How do I use remote machine's SSH keys in ansible git module
Solution 1
This is how I deploy from Github using a key file set on the remote server. If the keyfile parameter for git doesn't work then something is wrong with your playbook:
- name: Creates .ssh directory for root
sudo: yes
file: path=/root/.ssh state=directory
# This public key is set on Github repo Settings under "Deploy keys"
- name: Upload the private key used for Github cloning
sudo: yes
copy: src=keys/github dest=/root/.ssh/github
- name: Correct SSH deploy key permissions
sudo: yes
file: dest=/root/.ssh/github mode=0600
- name: Deploy site files from Github repository
sudo: yes
git:
repo: [email protected]:miohtama/foobar.git
dest: /srv/django/foobar
key_file: /root/.ssh/github
accept_hostkey: yes
force: yes
Solution 2
If I understand this correctly, you do - or want to - deploy your private key to the remote machine so you can clone the repo. I believe instead you should use key forwarding. In your .ssh/config set this:
ForwardAgent yes
Or if you want to limit this to Ansible you can define it in your ansible.cfg:
[ssh_connection]
ssh_args= -A
Solution 3
A note in case useful: for anyone using github (and I assume also applies to gitlab, etc.) - ensure that you provide the URL, correctly, in SSH form. If the key file is provided but you give ansible the HTTPS URL, it'll just quietly ignore the key and (potentially) hang waiting for input with a username and password.
Related videos on Youtube
jschank
Updated on July 09, 2021Comments
-
 jschank almost 3 years
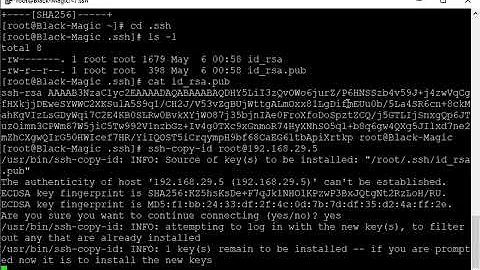
jschank almost 3 yearsI've been trying to get Ansible to provision a remote machine, and I want the remote machine to be set up with its own keys, and have the ability to clone git repositories from Bitbucket.
The user is set up, has its own id_rsa.pub, and the key has been registered with bitbucket.
But, when I use the Ansible Git module, it looks like the module always tries to use the keys from the machine running the playbook.
How do I get the git module to use the id_rsa.pub from the remote machine?
The relevant task is this:
- name: be sure prom-king has an up-to-date clone of its own repository git: repo: "ssh://[email protected]/prom-king.git" dest: /home/promking/prom-king accept_hostkey: yes clone: yes key_file: /home/promking/.ssh/id_rsa.pub update: yesThe relevant inventory is this
# inventory file for use with the vagrant box in the testing directory. [prom-king] 192.168.168.192 ansible_ssh_host=127.0.0.1 ansible_sudo=true ansible_connection=ssh ansible_ssh_port=2222 ansible_ssh_user=vagrant ansible_ssh_private_key_file=testing/.vagrant/machines/default/virtualbox/private_key-
 jschank about 9 yearsForgot to mention...I can get the clone to work with https (but that requires the password in the url, which I want to avoid) and when that clone is retrieved, the files are all owned by root on the remote machine - which is also not desired.
jschank about 9 yearsForgot to mention...I can get the clone to work with https (but that requires the password in the url, which I want to avoid) and when that clone is retrieved, the files are all owned by root on the remote machine - which is also not desired. -
Zasz about 9 yearsPaste in the playbook you are using. It could just be that git when its running on remote machine, is prompting for add bitbucket to known_hosts (yes/no) prompt which it always does when its running for the first time on a new machine
-
Zasz about 9 yearsHow do you know that git uses key from your playbook machine? All ansible modules run on remote machine unless you explicitly run on 127.0.0.1 or mark it as local_action or use delegation.
-
 jschank about 9 years@Zasz. I've added relevent code to the question. I know the keys are wrong because I get a key error when the task runs, and these vagrant keys are not on the bitbucket account. Also, when I ssh into the VM, and run the git command, it works fine. I should note that even though this is a vagrant vm, it is not provisioned with ansible. I use the VM to test the playbook before I use it on real servers. The VM uses private networking, so I access it just like any other machine (except by IP) Finally, when I use https, which works. The repo is owned by root.
jschank about 9 years@Zasz. I've added relevent code to the question. I know the keys are wrong because I get a key error when the task runs, and these vagrant keys are not on the bitbucket account. Also, when I ssh into the VM, and run the git command, it works fine. I should note that even though this is a vagrant vm, it is not provisioned with ansible. I use the VM to test the playbook before I use it on real servers. The VM uses private networking, so I access it just like any other machine (except by IP) Finally, when I use https, which works. The repo is owned by root. -
C G-K about 8 yearsPretty sure you should be specifying the private key and not the public key in key_file.
-
Code-Apprentice almost 3 years"Forgot to mention..." Feel free to edit you question at any time if you need to add details or clarification.
-
-
 Suvitruf - Andrei Apanasik over 8 yearsIt hangs if key has passphrase.
Suvitruf - Andrei Apanasik over 8 yearsIt hangs if key has passphrase. -
 halfer almost 8 yearsAn approach using
halfer almost 8 yearsAn approach usingsudonow displays[DEPRECATION WARNING]: Instead of sudo/sudo_user, use become/become_user and make sure become_method is 'sudo' (default). -
 halfer almost 8 yearsI've found that swapping
halfer almost 8 yearsI've found that swappingsudo: yesabove withbecome_user: rootworks fine for me, and removes the deprecation notice. I've already set upbecomeandbecome_methodat the start of the playbook. -
 luvejo about 6 yearsThanks! Just in case, I get ride of some nasty warning messages by using
luvejo about 6 yearsThanks! Just in case, I get ride of some nasty warning messages by usingssh_args=-o ForwardAgent=yesinstead. -
racl101 almost 6 yearsMuchas gracias. The
accept_hostkeyportion wasn't obvious from the error message I kept receiving. -
Arrow_Raider over 3 yearsNeither of -o ForwardAgent=yes works or -A. -A makes warnings appear