dmesg: read kernel buffer failed: Permission denied
So it was actually trivial, looking at the very last message from the bug report:
Part of the changelog from the aforementioned kernel: * security,printk: Enable SECURITY_DMESG_RESTRICT, preventing non-root users reading the kernel log by default (sysctl: kernel.dmesg_restrict)
So the solution is simply to run once:
% sudo sysctl kernel.dmesg_restrict=0
kernel.dmesg_restrict = 0
Then your local user can start using dmesg again. This apply to any user, instead of a group which I initially assumed.
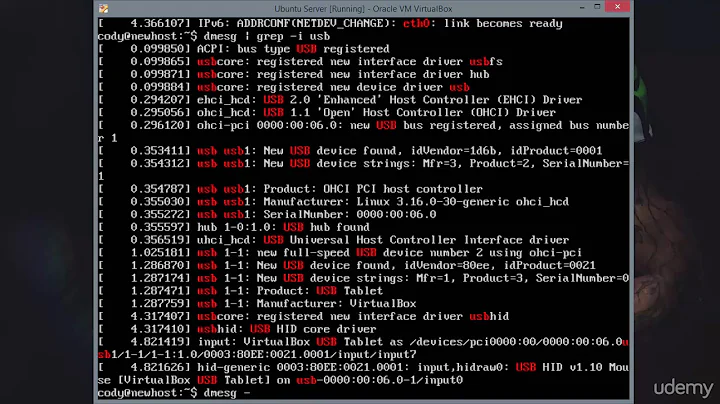
Everything is back to what I wanted:
% dmesg|wc
1307 11745 93652
and
% cat /dev/kmsg|head|wc
10 82 857
And to make it persists across reboots, simply save it as conf file:
$ cat /etc/sysctl.d/10-local.conf
kernel.dmesg_restrict = 0
Related videos on Youtube
Fakt7
Updated on September 18, 2022Comments
-
Fakt7 almost 2 years
Since recently Debian has changed the default behavior for
dmesgand I cannot use it simply from my local user.% dmesg dmesg: read kernel buffer failed: Operation not permittedSame goes for:
% cat /dev/kmsg cat: /dev/kmsg: Operation not permittedStarring at the bug tracker this lead to:
How do I change this behavior back to the previous one, where local user are allowed to use dmesg. I could not find a particular group for it (eg. sudoers or something like that).
-
 direprobs almost 7 yearsAre you able to execute this command:
direprobs almost 7 yearsAre you able to execute this command:cat /dev/kmesgas a regular user? -
 direprobs almost 7 yearsIt should be
direprobs almost 7 yearsIt should be/dev/kmsgin the first comment that was a typo. -
 Knobee almost 5 yearsEasier to make it permanent by adding
Knobee almost 5 yearsEasier to make it permanent by addingkernel.dmesg_restrict = 0to/etc/sysctl.conf -
 scruss over 3 yearsIn Ubuntu 20.10, there is already a line for this in
scruss over 3 yearsIn Ubuntu 20.10, there is already a line for this in/etc/sysctl.d/10-kernel-hardening.conf. After changing the file, the user should runsudo service procps restartto allow dmesg viewing again.

![[SOLVED] Fix /dev/kvm permission denied problem](https://i.ytimg.com/vi/g-KVqs7RxeY/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLBUqfm6jQSbtZ9eY3HKYPnTczpPgw)