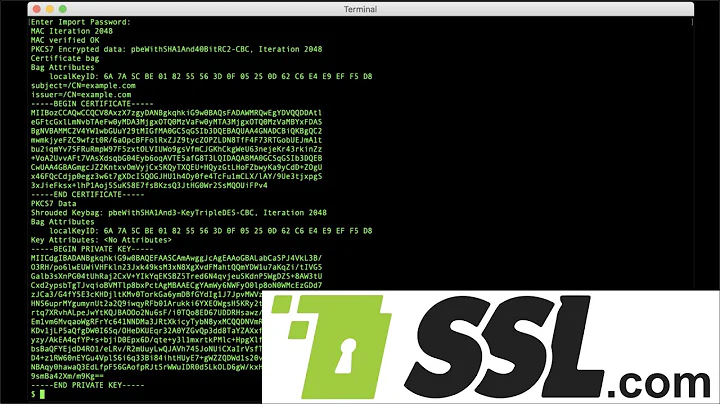
Extract public/private key from PKCS12 file for later use in SSH-PK-Authentication
Solution 1
You can use following commands to extract public/private key from a PKCS#12 container:
-
PKCS#1 Private key
openssl pkcs12 -in yourP12File.pfx -nocerts -out privateKey.pem -
Certificates:
openssl pkcs12 -in yourP12File.pfx -clcerts -nokeys -out publicCert.pem
Solution 2
This is possible with a bit of format conversion.
To extract the private key in a format openssh can use:
openssl pkcs12 -in pkcs12.pfx -nocerts -nodes | openssl rsa > id_rsa
To convert the private key to a public key:
openssl rsa -in id_rsa -pubout | ssh-keygen -f /dev/stdin -i -m PKCS8
To extract the public key in a format openssh can use:
openssl pkcs12 -in pkcs12.pfx -clcerts -nokeys | openssl x509 -pubkey -noout | ssh-keygen -f /dev/stdin -i -m PKCS8
Solution 3
OpenSSH cannot use PKCS#12 files out of the box. As others suggested, you must extract the private key in PEM format which gets you from the land of OpenSSL to OpenSSH. Other solutions mentioned here don’t work for me. I use OS X 10.9 Mavericks (10.9.3 at the moment) with “prepackaged” utilities (OpenSSL 0.9.8y, OpenSSH 6.2p2).
First, extract a private key in PEM format which will be used directly by OpenSSH:
openssl pkcs12 -in filename.p12 -clcerts -nodes -nocerts | openssl rsa > ~/.ssh/id_rsa
I strongly suggest to encrypt the private key with password:
openssl pkcs12 -in filename.p12 -clcerts -nodes -nocerts | openssl rsa -passout 'pass:Passw0rd!' > ~/.ssh/id_rsa
Obviously, writing a plain-text password on command-line is not safe either, so you should delete the last command from history or just make sure it doesn’t get there. Different shells have different ways. You can prefix your command with space to prevent it from being saved to history in Bash and many other shells. Here is also how to delete the command from history in Bash:
history -d $(history | tail -n 2 | awk 'NR == 1 { print $1 }')
Alternatively, you can use different way to pass a private key password to OpenSSL - consult OpenSSL documentation for pass phrase arguments.
Then, create an OpenSSH public key which can be added to authorized_keys file:
ssh-keygen -y -f ~/.ssh/id_rsa > ~/.ssh/id_rsa.pub
Solution 4
Solution 1:
Extract P12 from jks
keytool -importkeystore -srckeystore MyRootCA.jks -destkeystore MyRootCA.p12 -deststoretype PKCS12
Extract PEM from P12 and Edit file and pem from crt file
openssl pkcs12 -in MyRootCA.p12 -clcerts -nokeys -out MyRootCA.crt
Extract key from jks
openssl pkcs12 -in MyRootCA.p12 -nocerts -out encryptedPrivateKey.pem
openssl rsa -in encryptedPrivateKey.pem -out decryptedPrivateKey.key
Solution 2:
Extract PEM and encryptedPrivateKey to txt file```
openssl pkcs12 -in MyRootCA.p12 -out keys_out.txt
Decrypt privateKey
openssl rsa -in encryptedPrivateKey.key [-outform PEM] -out decryptedPrivateKey.key
Solution 5
Update: I noticed that my answer was just a poor duplicate of a well explained question on https://unix.stackexchange.com/... by BryKKan
Here is an extract from it:
openssl pkcs12 -in <filename.pfx> -nocerts -nodes | sed -ne '/-BEGIN PRIVATE KEY-/,/-END PRIVATE KEY-/p' > <clientcert.key>
openssl pkcs12 -in <filename.pfx> -clcerts -nokeys | sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > <clientcert.cer>
openssl pkcs12 -in <filename.pfx> -cacerts -nokeys -chain | sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > <cacerts.cer>
Related videos on Youtube
lazydaemon
Updated on July 08, 2022Comments
-
lazydaemon almost 2 years
I want to extract the public and private key from my
PKCS#12file for later use in SSH-Public-Key-Authentication.Right now, I'm generating keys via ssh-keygen which I put into
.ssh/authorized_key, respective somewhere on the client-side.In future, I want to use the keys from a
PKCS#12container, so I've to extract the public-key first fromPKCS#12and then put them into the.ssh/authorized_keysfile. Is there any chance to get this working viaopenssl? Are the keys inPKCS#12compatible for ssh-public-key authentication? -
edthethird almost 9 yearsthe commands work, but the Private key is exported as PKCS1 format and I need PKCS8... Is there any option I am missing to get this? For example, it exports '-----BEGIN RSA PRIVATE KEY-----' but I need '-----BEGIN PRIVATE KEY-----'
-
Snekse almost 9 yearsWhat's the
| openssl rsastuff for? -
 F4-Z4 almost 9 years@Snekse it makes sure there's only private key in the output. In my case, it creates identity file (
F4-Z4 almost 9 years@Snekse it makes sure there's only private key in the output. In my case, it creates identity file (~/.ssh/id_rsa) with some “cruft” like Bag Attributes without ` | openssl rsa`. I guess OpenSSH and other utilities which use identity file can handle that cruft (I haven’t tried), but I am simply used to provide only the necessary data and nothing more, especially if it's something around security. -
BillyRayCyrus over 8 yearsThis answer worked for me to get access to the PEM-format private key in the terminal, which I was able to copy/paste:
openssl pkcs12 -in filename.p12 -clcerts -nodes -nocerts -
Francois over 8 yearsTo do that you could try
openssl rsa -in privateKey.pem -out private.pem -
Christopher K. over 8 years@edthethird: To get PKCS8, add the -nodes flag
-
nidheeshdas over 8 yearsTo export without password, add
-passout pass:. It expects the parameter to be in the form pass:mypassword. stackoverflow.com/a/27497899/206277 -
BTC over 7 yearsThank you! The first line was the one I needed. Just the key, unencrypted, so it can be installed via most CDNs automated systems.
-
 TecHunter over 7 years@ChristopherK. thanks! that was the good one for me. adding
TecHunter over 7 years@ChristopherK. thanks! that was the good one for me. adding-nodesexports the key correctly -
 ryanc almost 7 years@PhilipRego I think you have public and private keys confused. An RSA public key is two values, 'e' the public exponent, and 'n' the modulus - both of which are stored along side the private parts of the key.
ryanc almost 7 years@PhilipRego I think you have public and private keys confused. An RSA public key is two values, 'e' the public exponent, and 'n' the modulus - both of which are stored along side the private parts of the key. -
 PatS about 6 yearsWhen answering questions it helps to highlight what the commands are. You can do that by adding three backquotes before and after the command so ```echo hello``` becomes
PatS about 6 yearsWhen answering questions it helps to highlight what the commands are. You can do that by adding three backquotes before and after the command so ```echo hello``` becomesecho hello. -
 mx0 over 5 yearsAdding some explanation would make this answer more useful.
mx0 over 5 yearsAdding some explanation would make this answer more useful. -
Styx about 5 yearsThat should be a comment to accepted answer, not the answer.
-
mlerley over 4 yearsTo get the CA certificate, use
openssl pkcs12 -in yourP12File.pfx -cacerts -nokeys -out caCert.pem -
Philip Rego over 4 yearsThis only exports the first certificate.