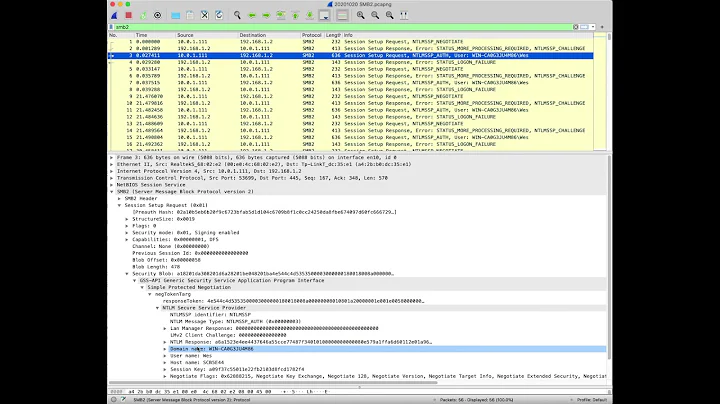
How to decode traffic as NTLM protocol in Wireshark?
I'm not quite sure which ports NTLMSSP actually uses, but you could try this Lua-script to register the NTLMSSP-dissectors to your custom port.
local tcp_port_table = DissectorTable.get("tcp.port")
local tcp_ntlmssp_dis = tcp_port_table:get_dissector(445)
tcp_port_table:add(6901, tcp_ntlmssp_dis)
Save this to a file - e.g. ntlmssp.lua - and tell Wireshark to load it, e.g.
$ wireshark -X lua_script:ntlmssp.lua -r trace.pcap
You might have to change the port 445 to what's really needed or register additional ports by adding additional lines like tcp_port_table:get_dissector(4711). If you need UDP as well, do the same for UDP.
Related videos on Youtube
Jury
Updated on September 18, 2022Comments
-
Jury over 1 year
I'm trying to debug
NTLMauthentication issue. One of my ideas was to capture the network traffic and look thougth it. In my caseNTLMauthentication is going over non-stardart port (6901). Of course, Wireshark can't detect it. But there is noNTLM(NTLMSSP) protocol in the list inDecode asmenu. I can't do like here.
Is there a way to ask Wireshark to decode traffic asNTLM?
Or I need to modify captured traffic, e.g. changeTCPport or somehow another?-
Marki555 almost 9 yearsWireshark does support NTLM SSP protocol wireshark.org/docs/dfref/n/ntlmssp.html
-
Jury almost 9 yearsIt supports, but how to decode raw byte traffic as
NTLM? -
 Michael Hampton almost 9 yearsHave you got a very old version of Wireshark then?
Michael Hampton almost 9 yearsHave you got a very old version of Wireshark then? -
Jury almost 9 yearsI checked for updates rigth now again...
-
-
 Doug over 6 yearsI have been trying to get this to work, and have not been successful. What is the proper port for NTLMSSP? If this technique works, it doesn't appear its 445, and I've tried a bunch of others.
Doug over 6 yearsI have been trying to get this to work, and have not been successful. What is the proper port for NTLMSSP? If this technique works, it doesn't appear its 445, and I've tried a bunch of others.