How does Windows Event forwarding work with non domain computers? (certificates)
Solution 1
The Web Services Management Protocol Extensions for Windows Vista protocol documentation is what you're looking for if you really want to use your own code in place of WinRM. It looks like a non-trivial protocol to implement.
Solution 2
i'm also in a similar situation, i found this msdn page that talks about setting up collectors in non domain situations
https://msdn.microsoft.com/en-us/library/windows/desktop/bb870973(v=vs.85).aspx
Related videos on Youtube
Juanjo Daza
Updated on September 18, 2022Comments
-
 Juanjo Daza over 1 year
Juanjo Daza over 1 yearIn reasearching this question I've looked at the following documents and none of them describe the options or flexibility of the event collector service.
- Microsoft's Event Collector Service on Technet (too procedural, I'm just looking for how it works)
- Microsoft/ MSDN Source initiated Subscription (again not an overview of how it works)
- This configuration guide by a 3rd party (omits non-domain computers)
The scenario I'm trying to address is
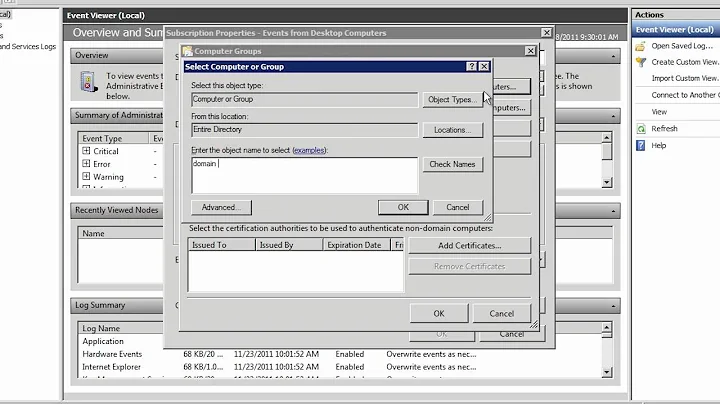
- Many non-domain computers need to send events to a central server for analysis and reporting
- The preferred transport is HTTP or HTTPS
- The service needs to authenticate before sending with either a username/password or a certificate
- The server must allow for up to 1,000 usernames or certificates to control who can forward events. The server must be able to determine who sent the event.
- Users can't "fake" an event for another user co-located on the same aggregate server
I suppose I can use fiddler to figure out how the server actually works, and write my own HTTP responder to handle these responses (and use my app instead of WinRM to receive the data), but handling non-domain connected machines is not documented clearly.
Could anyone help me understand how non-domain scenarios work, what the certificate should look like (EKU, etc), and ideally what is required to use my own code in place of the default WinRM
-
 Admin over 10 yearsAt the risk of being unhelpful, the easier solution (that I can't imagine any technical reason for not being the preferred solution) is to convert your non-domain computers to domain computers. Seriously, workgroups are literally good for nothing.
Admin over 10 yearsAt the risk of being unhelpful, the easier solution (that I can't imagine any technical reason for not being the preferred solution) is to convert your non-domain computers to domain computers. Seriously, workgroups are literally good for nothing. -
 Admin over 10 yearsAll of these servers and workstations are owned by people and companies that have no association (business or otherwise) with each other. I'm just the tech staff who wants to monitor events, and delegate access to a customer's logs to one of my peers... WITHOUT having to RDP in, etc. But thanks for reading the question @HopelessN00b
Admin over 10 yearsAll of these servers and workstations are owned by people and companies that have no association (business or otherwise) with each other. I'm just the tech staff who wants to monitor events, and delegate access to a customer's logs to one of my peers... WITHOUT having to RDP in, etc. But thanks for reading the question @HopelessN00b -
 Admin over 10 yearsOh, you poor fellow. That sounds... utterly horrific. I'll see what I can dig up.
Admin over 10 yearsOh, you poor fellow. That sounds... utterly horrific. I'll see what I can dig up. -
 Admin over 10 yearsI'm about to open a ticket with MSFT for this as well. I'll share the results as I get them
Admin over 10 yearsI'm about to open a ticket with MSFT for this as well. I'll share the results as I get them -
 Admin over 10 yearsI'm not sure if this will get you any closer, but have a look at this 3rd party: sumologic.com/_downloads/… -- I've been digging into them some lately to see what they offer and this might be worth a look for you.
Admin over 10 yearsI'm not sure if this will get you any closer, but have a look at this 3rd party: sumologic.com/_downloads/… -- I've been digging into them some lately to see what they offer and this might be worth a look for you. -
 Admin about 5 years@aL3891 has the right answer. An existing PKI is required since self-signed certs are not allowed.
Admin about 5 years@aL3891 has the right answer. An existing PKI is required since self-signed certs are not allowed.