How do I allow IPSec over TCP through a Cisco ASA?
14,001
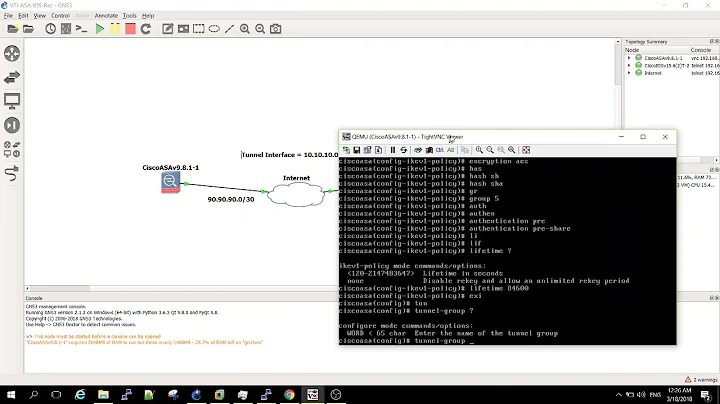
Try adding this to your asa config:
policy-map global_policy
class inspection_default
inspect ipsec-pass-thru
Related videos on Youtube
Author by
Matt
I currently work for Blue Dot Solutions, which is a mobile software company designing and developing mobile applications and MVC frameworks for mobile development. I've been in IT for 8 years, designing maintaining Blue Dot's network. I have extensive experience with VMWare, Cisco, SQL Server, Linux firewalls, IIS, and Windows OS.
Updated on September 17, 2022Comments
-
Matt almost 2 years
I have a internal user that needs to connect via VPN to an external company. The external company's vpn is using IPSec over TCP on port 57369. When my user tries to connect it fails. The logs on my ASA show the following. Deny TCP (no connection) from 172.x.x.x/1155 to 167.x.x.x/57369 flags RST on interface Inside
How do I allow this traffic through my ASA?
Thanks!
-
Matt over 14 yearsThe external company's IP is 167.124.0.37. My internal network is 172.x.x.x. It's odd that the firewall is denying an internal address from going out.
-
-
Matt over 14 yearsThanks for the reply, but still have the same issue.
-
einstiien over 14 yearsipsec-passthru is for regular ipsec traffic. He is talking about IPSec over TCP.
-
smithian over 14 yearsSorry, my fault for misreading the question. If you post your config and output of sh ver I will have a look. What you are trying to do should just work, I have the same setup in a number of offices.