How do I enable group enumeration on a Linux server that is using LDAP to connect to an AD server?
Add to /etc/nsswitch.conf:
(if needed:
passwd: files sss
group: files sss
)
Have sssd installed and configure it to search the appropriate space (/etc/sssd/sssd.conf):
[sssd]
domains = LDAP
[domains/LDAP]
ldap_schema = rfc2307bis
id_provider = ldap
auth_provider = ldap
ldap_uri = ldap://localhost
ldap_search_base = ou=users,o=company
ldap_user_search_base = ou=users,o=company
ldap_group_search_base = ou=groups,o=company
ldap_tls_reqcert = allow
cache_credentials = true
enumerate = true
min_id = 1
Related videos on Youtube
RebornGeek
MacLinuxSysAdminWordPressTwitterHumo[u]rGeekStephensonMUDsButNotWoW phew!
Updated on September 18, 2022Comments
-
RebornGeek over 1 year
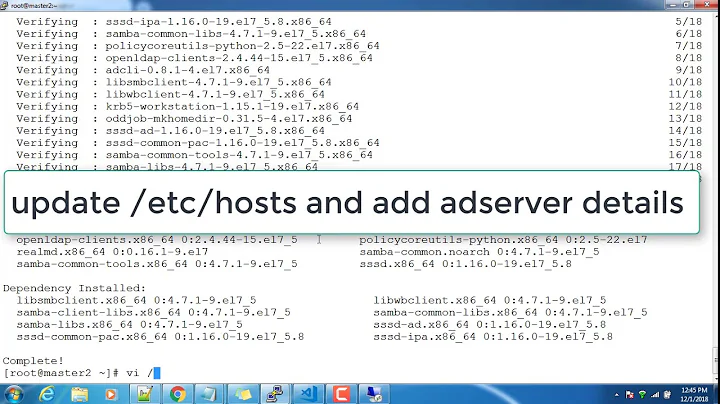
I've got a set of servers that I need to authenticate against a central Active Directory forest. The AD admins have kindly installed the UNIX AD extensions and the NIS ones as well, so I've got a lot of LDAP attributes to work from.
Authenticated binds are working, as are user logins. The one piece I'm missing is the magic sauce to make group enumerations work correctly.
Does anyone have any particular
/etc/ldap.confor perhaps PAM magic that I could employ to make groups work correctly?To wit:
[root@hostname ~]# groups username id: cannot find name for group ID 1768498755 [root@hostname ~]#(The ID is the default group specified via gidNumber.)
Thanks!
-
RebornGeek about 13 yearsGetting really close here. I can't seem to start sssd: "Starting sssd: Cannot load configuration database"
-
RebornGeek about 13 yearsOkay, I had it slightly misconfigured. Now I'm seeing the following in sssd_nss.log: "(Tue May 3 10:06:53 2011) [sssd[pam]] [confdb_get_domain_internal] (1): No enumeration for [AD]!" Ideas?
-
chandank over 11 yearsit did not help either
![LDAP Enumeration - Active Directory Enumeration | [ தமிழில் ]](https://i.ytimg.com/vi/UWdY6T--j_o/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLCd6-VmkWjI3idmxeZ8aqz09Ot2qA)