firewall-cmd reject destination address
On inspection of the full iptables -n --list output, IN_public_deny is (eventually) called from the INPUT chain, which has nothing to do with packets sent from the system to the thus undenied host; those packets are instead routed through the OUTPUT chain (or possibly FORWARD if the firewall is a router or bridge between the source and destination). firewalld.richlanguage(5) does not appear to offer any means of specifying that the rule must go onto the OUTPUT (or FORWARD) chain, so the "last resort" option of a direct rule appears to be one solution.
firewall-cmd --direct --add-rule ipv4 filter OUTPUT_direct 0 -p icmp -d 10.52.208.220 -j REJECT --reject-with icmp-host-prohibited
(Though usually I prefer to DROP (and possibly LOG with rate limiting) instead of sending ICMP rejects, as if the host-to-be-blocked is going nuts, throwing ICMP response packets to it back onto a burdened network can make things go from bad to worse...)
Related videos on Youtube
alexus
Consulting | alexus.biz Dmitry Chorine | LinkedIn a1exus (a1exus) on Twitter Verify a Red Hat Certified Professional | redhat.com
Updated on September 18, 2022Comments
-
 alexus almost 2 years
alexus almost 2 yearsI'm using following:
# cat /etc/redhat-release CentOS Linux release 7.1.1503 (Core) # rpm -q firewalld firewalld-0.3.9-11.el7.noarch #I'm trying to block specific IP address (10.52.208.220) from reaching it from my system, yet unable to do so:
before:
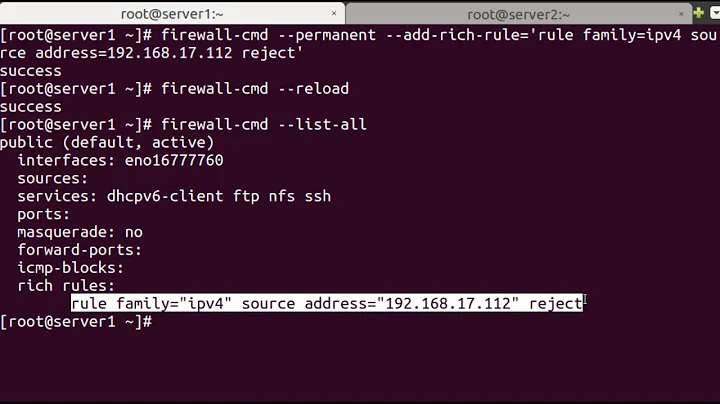
# firewall-cmd --reload success # firewall-cmd --list-all public (default, active) interfaces: eno1 sources: services: dhcpv6-client high-availability http https ssh ports: 5666/tcp 3306/tcp 5900/tcp 9001/tcp masquerade: no forward-ports: icmp-blocks: rich rules: # ping -c1 wcmisdlin01 PING wcmisdlin01.uftmasterad.org (10.52.208.220) 56(84) bytes of data. 64 bytes from wcmisdlin01.uftmasterad.org (10.52.208.220): icmp_seq=1 ttl=64 time=0.379 ms --- wcmisdlin01.uftmasterad.org ping statistics --- 1 packets transmitted, 1 received, 0% packet loss, time 0ms rtt min/avg/max/mdev = 0.379/0.379/0.379/0.000 ms #after:
# firewall-cmd --add-rich-rule='rule family="ipv4" destination address="10.52.208.220" protocol value="icmp" reject' success # firewall-cmd --list-all public (default, active) interfaces: eno1 sources: services: dhcpv6-client high-availability http https ssh ports: 5666/tcp 3306/tcp 5900/tcp 9001/tcp masquerade: no forward-ports: icmp-blocks: rich rules: rule family="ipv4" destination address="10.52.208.220" protocol value="icmp" reject # ping -c1 wcmisdlin01 PING wcmisdlin01.uftmasterad.org (10.52.208.220) 56(84) bytes of data. 64 bytes from wcmisdlin01.uftmasterad.org (10.52.208.220): icmp_seq=1 ttl=64 time=0.266 ms --- wcmisdlin01.uftmasterad.org ping statistics --- 1 packets transmitted, 1 received, 0% packet loss, time 0ms rtt min/avg/max/mdev = 0.266/0.266/0.266/0.000 ms #IPTABLES(8) - iptables/ip6tables — administration tool for IPv4/IPv6 packet filtering and NAT# iptables --list IN_public_deny Chain IN_public_deny (1 references) target prot opt source destination REJECT icmp -- anywhere wcmisdlin01.uftmasterad.org ctstate NEW reject-with icmp-port-unreachable #What am I doing wrong?
-
thrig almost 9 years
IN_public_denysounds like it is for inbound packets, e.g. from the remote system to your system. This would therefore not block a outgoing connection from your system to the host in question, as the response from the blocked host would be shuffled through the connection state created by the outgoing packet. -
 alexus almost 9 years@thrig that's what I thought too, that's why I included in my question, but then again chain can be named differently, the question is how to make it work)
alexus almost 9 years@thrig that's what I thought too, that's why I included in my question, but then again chain can be named differently, the question is how to make it work)
-


![Managing firewalld using firewall-cmd command [RHEL-7.3]](https://i.ytimg.com/vi/sA_MBFD-gLA/hqdefault.jpg?sqp=-oaymwEcCOADEI4CSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLAg7lhiyHFRLrerdmXtU3MPpn4oHQ)