Extracting SSL certificates from the network or pcap files
Solution 1
Do you need the certificates in a particular format (PEM/DER/...)?
ssldump can show parsed ASN.1 certificates with the -N option and read a pcap file as input with -r. The following command could show you the certificates in a human-readable form.
ssldump -Nr file.pcap | awk 'BEGIN {c=0;} { if ($0 ~ /^[ ]+Certificate$/) {c=1; print "========================================";} if ($0 !~ /^ +/ ) {c=0;} if (c==1) print $0; }'
The awk script isn't the cleanest but does the job (improvements more than welcome).
The -x option of ssldump would show you the actual packet payload (packet_data). That will include the record layer and handshake protocol fields (i.e. not the certificate only). A more intelligent script/code might be able to extract it from there and convert it to a more common format.
Solution 2
The easiest way to extract X.509 certificates from a PCAP file with SSL traffic (like HTTPS) is to load the PCAP into the free open-source software NetworkMiner. You'll find the extracted certificate under the "Files" tab in NetworkMiner.
NetworkMiner automatically extracts X.509 certificates to disk from SSL/TLS sessions going to any of the following TCP ports: 443, 465, 563, 992, 993, 994, 995, 989, 990, 5223, 8170, 8443, 9001 and 9030.
You can download NetworkMiner here: http://sourceforge.net/projects/networkminer/
Also, see this guide for how to install and run NetworkMiner on Linux: http://www.netresec.com/?page=Blog&month=2014-02&post=HowTo-install-NetworkMiner-in-Ubuntu-Fedora-and-Arch-Linux
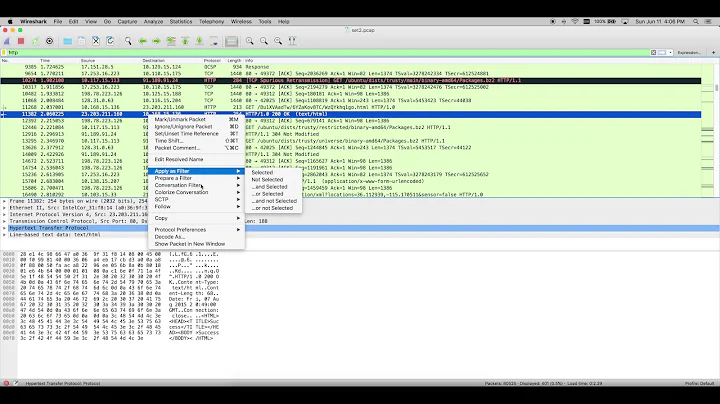
Related videos on Youtube
Apakoh
Updated on September 18, 2022Comments
-
Apakoh over 1 year
I will appreciate if someone can point me to a tool or approach to extract SSL/TLS certificates from live HTTPS connections (directly from the network) or from a network trace file (pcap file). I tried using ssldump but I was not able to extract the certificates. I can also use Wireshark for this (manually), but I want to do this in an automated way. I am using a Linux platform for this. Thanks
Edit: I want to extract the SSL certificate than a server sends to the client (browser) during an SSL handshake. I want to use a network sniffer (tcpdump) to capture the SSL connections in a network and then extract the certificates from the resulting pcap file (or doing it live).
-
 Admin over 12 yearsMaybe I didn't explain well. By using a network sniffer, I want to extract the server SSL certificates that clients (browsers) receive while establishing a SSL connection (HTTPS). The certificate is send by the server during the SSL handshake and it is not encrypted.
Admin over 12 yearsMaybe I didn't explain well. By using a network sniffer, I want to extract the server SSL certificates that clients (browsers) receive while establishing a SSL connection (HTTPS). The certificate is send by the server during the SSL handshake and it is not encrypted. -
sanmai over 12 yearsWhat is stopping you from using
openssl s_client? Why can't you connect to a server to check a certificate? -
 Admin over 12 yearsI don't want to check the certificate of a specific server. I want to monitor the certificates that other clients in the network are using. For example, if a use tcpdump to capture HTTPS connections in the network (promiscuous mode), I want to extract automatically the server certificates that were used to established such connections (during the SSL handshake).
Admin over 12 yearsI don't want to check the certificate of a specific server. I want to monitor the certificates that other clients in the network are using. For example, if a use tcpdump to capture HTTPS connections in the network (promiscuous mode), I want to extract automatically the server certificates that were used to established such connections (during the SSL handshake). -
sanmai over 12 yearsYou can pipe
tcpdumpoutput into agrep/sedfilter and pipe it toxargs openssl s_clientand it'll show you certificate info for each connection matchingtcpdumpfilter you setup. -
 Admin over 12 yearsIf I understand correctly, you are suggesting to use the filtered connection information to download the certificate from the server directly, instead of extracting it from the existent connection. I want a passive tool, asking again for the certificate to the server is not very efficient if the SSL network load is high. Also, I want to make sure I see exactly the same certificate that the client is using, which could differ in some scenarios (some sites use multiple certificates in their SSL reverse-proxies). Thanks for the suggestion anyway.
Admin over 12 yearsIf I understand correctly, you are suggesting to use the filtered connection information to download the certificate from the server directly, instead of extracting it from the existent connection. I want a passive tool, asking again for the certificate to the server is not very efficient if the SSL network load is high. Also, I want to make sure I see exactly the same certificate that the client is using, which could differ in some scenarios (some sites use multiple certificates in their SSL reverse-proxies). Thanks for the suggestion anyway. -
 President James K. Polk over 12 yearswhere do you get ssldump from?
President James K. Polk over 12 yearswhere do you get ssldump from? -
nrolans over 12 yearsYou can get it from sourceforge. Most distributions will have a package for it. I did this on version 0.9b3.
-
Apakoh over 12 yearsGreat. I new that ssldump was the tool for this, however, I think my problem was that the pcap files that I was trying did not have all the packet payload (truncated). Trying the command you suggest on live connections (not from a pcap file) I am able to see the certificates. I will try the -x option and figure out how to parse the certificate information from the packed data because I want the certificates in DER format. Thanks a lot!