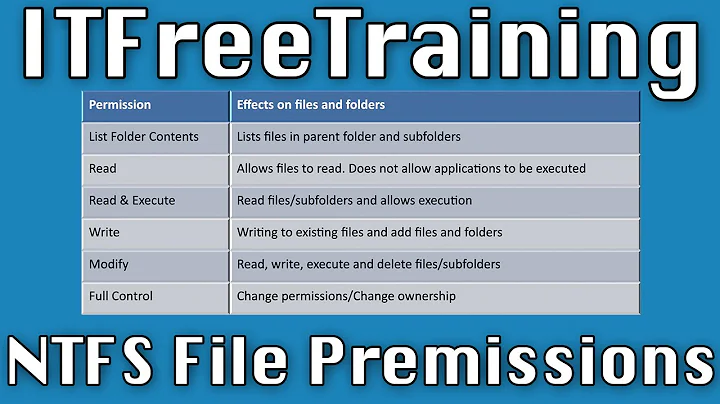
How do you grant read-only permissions on NTFS Security settings?
The minimum permission required to read a folder's permissions (DACL) is READ_CONTROL ("Read Permission"). If you also want to be able to view the folder's subfolders, FILE_LIST_DIRECTORY ("List Folder") is required.
But beware: When set on a directory, FILE_LIST_DIRECTORY gives you the right to list the children, but when set on a file it allows you to read the content.
So you probably want to use FILE_LIST_DIRECTORY+READ_CONTROL, set that on a root directory and have the permissions apply (inherit) to subfolders only, but not to files.
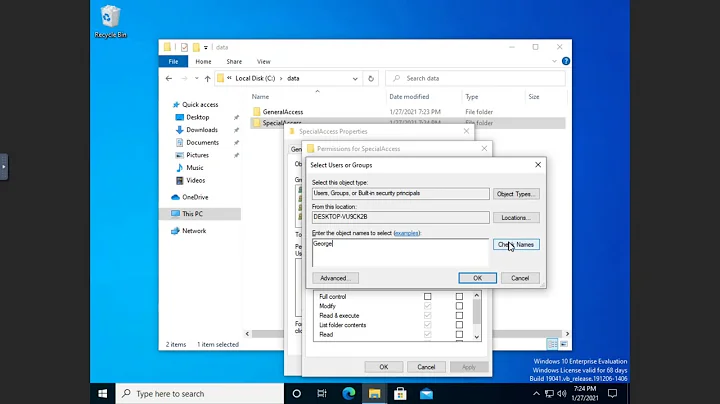
With SetACL you could set such permissions like this:
SetACL -on PathToDirectory -ot file -actn ace -ace n:UserOrGroup;p:list_dir,read_dacl;i:so
Related videos on Youtube
Chum
Updated on September 17, 2022Comments
-
Chum over 1 year
Is it possible to create a security group that can read who has permission to do what on NTFS folders but without granting Full Control or letting the group open files within those folders?
-
Chum about 13 yearsThank you for the advice. Will test. Your SetACL tool looks interesting also.
-
Helge Klein about 13 yearsPlease consider marking useful and/or correct answers as such (at the left of each answer).
-
Chum about 13 yearsDone - thanks again. When my rep goes up I will upvote your answer too. :)
-
Dogmatixed about 13 yearswhat is the difference between List Folder and Traverse Folder in this context?
-
Helge Klein about 13 yearsPlease open a new thread for new questions. Anyway, here is the answer: "For folders: The Traverse Folder permission applies only to folders. This permission allows or denies the user from moving through folders to reach other files or folders, even if the user has no permissions for the traversed folders. Traverse Folder takes effect only when the group or user is not granted the Bypass Traverse Checking user right. The Bypass Traverse Checking user right checks user rights in the Group Policy snap-in." [From support.microsoft.com/kb/308419]
![Linux Read Only Problem On NTFS | How to Enable Write Permission on NTFS in Ubuntu [HINDI] | azvish](https://i.ytimg.com/vi/eFvj7V-sNYk/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLAoTaPg2llJzvn2c0LT8n-HZZzaUQ)