Error 0x8007274C connecting via SSTP VPN to Windows 2008r2 server
SOLVED
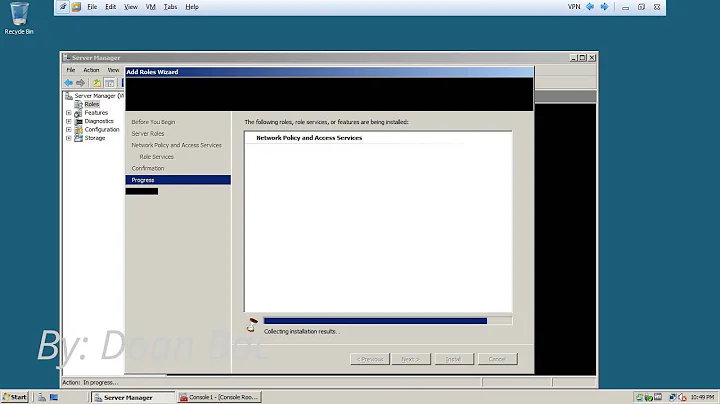
My issue was this: I had VPN and NAT routing running on the same RRAS server. NAT by default, didn't let TCP port 443 traffic through - I verified this by attempting to telnet to my SSTP server from my VPN client and got nothing.
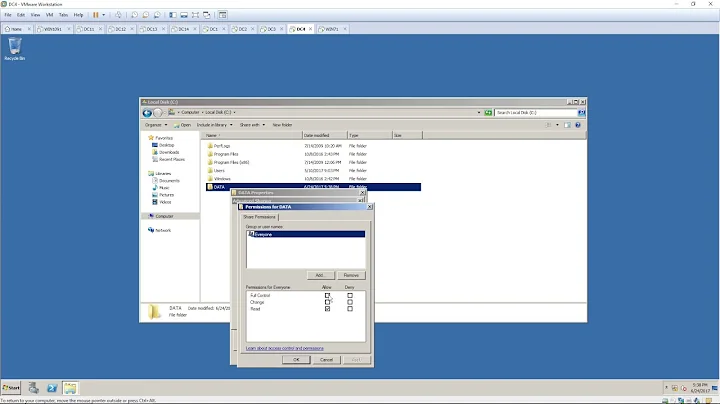
On the VPN server, I went in to Routing and Remote Access / IPv4 / NAT, and went into the adapter's properties for my public interface. Go to the Services and Ports tab, and check the box "Secure Web Server (HTTPS), and put 127.0.0.1 for the Private address. This will allow the necessary SSL traffic to get through to terminate SSTP connections. Hope this helps someone. From your VPN client, you should be able to telnet to the SSTP server on port 443.
Related videos on Youtube
mahi
Updated on September 18, 2022Comments
-
mahi over 1 year
I'm setting up a VPN using a self-signed certificate. My certificate is was generated on the server and is installed on the server. It shows up in the MMC console under "Certificates (Local Computer) / Personal / Certificates"
I have verified the binding of the certificate to the SSL listener with "netsh http show sslcert", which reports back:
SSL Certificate bindings: ------------------------- IP:port : 0.0.0.0:443 Certificate Hash : bc21f475405f********a97aa4cdecd3bfe257d3 Application ID : {ba195980-cd49-458b-9e23-c84ee0adcd75} Certificate Store Name : MY Verify Client Certificate Revocation : Enabled Verify Revocation Using Cached Client Certificate Only : Disabled Usage Check : Enabled Revocation Freshness Time : 0 URL Retrieval Timeout : 0 Ctl Identifier : (null) Ctl Store Name : (null) DS Mapper Usage : Disabled Negotiate Client Certificate : Disabled IP:port : [::]:443 Certificate Hash : bc21f475405f********a97aa4cdecd3bfe257d3 Application ID : {ba195980-cd49-458b-9e23-c84ee0adcd75} Certificate Store Name : MY Verify Client Certificate Revocation : Enabled Verify Revocation Using Cached Client Certificate Only : Disabled Usage Check : Enabled Revocation Freshness Time : 0 URL Retrieval Timeout : 0 Ctl Identifier : (null) Ctl Store Name : (null) DS Mapper Usage : Disabled Negotiate Client Certificate : DisabledHowever, "netstat -aon" does not report anything listening on port 443. I checked the registry at "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\SstpSvc\Parameters" and found that ListenerPort was set to 0. I changed it to 443. I restarted the SSTP service, but still nothing is listening on 443. "sc query sstpsvc" and "sc query remoteaccess" both report "State 4 Running"
The error is shown on the client. The VPN client is a Windows 7 machine on the local LAN. The VPN is configured to use only SSTP. If I change it to use PPTP, it connects instantly. I have exported the self-signed certificate and imported it into the client system. I used the answer in this question to install the certificate in the client's trusted root store.
I have reviewed this article, and used the steps in this article to verify that the certificate was correctly bound.
This article discusses various error codes from SSTP connections, but unfortunately Error 0x8007274C is not mentioned. There is not very much useful information on that error found in Google. Can anyone offer any insight is fixing this problem?
-
mahi almost 11 yearsIt appears that restarting relevant services does not update ListenerPort. A full server restart was required. Now the error message has changed to 0x800B010F, which is a certificate name mismatch. Now to chase that down....
-