How do I stop Apache from running as root?
It is unusual to find Apache running as root in any stock configuration. How have you determined that Apache is running as root? Note that Apache must start up as root in order to bind to privileged ports, but typically sheds its privileges later on.
You can look in your Apache configuration (often in /etc/httpd or /etc/apache2, depending on your distribution) for the User and Group directives (documented here). These two directives control under what user id Apache runs.
It is also unusual to find a system that has "no other groups or users". What do getent passwd and getent group show? Are there really no other users or groups other than root? Most distributions ship with an apache or www-data user or somesuch and a matching configuration that will run Apache as that user.
There are a variety of introductory guides out there to Apache configuration and security. A simple Google search yields many likely looking results. The RedHat/CentOS Deployment Guide is a good place to start (if you're on a RedHat/CentOS system).
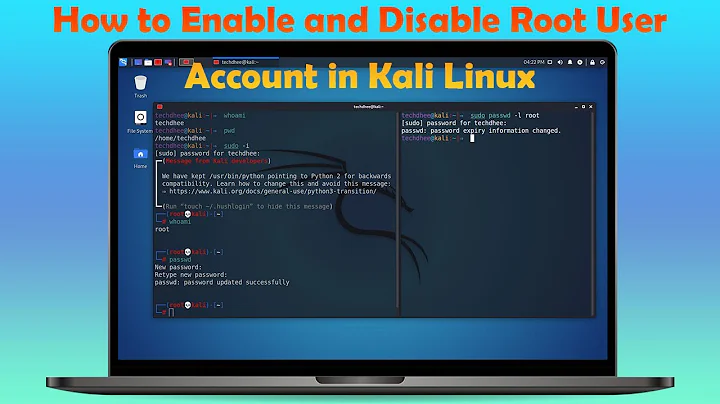
Related videos on Youtube
r00tAcc3ss
Updated on September 18, 2022Comments
-
r00tAcc3ss over 1 year
New on the job, small place, and the security stuff just landed on my desk. I was hired to be a front-end developer. Happy to learn new things, but never had to do sysadmin stuff before.
I started digging and it appears that apache, the site, and everything is running on root. There are no other groups or users. ACK!
What steps should I take to change this? I know that this is a big no-no...
Bonus points if anyone can please point me to a good basic 101 tutorial on apache/php security.
-
r00tAcc3ss about 12 yearsThanks, yeah, it wasn't running off root, but it seems that everything else has been done using root. all the folders, files, etc. I'll need to work out how to change that.
-
larsks about 12 yearsWell...not necessarily. You don't want the files owned by the same user as the running Apache process. Ideally, a compromise in the web server will not result in an attacker being able to modify your Apache configuration or web content.