How can you prevent root password change on linux?
Solution 1
You have to think about it like this. If you give them the root password, or a route to it, you're essentially asking "how can I give them root except for all the times when I magically don't want them to have it". And the answer is "you can't. Computers don't work that way."
Solution 2
You can selectively allow certain commands with sudo, but you must be careful to not permit programs that allow shell access, writing to sym links, or one of a few dozen other problems. Here's a page on secure sudo scripting: http://www.kramse.dk/projects/unix/security-sudo-script_en.html
You could always hope that they don't know about the chattr command ;-)
Solution 3
I think the answer here depends on whether you are trying to stop them from maliciously changing the password to keep you out, or just carelessly getting the password because they forgot you need access. In the former case you are going to have a lot of trouble. I don't know under what circumstance you would give users root access to the box but still be worried about this, but the best you can do is try to limit their access to commands through sudo, which as others mentioned is tricky at best. In the latter case it seems like the solution would be to create yourself a user with sudo privileges. No one is going to accidentally change the password on your account so you don't have to worry about someone just making a mistake, or even changing the password for a good reason and forgetting to tell you about it because you can always get in with your account and change it back.
Solution 4
SELinux can do what you're looking for, although it's like using a nuclear-powered planet-smashing battleax to swat a fly, or whatever the Hitchhiker's quote actually is. If you're set on Linux rather than Solaris (and its shiny RBAC), the easiest-to-implement option will likely to be to configure sudo to only allow the commands necessary.
Solution 5
There are a few options:
- You could use PAM (Pluggable Authentication Modules) to allow you to log in as root, regardless of what they set the password to. There are a lot of modules available, so I'll just leave this one hanging.
- You create 'a second root user' by opening /etc/passwd and adding a new user with the same UID as root (0). Then add a password into the /etc/shadow file for that specific user. This will allow you to log in as root and even if they change the password for 'root' - your login still works.
- Create a shellscript that is run periodically to check if the hash of the root user in /etc/shadow for root matches the one you want it to be. If it's not, the hash is changed back.
As others have pointed out, giving root access will allow them to do absolutely what ever they like on the system and if they really want to lock you out; they can. The options above however make it harder or less transparent to them.
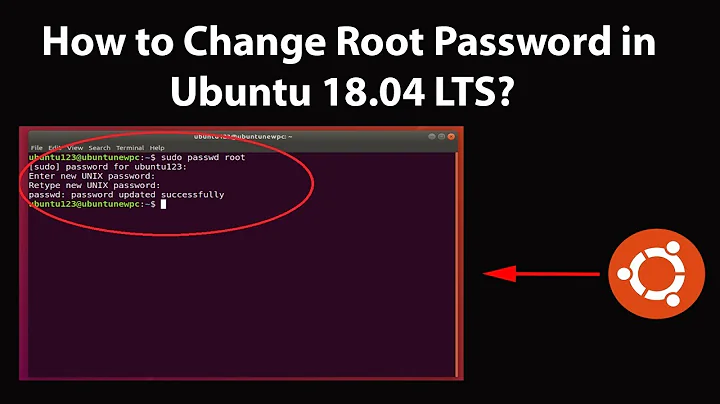
Related videos on Youtube
Philipp Jahoda
Updated on September 17, 2022Comments
-
Philipp Jahoda over 1 year
I'm setting up a server which other people will have sudo access to via ssh. They can install stuff and make changes as they see fit, however I still need to manage the server, install patches and software updates etc.
I'm wondering if I keep the root password so that I can always do what I need to, can I somehow disable people with sudo from being able to change it with sudo.
-
koenigdmj almost 15 yearsThen they run
chattr -i /etc/shadowwithsudoand are back in business. -
 womble almost 15 yearsIn either of those cases -- malice or incompetence -- you really, really, really don't want to be giving them root access at all. +1 for the "keeping a separate sudo-capable account" around.
womble almost 15 yearsIn either of those cases -- malice or incompetence -- you really, really, really don't want to be giving them root access at all. +1 for the "keeping a separate sudo-capable account" around. -
 womble almost 15 yearsNot to mention the fact that it means that no other user can change their password either, which is really bad.
womble almost 15 yearsNot to mention the fact that it means that no other user can change their password either, which is really bad. -
David Pashley almost 15 yearsWouldn't it be great if they could. I, for one, await the window manager with a Focus-Follows-Mind mode.
-
ThorstenS almost 15 yearsI already wrote "prevent THEM to change ANY password". not many sparetime admins know chattr. In the past it was very usefull for me to know and use chattr.
-
Akilan almost 15 yearsHaving a separate sudoer account is is a great idea.
-
hayalci almost 15 years+1 for chattr, or +i ;)
-
Matt Simmons almost 15 yearsDavid: Maybe eventually :-) That would be excellent.
-
chris almost 15 yearsActually getting the sudo permissions correct to absolutely contain someone is a steep hill. Once I've got a program running as UID 0, I've got just a thin paper wall between me and an actual root shell. Of course, that's assuming clever and hostile users, but still.
-
Andrioid almost 15 yearsNot really an answer to his question, now is it?
-
Brad Ackerman almost 15 yearsJust because you're paranoid, it doesn't mean they're not out to get you.
-
 Rob Moir almost 15 yearsActually, Andriod, I think it is. Maybe not the answer wanted, but an answer none the less.
Rob Moir almost 15 yearsActually, Andriod, I think it is. Maybe not the answer wanted, but an answer none the less. -
Sandokas over 14 yearsYou can, any RBAC system allow you to accomplish a similar job. Saying computers don't work that way, computers are done to work the way creators are smart enough to make them do!
-
Sumeet Kashyap over 14 yearsHmmm.. is it possible to do this with SELinux?
-
MadHatter almost 9 yearsYou might want to hold off on security pronouncements until you learn a bit more. To drive a truck through your rules above, try
sudo vi /tmp/foo, then:!/bin/bash, thenpasswd root. -
 Eric almost 9 yearsYes, this is not a polished solution, but it answers his question.
Eric almost 9 yearsYes, this is not a polished solution, but it answers his question. -
MadHatter almost 9 yearsMy point is it's not a solution at all.. If you were to try to polish it, you'd find out that the observation "you can't" is in fact correct. It's true that you can secure a system with
sudo, but you will never manage it by allowing them to do everything-except-the-listed-exceptions. It's literally impossible. -
Sam over 8 yearsObscurity is not the same as security, thus chattr is not a secure solution.