How is it possible to list all folders that a particular user/group has permissions on?
Solution 1
Looks like there is no simple tool for this. I ended up going with a combination of getting a report from DumpSec and searching for Devs with FINDSTR.
And yes, I know there are dozens of equally good solutions, but those were the tools I was thinking of when I decided to give up the search for a one-step strategy.
Solution 2
I found a forum entry that may help.
Here is an excerpt:
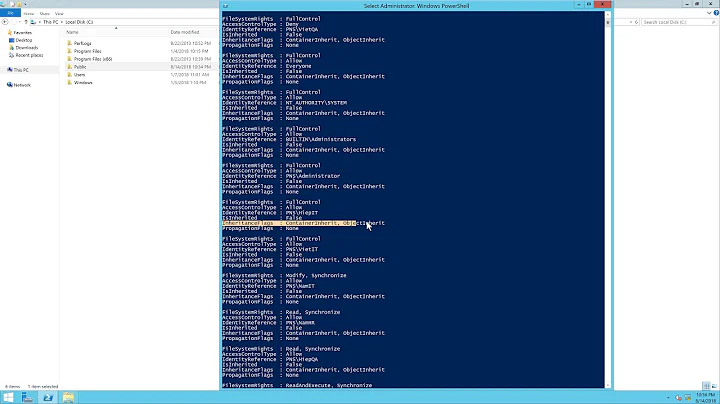
if (($args.Count) -eq 2) {
$dir = $args[0]
if ((Test-Path $dir) -eq $true) {
$script:FoldersFound = New-Object System.Collections.ArrayList
$GroupName = $args[1]
$folders = Get-ChildItem $dir -Recurse | Where-Object {$_.PSIsContainer}
foreach($folder in $folders) {
$ACL = Get-Acl -Path $folder.FullName
foreach($ACE in $ACL.access) {
if (($ACE.IdentityReference) -like "*\$GroupName") {
if (($ACE.IsInherited) -eq $false) {
$FoldersFound.Add($folder.FullName) | Out-Null
break
}
}
}
}
$FoldersFound.Sort()
foreach($folder in $FoldersFound) {
Write-Host $folder
}
}
} else {
Write-Host "Syntax:" $MyInvocation.MyCommand.Name """path""" """Group Name"""
}
Save the above code as <filename>.ps1, and run it from the PowerShell prompt with two arguments: "Folder path" followed by "group name."
Example: Navigate to the folder where you saved the script, and type the following, where <filename> is (obviously) the name you gave the file, and substitute the path and group name with your own:
.\<filename>.ps1 "C:\Users" "Administrators"
Now mind you, there is no error handling in the script, so it does not take care of access denied errors or too long path names, for example.
Credit goes to Andreas Hultgren, MCTS, MCITP.
Solution 3
Sysinternals' AccessEnum might help do what you want. It will enumerate the permissions on your directories. It doesn't exactly show whether the permissions are explicit or inherited, but it will show you all directories (and files) whose permissions differ from their parent. This probably gets you the same information. It can also enumerate permissions registry keys in the same manner.
You might also be interested in AccessChk (command line) and ShareEnum (like AccessEnum for your file shares).
Related videos on Youtube
bhaskar
Former Community Manager at Stack Exchange (August 2013-November 2017). My posts from before or after that time period (and, like, a bunch of the ones from during it, too) should not be considered "official" in any way. Joel: I have all these opinions ... and no outlet for them! Josh: Have you tried yelling them at the Internet? Joel: Almost exclusively! And yet problems still persist! -"The Grand Opining", HijiNKS ENSUE, by Joel Watson "On two occasions I have been asked, 'Pray, Mr. Babbage, if you put into the machine wrong figures, will the right answers come out?' ... I am not able rightly to apprehend the kind of confusion of ideas that could provoke such a question." -Charles Babbage Hofstadter's Law: It always takes longer than you expect, even when you take into account Hofstadter's Law. -Douglas Hofstadter, Gödel, Escher, Bach: An Eternal Golden Braid
Updated on September 17, 2022Comments
-
bhaskar over 1 year
Is it possible to list all folders/files that a given group has explicit permissions on, for a machine running Windows Server 2003? If so, how? It would be nice to see inherited permissions as well, but I could do with just explicit permissions.
A little background: I'm trying to update groups/permissions on a test server. One of the groups,
Devs, wasn't implemented correctly when it was created, and my goal is to remove it from the system. It has been replaced byLeadDevelopers, which has permissions on many — but naturally not all — of the same folders. I want to make sure that I don't accidentally orphan any folders or cause any other issues when I removeDevs. It did have some admin-level permissions.EDIT: The answers so far — at least
*caclsandAccessEnum— provide a way to find out which groups/users have permissions on known directories/files. I actually want the reverse of this behavior: I know the group, and I'm looking for the directories/files for which the group has permissions. Also, as I noted in a comment, theDevsgroup is not itself a member of any other group. -
 TheModularMind almost 14 yearsAccessEnum is probably your best bet (=1), but is still not a silver bullet, unfortunately. For your specific scenario it should help as it will highlight exceptions to the normal inhertiance, where Devs may have been given explicit permissions. Hopefully you are also taking into account nested group membership, so if Devs is a member of AllGeeks, you need to make sure LeadDevs is also in there or is given permissions at the same places as AllGeeks
TheModularMind almost 14 yearsAccessEnum is probably your best bet (=1), but is still not a silver bullet, unfortunately. For your specific scenario it should help as it will highlight exceptions to the normal inhertiance, where Devs may have been given explicit permissions. Hopefully you are also taking into account nested group membership, so if Devs is a member of AllGeeks, you need to make sure LeadDevs is also in there or is given permissions at the same places as AllGeeks -
bhaskar almost 14 years@AdamV, fortunately, I know neither
DevsnorLeadDevelopersis a member of another group, but it's definitely a good point to keep in mind.