How can I verify if TLS 1.2 is supported on a remote web server from the RHEL/CentOS shell?
Solution 1
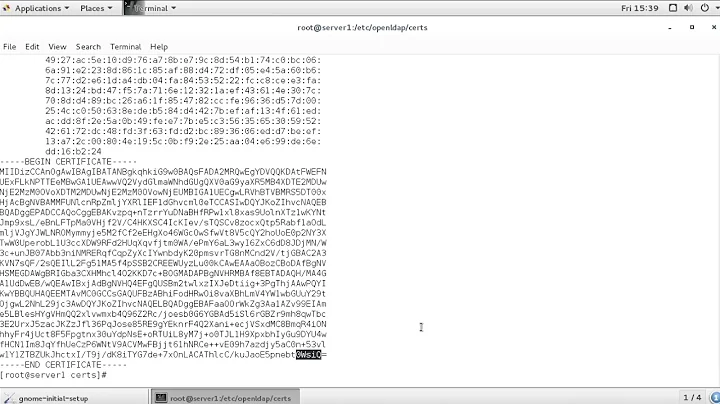
You should use openssl s_client, and the option you are looking for is -tls1_2.
An example command would be:
openssl s_client -connect google.com:443 -tls1_2
If you get the certificate chain and the handshake you know the system in question supports TLS 1.2. If you see don't see the certificate chain, and something similar to "handshake error" you know it does not support TLS 1.2. You can also test for TLS 1 or TLS 1.1 with -tls1 or tls1_1 respectively.
Solution 2
Also you can list all supported ciphers using:
nmap --script ssl-enum-ciphers -p 443 www.example.com
And then check the output. If it's supported you'll get something like this:
| TLSv1.2:
| ciphers:
| TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA - strong
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA - strong
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 - strong
| TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 - strong
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA - strong
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 - strong
| TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 - strong
| TLS_ECDHE_RSA_WITH_RC4_128_SHA - strong
| TLS_RSA_WITH_3DES_EDE_CBC_SHA - strong
| TLS_RSA_WITH_AES_128_CBC_SHA - strong
| TLS_RSA_WITH_AES_128_CBC_SHA256 - strong
| TLS_RSA_WITH_AES_128_GCM_SHA256 - strong
| TLS_RSA_WITH_AES_256_CBC_SHA - strong
| TLS_RSA_WITH_AES_256_CBC_SHA256 - strong
| TLS_RSA_WITH_AES_256_GCM_SHA384 - strong
| TLS_RSA_WITH_RC4_128_MD5 - strong
| TLS_RSA_WITH_RC4_128_SHA - strong
| compressors:
| NULL
Related videos on Youtube
Mike B
Technology Enthusiast, Gamer, Sci-Fi Addict, and DIY-er in training. =)
Updated on September 18, 2022Comments
-
 Mike B over 1 year
Mike B over 1 yearI'm on CentOS 5.9.
I'd like to determine from the linux shell if a remote web server specifically supports TLS 1.2 (as opposed to TLS 1.0). Is there an easy way to check for that?
I'm not seeing a related option on
opensslbut perhaps I'm overlooking something. -
 Michael Hampton over 9 yearsAnd keep in mind that you'll have to use a version of OpenSSL which does TLS 1.2, and that means CentOS 5 is right out.
Michael Hampton over 9 yearsAnd keep in mind that you'll have to use a version of OpenSSL which does TLS 1.2, and that means CentOS 5 is right out. -
 Xavier Lucas over 9 yearsGot a really hard time trying to make this third party script work. Wrote mine for people interested : here.
Xavier Lucas over 9 yearsGot a really hard time trying to make this third party script work. Wrote mine for people interested : here. -
Quanlong almost 9 yearsDoes not work on Mac OS X 10.11
-
Kevin_Kinsey almost 9 yearsMichael Hampton, only OOB setups: [me@server][~] cat /etc/redhat-release CentOS release 5.11 (Final) [me@server][~] openssl version OpenSSL 1.0.2d 9 Jul 2015 ;)
-
 Xiao almost 9 years@Quanlong homebrew has openssl v1.0.2. Install it then run it with
Xiao almost 9 years@Quanlong homebrew has openssl v1.0.2. Install it then run it with/usr/local/Cellar/openssl/1.0.2d_1/bin/openssl s_client -connect google.com:443 -tls1_2 -
Quanlong almost 9 yearsIt works fine after
brew upgrade openssl -
colefner almost 7 yearsIt worked great for me.
-
 Abrar Hossain over 5 yearsWorked as per expectation on OpenSuse Tumbleweed. Thanks
Abrar Hossain over 5 yearsWorked as per expectation on OpenSuse Tumbleweed. Thanks -
 Mariano Paniga over 4 yearsSee also this very good answer to similar question: security.stackexchange.com/a/169738/60157
Mariano Paniga over 4 yearsSee also this very good answer to similar question: security.stackexchange.com/a/169738/60157 -
 Gaurav Kansal about 4 yearsAs on date, nmap doesn’t support TLS1.3, so this command will not help if you want to check for TLS1.3 availability on the web server side. Otherwise for upto version 1.2 , this solution is working fine.
Gaurav Kansal about 4 yearsAs on date, nmap doesn’t support TLS1.3, so this command will not help if you want to check for TLS1.3 availability on the web server side. Otherwise for upto version 1.2 , this solution is working fine.
![[SOLVED] How to Fix TLS Error Problem (100% Working)](https://i.ytimg.com/vi/8eo-fdMAG80/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLBEOSFJoTnwm_lg5xvfZHXnoee0Wg)