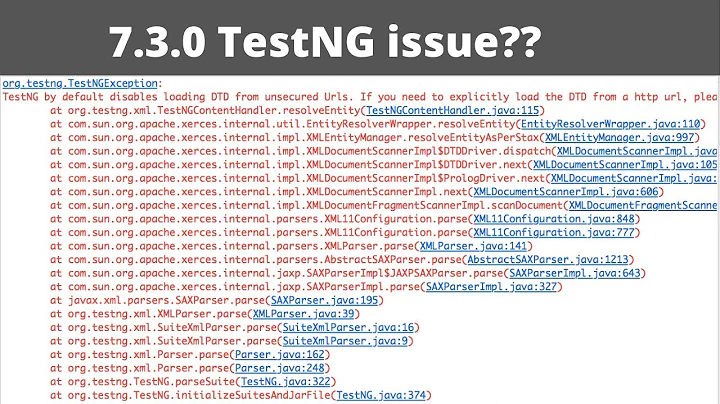
How to disable DTD fetching using JAXB2.0
Solution 1
Below is sample code that demonstrates how to get a JAXB (JSR-222) implementation to use your SAX parser:
import java.io.FileReader;
import javax.xml.XMLConstants;
import javax.xml.bind.JAXBContext;
import javax.xml.bind.Unmarshaller;
import javax.xml.parsers.SAXParserFactory;
import javax.xml.transform.sax.SAXSource;
import org.xml.sax.InputSource;
import org.xml.sax.XMLReader;
public class Demo {
public static void main(String[] args) throws Exception {
JAXBContext jc = JAXBContext.newInstance(Foo.class);
SAXParserFactory spf = SAXParserFactory.newInstance();
spf.setFeature(XMLConstants.FEATURE_SECURE_PROCESSING, true);
XMLReader xmlReader = spf.newSAXParser().getXMLReader();
InputSource inputSource = new InputSource(new FileReader("input.xml"));
SAXSource source = new SAXSource(xmlReader, inputSource);
Unmarshaller unmarshaller = jc.createUnmarshaller();
Foo foo = (Foo) unmarshaller.unmarshal(source);
System.out.println(foo.getValue());
}
}
Solution 2
Building on the answers from @blaise-doughan and @aerobiotic, here is a solution that worked for me:
import java.io.FileReader;
import javax.xml.XMLConstants;
import javax.xml.bind.JAXBContext;
import javax.xml.bind.Unmarshaller;
import javax.xml.parsers.SAXParserFactory;
import javax.xml.transform.sax.SAXSource;
import org.xml.sax.InputSource;
import org.xml.sax.XMLReader;
public class Demo2 {
public static void main(String[] args) throws Exception {
JAXBContext jc = JAXBContext.newInstance(MyBean.class);
SAXParserFactory spf = SAXParserFactory.newInstance();
spf.setFeature("http://apache.org/xml/features/nonvalidating/load-external-dtd", false);
spf.setFeature("http://xml.org/sax/features/validation", false);
XMLReader xmlReader = spf.newSAXParser().getXMLReader();
InputSource inputSource = new InputSource(
new FileReader("myfile.xml"));
SAXSource source = new SAXSource(xmlReader, inputSource);
Unmarshaller unmarshaller = jc.createUnmarshaller();
MyBean foo = (MyBean) unmarshaller.unmarshal(source);
}
}
Solution 3
In answer to the question "How to disable DTD fetching using JAXB2.0".
@sameer-puri links to https://cheatsheetseries.owasp.org/cheatsheets/XML_External_Entity_Prevention_Cheat_Sheet.html#SAXTransformerFactory which answers the question as follows:
JAXB Unmarshaller
Since a javax.xml.bind.Unmarshaller parses XML and does not support any flags for disabling XXE, it's imperative to parse the untrusted XML through a configurable secure parser first, generate a source object as a result, and pass the source object to the Unmarshaller. For example:
//Disable XXE
SAXParserFactory spf = SAXParserFactory.newInstance();
spf.setFeature("http://xml.org/sax/features/external-general-entities", false);
spf.setFeature("http://xml.org/sax/features/external-parameter-entities", false);
spf.setFeature("http://apache.org/xml/features/nonvalidating/load-external-dtd", false);
//Do unmarshall operation
Source xmlSource = new SAXSource(spf.newSAXParser().getXMLReader(),
new InputSource(new StringReader(xml)));
JAXBContext jc = JAXBContext.newInstance(Object.class);
Unmarshaller um = jc.createUnmarshaller();
um.unmarshal(xmlSource);
Related videos on Youtube
Nick
Updated on July 29, 2021Comments
-
Nick over 2 years
I'm trying to use JAXB to unmashall some XML which I used xjc to create in the first place. I don't want to do any validation on the unmarshalling, but even though I have disabled the validation according to the JAXB documentation with
u.setSchema(null);, but this hasn't prevented aFileNotFoundExceptionbeing thrown when it tries to run and can't find the schema.JAXBContext jc = JAXBContext.newInstance("blast"); Unmarshaller u = jc.createUnmarshaller(); u.setSchema(null); return u.unmarshal(blast)I've seen similar questions for disabling SAX parsing from validation by setting the apache property
http://apache.org/xml/features/validation/schematofalse, but I can't get the Unmarshaller to use my own sax parser. -
aerobiotic almost 12 yearsThat didn't work for me but these did: parser.setFeature("apache.org/xml/features/nonvalidating/load-external-dtd", false); parser.setFeature("xml.org/sax/features/validation", false);
-
 Sameer Puri over 7 yearsThis website explains how it can be blocked on any of the major Java frameworks.
Sameer Puri over 7 yearsThis website explains how it can be blocked on any of the major Java frameworks. -
 gihan-maduranga over 7 yearsThis worked for me.Also additionally added
gihan-maduranga over 7 yearsThis worked for me.Also additionally addedspf.setValidating(false);Thanks -
 ahmettolga over 4 yearsSeems that FEATURE_SECURE_PROCESSING is about entityExpansionLimit. Check the last part of the documentation docs.oracle.com/javase/1.5.0/docs/guide/xml/jaxp/…
ahmettolga over 4 yearsSeems that FEATURE_SECURE_PROCESSING is about entityExpansionLimit. Check the last part of the documentation docs.oracle.com/javase/1.5.0/docs/guide/xml/jaxp/… -
Graham Leggett over 3 yearsThis answers the question "how do I get the Unmarshaller to use my own sax parser", but does not answer the question "How to disable DTD fetching using JAXB2.0".




![HOW TO Remove Broken Impact Driver Bits - Don't Get Mad! [EASY PEASY]](https://i.ytimg.com/vi/dt0ld4uu5Ds/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLA3u3q-_L-8LXOyxh7fWGhM-nLyvw)
![B1 - Faded [Music Video] (Prod By G8Freq) | Link Up TV](https://i.ytimg.com/vi/SbeSddAMtFc/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLBctQ2C_ZzeLwUwAwR8WlBHgz676A)