How to connect to a L2TP VPN given some info from a sysadmin
Try:
conn tab-vpn
...
rightid=192.168.122.2
in /etc/ipsec.conf
The rightid parameter can be used to specify the IP address that the server identifies itself as (ie. it's LAN IP address rather than the public IP address of the router).
If the expected IP address and the IP address that the server identifies as don't match then ipsec abandons the connection attempt.
Related videos on Youtube
Asfand Qazi
Updated on September 18, 2022Comments
-
Asfand Qazi almost 2 years
I have been given some details of a VPN I am meant to connect to, and can't for the life of me get it to work under Kubuntu.
The info I have been given is (fake values substituted where appropriate of course):
I have configured a new VPN account for you on our server.
Your login details are as follows:
IP address: 1.2.3.4 username: myfullname password: wordpass shared secret: XXXXXXXXXXThe connection type is L2TP.
Ensure that you select the option to send all traffic over the VPN.
I have tried 2 routes:
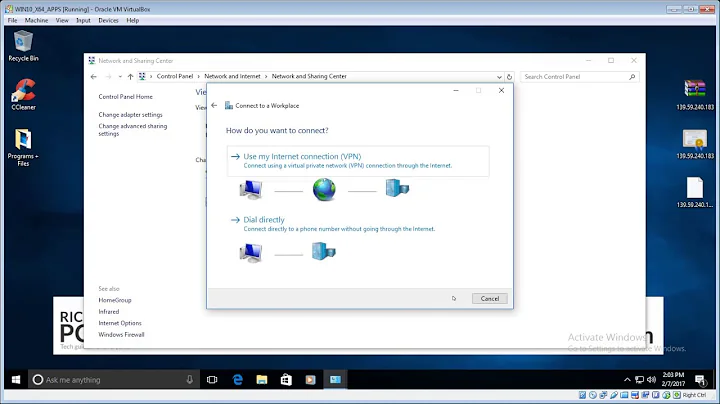
1) Using the KDE widget to configure this
2) Using config files to configure this
Using the widget:
I add the https://launchpad.net/~seriy-pr/+archive/network-manager-l2tp PPA, and install network-manager-l2tp.
Then, I add an L2TP connection and I come across the following fields (which I fill in): Gateway (1.2.3.4) User name: (myfullname) Password: (wordpass)
Then I go into IPsec Settings, and (after checking "Enable IPSec tunnel to L2TP host): Group Name Gateway ID Pre-shared Key
I fill in Pre-shared Key with XXXXXXXXXX, and click OK.
Then I try to connect, and get the following error:
"Necessary secrets for the VPN connection were not provided."
Using config files, and using https://www.elastichosts.com/support/tutorials/linux-l2tpipsec-vpn-client/ as a guide, I do the following:
I add the following to /etc/ipsec.conf:
config setup .... protostack=netkey plutoopts="--interface=wlan0" .... conn tab-vpn authby=secret pfs=no auto=add keyingtries=3 dpddelay=30 dpdtimeout=120 dpdaction=clear rekey=yes ikelifetime=8h keylife=1h type=transport left=%defaultroute leftnexthop=%defaultroute leftprotoport=17/1701 right=1.2.3.4I add the following to /etc/ipsec.secrets:
%any 1.2.3.4: PSK "XXXXXXXXXX"Then when I restart ipsec with:
sudo ipsec auto --up tab-vpnI get:
104 "tab-vpn" #1: STATE_MAIN_I1: initiate 003 "tab-vpn" #1: ignoring Vendor ID payload [MS NT5 ISAKMPOAKLEY 00000009] 003 "tab-vpn" #1: received Vendor ID payload [RFC 3947] method set to=115 003 "tab-vpn" #1: received Vendor ID payload [draft-ietf-ipsec-nat-t-ike-02_n] meth=106, but already using method 115 003 "tab-vpn" #1: ignoring Vendor ID payload [FRAGMENTATION] 003 "tab-vpn" #1: ignoring Vendor ID payload [MS-Negotiation Discovery Capable] 003 "tab-vpn" #1: ignoring Vendor ID payload [IKE CGA version 1] 106 "tab-vpn" #1: STATE_MAIN_I2: sent MI2, expecting MR2 003 "tab-vpn" #1: NAT-Traversal: Result using draft-ietf-ipsec-nat-t-ike (MacOS X): both are NATed 108 "tab-vpn" #1: STATE_MAIN_I3: sent MI3, expecting MR3 003 "tab-vpn" #1: we require peer to have ID '1.2.3.4', but peer declares '192.168.122.2' 218 "tab-vpn" #1: STATE_MAIN_I3: INVALID_ID_INFORMATIONI and the server in question are behind the same firewall.
It SHOULD allow me to connect so I can move onto setting up the xl2tpd.conf options, but I don't get that far.
Help?
-
 No Time about 10 yearsAre you trying to put any number in for the IP? (where you have %any 1.2.3.4) That seems to be where you are having issues
No Time about 10 yearsAre you trying to put any number in for the IP? (where you have %any 1.2.3.4) That seems to be where you are having issues -
 Mladen B. about 10 yearsIP address (1.2.3.4 in your case) is not the Gateway info. It is the ip address of a VPN dial-in point (remote VPN server). Once you login with your credentials, most probably DHCP will automatically give you an appropriate IP address and the Gateway info.
Mladen B. about 10 yearsIP address (1.2.3.4 in your case) is not the Gateway info. It is the ip address of a VPN dial-in point (remote VPN server). Once you login with your credentials, most probably DHCP will automatically give you an appropriate IP address and the Gateway info. -
Asfand Qazi about 10 yearsUnfortunately, I've left the place of work where I needed this, so I have no way of testing it. If a few people can confirm that any of the techniques work, I'll accept the best answer.
-