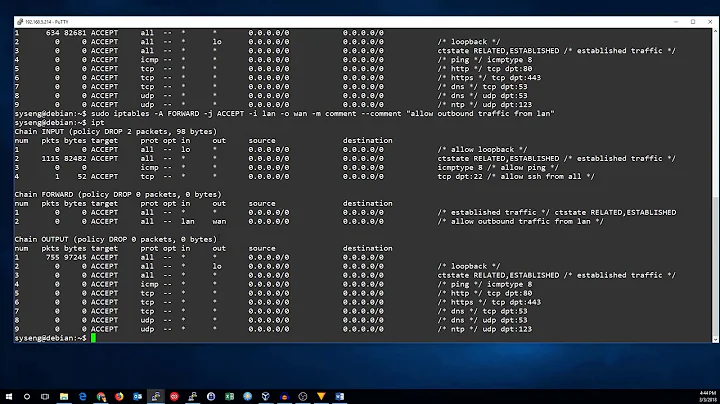
Here's what I'm using, assuming lan0 is connected to your internal network, and wan0 to your ISP.
I'm not sure what you mean by "DHCP client on the upstream interface", since this is done with a DHCP client, not nftables. The setup below doesn't restrict outgoing traffic so the DHCP request will go through.
#!/usr/bin/nft -f
flush ruleset
table inet filter {
chain input {
type filter hook input priority 0; policy drop;
# allow established/related connections
ct state {established, related} accept
# early drop of invalid connections
ct state invalid drop
# allow from loopback
iifname lo accept
# Allow from internal network
iifname lan0 accept
# allow icmp
ip protocol icmp accept
# allow ssh
tcp dport 22 accept comment "SSH in"
reject
}
chain forward {
type filter hook forward priority 0;
# Allow outgoing via wan0
oifname wan0 accept
# Allow incoming on wan0 for related & established connections
iifname wan0 ct state related, established accept
# Drop any other incoming traffic on wan0
iifname wan0 drop
}
chain output {
type filter hook output priority 0;
}
}
table ip nat {
chain prerouting {
type nat hook prerouting priority 0;
# Forward traffic from wan0 to a LAN server
iifname wan0 tcp dport 80 dnat 192.168.0.8 comment "Port forwarding to web server"
}
chain postrouting {
type nat hook postrouting priority 0;
# Masquerade outgoing traffic
oifname wan0 masquerade
}
}
Solution 2
Masquerading is a special case of SNAT. If you want to attach the trafic to output interface or output address (Source address for your internal IPs) use SNAT
Related videos on Youtube
Comments
-
Johannes Ernst over 1 year
I'm looking for a complete example how to do this using nftables. It should be a DHCP client on the upstream interface, have a 192.168.0.0/24 LAN on the other interface, and also act as a firewall.
Extra credit for opening up an ssh port on the upstream interface, and forwarding port 80 traffic to some other server on the LAN.
The nftables wiki leaves some questions unanswered. For example, the section on masquerading doesn't describe how to attach the masquerading rule to one interface vs the other.