How does Google Chrome store passwords?
Solution 1
You seem to be curious specifically about the key used to encrypt the passwords in Chrome.
The answer is:
Every password is encrypted with a different random key.
And then the encrypted password is stored in the SQLite database file:
%LocalAppData%\Google\Chrome\User Data\Default\Login Data
You can use something like SQLite Database Browser or SQLite Maestro to view it. Here's a snippet from my Login Data file:
origin_url username_value password_value
======================================== ============== ========================
http://thepiratebay.org/register [email protected] 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000BB0E1F4548ADC84A82EC0873552BCB460000000002000000000003660000C0000000100000006811169334524F33D880DE0C842B9BBB0000000004800000A00000001000000043C8E23979F5CC5499D73610B969A92A08000000EE07953DEC9F7CA01400000098B5F0F01E35B0DC6BBAFC53A9B1254AC999F4FA
You'll notice the password is an encrypted blob of data. The approximate algorithm to encrypt a new password is:
- generate a new random session key
- encrypt the password with the session key
- encrypt the session key with the user's RSA public key
- generate a Message Authentication Code (HMAC) for the encrypted data
- concatenate the encrypted session key, the encrypted password, and the MAC
And Chrome saves that blob to its SQLite database.
But to answer your question: Where does the encryption key come from?
Each password is encrypted with a different randomly generated key
The Technical Details
Of course i left out the technical details. Chrome does not encrypt your passwords itself. Chrome does not have a master key used to encrypt anything. Chrome does not do the encryption. Windows does.
There is a Windows function, CryptProtectData, which is used to encrypt any arbitrary data you like. The details of calling it is less important. But if i invent a pseudo-language that somewhat can be decipherable as any programming languge, Chrome calls:
CryptProtectData(
{ cbData: 28, pbData: "correct battery horse staple" },
"The password for superuser.com and all the glee therein",
null, //optional entropy
null, //reserved
null, //prompt options
0, //flags
{ cbData: pbData: }); //where the encrypted data will go
So the password:
-
Plaintext:
correct battery horse staple -
Encrypted:
01000000D08C9DDF0115D1118C7A00C04FC297EB01000000BB0E1F4548ADC84A82EC0873552BCB460000000002000000000003660000C0000000100000006811169334524F33D880DE0C842B9BBB0000000004800000A00000001000000043C8E23979F5CC5499D73610B969A92A08000000EE07953DEC9F7CA01400000098B5F0F01E35B0DC6BBAFC53A9B1254AC999F4FA
You'll notice that i never needed to supply a password. That is because Windows takes care of all of that. In the end:
- a random password is generated to encrypt the password
- that password is encrypted with a random password
- that password is encrypted with your Windows password
So the only way for someone to know your password is if they know your password.
Solution 2
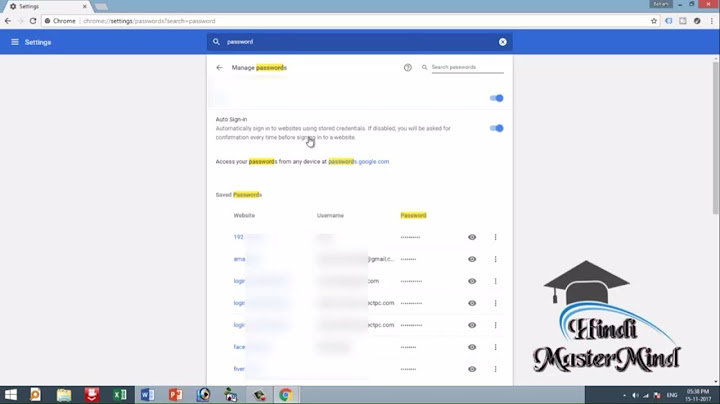
The passwords are encrypted and stored in a SQLite database:
The important piece here is
CryptProtectData, which is a Windows API function for encrypting data. Data encrypted with this function is pretty solid. It can only be decrypted on the same machine and by the same user that encrypted it in the first place.
Solution 3
Google Chrome encrypts passwords and stores them in SQLite DB but they could be easily viewed with the special password recovery applications such as ChromePass (http://www.nirsoft.net/utils/chromepass.html) or SecurePassword Kit (http://www.getsecurepassword.com/)
Solution 4
They are "encrypted" but it's a reversable encryption. Chrome has to send the raw password to the site it was stored for, so if Chrome can decrypt and use it, so can other people. Storing passwords is never 100% safe.
Solution 5
On the Mac, the equivalent to the CryptProtectData function in Windows is to access the password for "Chrome Safe Storage" in OS X's Keychain.
Related videos on Youtube
Óscar
Updated on September 17, 2022Comments
-
Óscar almost 2 years
Are they encrypted in disk? How? Are they safe, for example, in the event of someone booting from a Live CD and mounting the hard disk?
How is the encryption key generated? Is it different in Windows and Linux?
-
dskrvk over 6 yearsRelated: askubuntu.com/q/525019/472560
-
 Dan Dascalescu over 3 yearsNote that Google refused to implement a master password (as Firefox has) because it would create a false sense of security, and there are tools like Chromepass that can decrypt the passwords database, provided the user is logged in.
Dan Dascalescu over 3 yearsNote that Google refused to implement a master password (as Firefox has) because it would create a false sense of security, and there are tools like Chromepass that can decrypt the passwords database, provided the user is logged in.
-
-
Óscar about 14 yearsBut which is the encryption key?
-
Óscar about 14 yearsBut how is the encryption key generated? Depending on this I would consider the scheme more or less secure. And what about Linux?
-
Pylsa about 14 yearsCheck the answer of sblair. Note that there is a possibility of decryption, no matter how it is stored. With the proper software, anyone could decrypt it. When you have logged into your Windows account until the moment you log out, your passwords are completely usable and completely viewable. Just indicating that there is not a 100% safe solution of storing browser passwords.
-
Óscar about 14 yearsWell, if for example the encryption key is my password in a Linux system then the password database cannot be decrypted without knowing it (or by brute force).
-
Pylsa about 14 yearsNo but if your computer is hijacked/infected, browser passwords could easily be recovered without you noticing. Once again, all I'm pointing out is that there's no 100% failproof password storage for browsers... Just answering your question about their safety.
-
Óscar about 14 yearsWell there nothing 100% secure, but there are schemes more secure than others. This is why I would like to know which is the master password that Google Chrome is using.
-
Pylsa about 14 yearsThere is no "master password".
CryptProtectDatais a Windows API, Windows actually does all the encryption and retrieval, the encryption key is dependent on your user account and system. -
Óscar about 14 yearsWell by master password I meant the encryption key (the password used to encrypt the other passwords). How is it generated from the user account and system data?
-
Pylsa about 14 yearsThis should provide you with an explanation of its workings: msdn.microsoft.com/en-us/library/ms995355.aspx
-
user1686 about 14 years@Óscar: On Windows,
CryptProtectDatauses your Windows credentials (not the password, but some other data) as the key. AFAIK, it's the same function used to protect your certificates, network credentials and all that stuff. -
user1686 about 14 years@Óscar: On Linux,
Encryptor::EncryptStringdoes not do anything. There seems to be code for using GNOME Keyring and KDE Wallet. -
 Michael Hampton over 11 yearsCorrect. On Linux, KDE Wallet, GNOME Keyring, or one other supported native password store (which I forget offhand) is used instead.
Michael Hampton over 11 yearsCorrect. On Linux, KDE Wallet, GNOME Keyring, or one other supported native password store (which I forget offhand) is used instead. -
rogerdpack over 11 yearsso...it seems it is possible to have another separate app that basically snoops your chrome passwords, given that you're already logged in and it's running as you?
-
Ian Boyd almost 11 years@rogerdpack It absolutely is correct that once you type in your encryption password, that other applications can access those stored passwords (which is true of all encryption systems).
-
brunoais over 10 yearsHow does chrome know the key to be able to use it to decript the stored password, then?
-
Ian Boyd over 10 years@brunoais Chrome does not know the key used to encrypt passwords. Chrome does not decrypt them - Windows does.
-
brunoais over 10 yearsAh, ok. So if a malicious program gets into the computer the passwords are completely available to that program, right?
-
Ian Boyd over 10 years@brunoais Only if you've typed in your password. Unfortunately this is a fundamental limitation of encryption: once data is decrypted it is decrypted.
-
Colonel Panic over 8 yearsWhere is the database?
-
Colonel Panic over 8 yearsThanks. Chrome stopped my remembering my passwords (it still offered to save them, but never recalled them), I figured the password database was corrupted. Solved by deleting
%LocalAppData%\Google\Chrome\User Data\Default\Login Data -
 pythonian29033 almost 8 yearswait! so theoretically: if chrome uses the win API func 'CryptProtectData' then I just have to find the polar opposite function 'DecryptUnprotectData' to undo it, that I can probably find in a .NET lookup table somewhere? or just google?
pythonian29033 almost 8 yearswait! so theoretically: if chrome uses the win API func 'CryptProtectData' then I just have to find the polar opposite function 'DecryptUnprotectData' to undo it, that I can probably find in a .NET lookup table somewhere? or just google? -
Ian Boyd almost 8 years@pythonian29033
CryptUnprotectData. You'll also have to know the user's Windows password. If you already know your Windows password, you can dump them using a NirSoft tool. Or you could just - you know - visit the website in Chrome. -
 pythonian29033 almost 8 years@IanBoyd but I mean programatically; if my script/program is run in the current (or should I say 'Victim'`s) user context, then no password is needed I just have to get the user's permission, which can be done a million ways and that would probably get me the plain text password? Not really very safe is it
pythonian29033 almost 8 years@IanBoyd but I mean programatically; if my script/program is run in the current (or should I say 'Victim'`s) user context, then no password is needed I just have to get the user's permission, which can be done a million ways and that would probably get me the plain text password? Not really very safe is it -
 pythonian29033 almost 8 years@ColonelPanic it's somewhere in the
pythonian29033 almost 8 years@ColonelPanic it's somewhere in theUser Data(or equivalent) directory inside the Chrome folder, it's a sqlite db file namedLogin DataorUser Dataor similar -
Ian Boyd almost 8 years@pythonian29033 Yes, being on the other side of the security boundary means you are on the other side of the security boundary. Applications that save passwords (like Kneepass, OnePass, Chrome, Internet Explorer, FireFox, Opera, Lynx, Outlook, Remote Desktop Connection, Exchange) have the same issue: If you know the user's password you can access the user's passwords.
-
MrMas over 4 yearsBitwarden is one example of an app that does this for you (may still use system encryption libraries) and users a separate password which is used to decrypt your data. Bitwarden has a setting that says how often you have to enter your password (every time, if you'd like). It stores all the passwords locally and decrypts locally.
-
user43968 almost 4 yearsThx, really nice explanation !!! Information provided here seems still up-to-date. But I made a small sample app to decrypt my Login Data file. It still work on some password but for other (maybe the most recent one) I notice that password value is shorter and can't be decrypted with unprotectdata Any update on this ?
-
Ian Boyd over 3 years@MrMas Windows also has the option to require you to enter your password in order to access saved passwords. But BitWarden will have the same issue as every other password manager (including Windows's own). Once you type in your master password: you can then access the saved password - and the "you" also includes malicious apps running as you.
-
Ramhound almost 3 yearsIf you have a new question, please ask it by clicking the Ask Question button. Include a link to this question if it helps provide context.
-
Community almost 3 yearsPlease provide additional details in your answer. As it's currently written, it's hard to understand your solution.
-
ruief about 2 yearsAll encryption is reversible. That's the whole point.