dmesg flooded with firewall logs
Solution 1
You could use the NFLOG target instead of LOG:
NFLOG
This target provides logging of matching packets. When this target is set for a
rule, the Linux kernel will pass the packet to the loaded logging backend to log the
packet. This is usually used in combination with nfnetlink_log as logging backend,
which will multicast the packet through a netlink socket to the specified multicast
group. One or more userspace processes may subscribe to the group to receive the
packets. Like LOG, this is a non-terminating target, i.e. rule traversal continues
at the next rule.
All you'd need is a nfnetlink_log capable logging program. Messages would go there and the userspace process would decide whether to log the packet or not.
Another thing you could try would be limiting the LOG rule to a specific threshold:
-A INPUT -i eth0 -m limit --limit 10/minutes -j LOG --log-prefix "FW: " --log-level 7
-A INPUT -i eth0 -j DROP
This would on average log 10 packets per minute. You could of course adjust this at your needs.
Solution 2
When you have set the log level to 7 with the command:
-A INPUT -i eth0 -j LOG --log-prefix "FW: " --log-level 7
Then you can simply filter out these messages by passing the level threshold to the dmesg:
dmesg --level=err,warn
Related videos on Youtube
Tam Borine
Updated on September 18, 2022Comments
-
 Tam Borine over 1 year
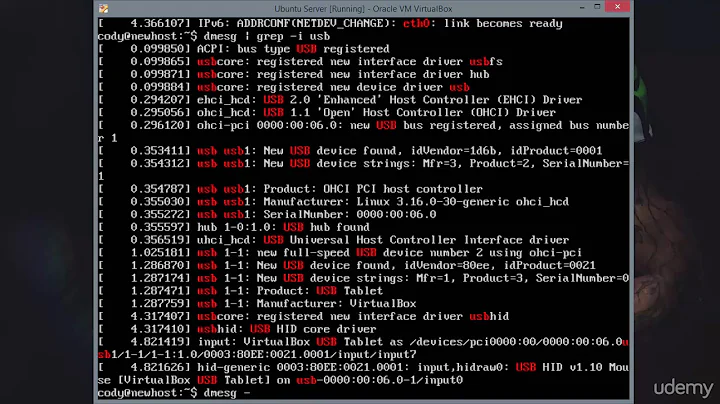
Tam Borine over 1 yearIn my iptables, I have a rule which logs dropped packets:
-A INPUT -i eth0 -j LOG --log-prefix "FW: " --log-level 7 -A INPUT -i eth0 -j DROPAnd in
/etc/rsyslog.conf, I have another rule which sends these logs to a dedicated file/var/log/firewall.log.:msg, contains, "FW: " -/var/log/firewall.log & ~The
& ~deletes the logs immediately, so that they don't floodsyslogor other log files.This works well, except that it floods
dmesgwith those firewall logs (not/var/log/dmesgbut the output of commanddmesg).Is there a way to prevent these logs being shown in
dmesg?-
 Admin almost 10 yearsWhat's the point in logging everything anyway?
Admin almost 10 yearsWhat's the point in logging everything anyway? -
 Admin almost 10 yearsIt's really no good idea to log all dropped packets. Better thing than eliminating the symptoms would be being more specific with your logging rule. E.g. it's not very wise to log any packets that are not related to any connection and don't do anything »special« (like connection initation). Would be much better to cut this down to relevant things like »Host A wanted to connect to port B«. Potentially the number of reasons a packet is dropped is massively greater than the number of reasons you would drop it for a relevant reason.
Admin almost 10 yearsIt's really no good idea to log all dropped packets. Better thing than eliminating the symptoms would be being more specific with your logging rule. E.g. it's not very wise to log any packets that are not related to any connection and don't do anything »special« (like connection initation). Would be much better to cut this down to relevant things like »Host A wanted to connect to port B«. Potentially the number of reasons a packet is dropped is massively greater than the number of reasons you would drop it for a relevant reason. -
 Admin almost 10 years@Andreas Wiese - I have simplified my rule for the sake of this question. My rules are more sophisticated and specific. But anyway, the question is how to prevent
Admin almost 10 years@Andreas Wiese - I have simplified my rule for the sake of this question. My rules are more sophisticated and specific. But anyway, the question is how to preventdmesgbeing flooded, not about firewall rules. -
 Admin about 5 yearsSee also this answer about the Netfilter logging daemon
Admin about 5 yearsSee also this answer about the Netfilter logging daemonulogd2. That is how I solved the problem.
-
-
 Tam Borine almost 10 yearsI was not able to find any information how to configure
Tam Borine almost 10 yearsI was not able to find any information how to configurersyslogto logNFLOGpackets. I need some solution that will work withrsyslog. -
uckelman almost 9 years@MartinVegter - NFLOG will work with rsyslog. For NFLOG, you would use ulogd (I think ulogd2 is needed) as the go-between. It will listen on the netlink socket to get the logs, and deliver them (as configured) to syslog. If ulogd2 is not available, use ulogd (1.x) and the ULOG target.