exclude commands from user's sudo permissions
Solution 1
Without using additional security levels like SELinux, you cannot do this. But then it is a bad idea too, since there are really a lot of other possibilities to lock other user out if one can get (nearly full) root rights via sudo.
See https://serverfault.com/questions/36759/editing-sudoers-file-to-restrict-a-users-commands
Solution 2
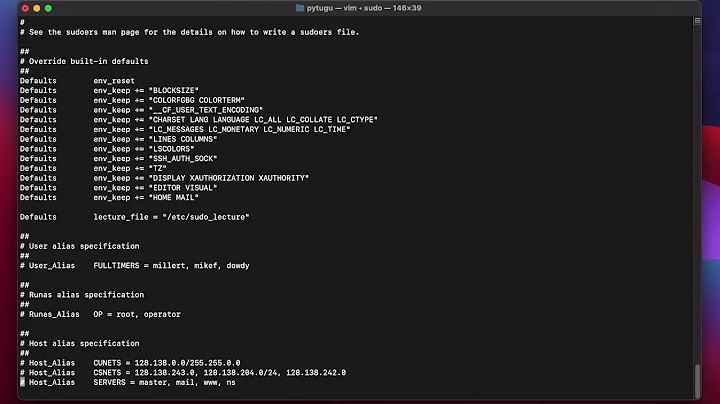
You can do this with Cmnd_Alias record. In your case solution will be like:
Cmnd_Alias PASSWD = /usr/bin/passwd
username ALL=(ALL) ALL, !PASSWD
Related videos on Youtube
Comments
-
moooeeeep over 1 year
Consider the following line in a
/etc/sudoersfile:username ALL=(ALL) ALL, !/usr/bin/passwdas far as I know, this allows user
usernameto use sudo, unless he not uses/usr/bin/passwd. But apparantly the user is still able to get a root shell usingsudo -s/sudo -iand do whatever he likes. Have I understood this correctly? What would be a better configuration if I indeed want to disallow the user to change any password as root. -
moooeeeep about 12 yearsThanks for your reply! Would then a whitelist approach be effective, i.e. only allow him to use
aptitude, or would it still be possible to get a root shell? -
YoloTats.com about 12 yearsA whitelist could work. But you need to know all features of the allowed programs: For example, if a user (re)installs/updates a package which want to overwrite an existing configuration file, a option is provided to run a shell with full root-rights to "resolve" this issue... I do not know how the new PackageKit, which can be configured via Policykit such that normal user can install packages, handle this case. Beside this, the user can install unsafe software and exploit it to get root access.
-
 dubek over 3 yearsThe gtfobins list tells you what you can do when given access to some restricted programs (for example access to
dubek over 3 yearsThe gtfobins list tells you what you can do when given access to some restricted programs (for example access toapt-getcan be used to show info withless, which can be used to run arbitrary shell commands using a!command).