How to dump memory image from linux system?
Solution 1
From the Forensic's Wiki: Tools:Memory Imaging
excerpt
Linux
/dev/mem
On older Linux systems, the program dd can be used to read the contents of physical memory from the device file /dev/mem. On recent Linux systems, however, /dev/mem provides access only to a restricted range of addresses, rather than the full physical memory of a system. On other systems it may not be available at all. Throughout the 2.6 series of the Linux kernel, the trend was to reduce direct access to memory via pseudo-device files. See, for example, the message accompanying this patch: http://lwn.net/Articles/267427/.
/dev/crash
On Red Hat systems (and those running related distros such as Fedora or CentOS), the crash driver can be loaded to create pseudo-device /dev/crash for raw physical memory access (via command "modprobe crash"). This module can also be compiled for other Linux distributions with minor effort (see, for example, http://gleeda.blogspot.com/2009/08/devcrash-driver.html). When the crash driver is modified, compiled, and loaded on other systems, the resulting memory access device is not safe to image in its entirety. Care must be taken to avoid addresses that are not RAM-backed. On Linux, /proc/iomem exposes the correct address ranges to image, marked with "System RAM".
Second Look: Linux Memory Forensics
This commercial memory forensics product ships with a modified version of the crash driver and a script for safely dumping memory using the original or modified driver on any given Linux system.
fmemfmem - github repofmem is kernel module that creates device /dev/fmem, similar to /dev/mem but without limitations. This device (physical RAM) can be copied using dd or other tool. Works on 2.6 Linux kernels. Under GNU GPL.
LiME - Linux Memory Extractor
Linux Memory Extractor (LiME) is a Loadable Kernel Module (LKM), which allows the acquisition of volatile memory from Linux and Linux-based devices, such as those powered by Android. The tool supports dumping memory either to the file system of the device or over the network.
I found this example of fmem in use, which seems to be the easiest way to dump memory for analysis purposes, you can no longer use /dev/mem after the 2.6.x kernels, as I understand it.
fmem Example
$ ./run.sh
...
----Memory areas: -----
reg00: base=0x000000000 ( 0MB), size= 1024MB, count=1: write-back
reg01: base=0x0c8800000 ( 3208MB), size= 2MB, count=1: write-combining
-----------------------
!!! Don't forget add "count=" to dd !!!
$ ls /dev/f*
/dev/fb0 /dev/fd0 /dev/fmem /dev/full /dev/fuse
$ sudo dd if=/dev/fmem of=/tmp/fmem_dump.dd bs=1MB count=10
10+0 records in
10+0 records out
10000000 bytes (10 MB) copied, 0.0331212 s, 302 MB/s
*Source: How can I dump all physical memory to a file?
LiME Example
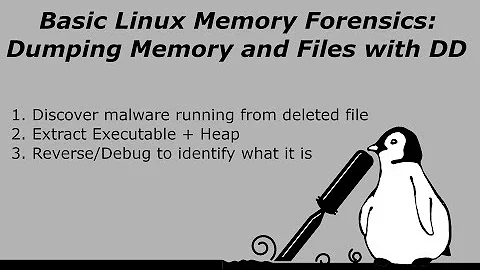
For analyzing volatile memory there's also this page, titled: Linux Memory Analysis. There's a thorough example in this video tutorial that shows the use of LiME and Volatility to collect a memory dump and then analyze it, extracting the user's Bash history from the memory dump.
What else?
There's also this U&L Q&A titled: How can I dump the full system memory? which has additional examples and information.
Solution 2
rekall
Check out the rekall framework, they have a linpmem application for this purpose: http://www.rekall-forensic.com/docs/Tools/index.html
The SANS rekall memory forensic cheatsheet has an example of how to dump memory under linux too:
# ./linpmem_2.0.1 -o linux.aff4
Related videos on Youtube
bakie
Updated on September 18, 2022Comments
-
bakie almost 2 years
I know to dump memory images in Windows. (eg-dumpit) But I don't know how to dump memory images in Linux.
I want to get memory images in Linux and from Linux to Linux with ssh connection or something.
How can I get in Linux?
-
casey over 10 yearsAre you trying to get memory from a running process, kernel memory or raw physical memory? All are available but methods for access differ. See /dev/kmem, /dev/mem, /proc/kcore, /proc/$pid/maps and /proc/$pid/mem .
-
 slm over 10 yearsTake a look at this SU Q&A: superuser.com/questions/164960/…
slm over 10 yearsTake a look at this SU Q&A: superuser.com/questions/164960/…
-
-
 phk over 7 yearsSome explanation would be nice.
phk over 7 yearsSome explanation would be nice.