How to exclude given lines in syslog-ng?
12,153
Solution 1
BEFORE:
SERVER:/etc/syslog-ng # tail -3 syslog-ng.conf
#
#
log { source(src); destination(/var/log/messages); };
SERVER:/etc/syslog-ng #
EDIT THE syslog-ng.conf FILE:
vi /etc/syslog-ng/syslog-ng.conf
AFTER:
SERVER:/etc/syslog-ng # tail -3 syslog-ng.conf
#log { source(src); destination(/var/log/messages); };
filter heartbeat_filter { not match("PFILTER-DROP") and not match("DST=192.168.202.255") and not match("PROTO=UDP"); };
log { source(src); filter(heartbeat_filter); destination(/var/log/messages); };
SERVER:/etc/syslog-ng #
RESTART SYSLOG-NG
/etc/init.d/syslog restart # or whatever you use to restart syslog-ng
# now check
ROTATE IF NEEDED
logrotate /etc/logrotate.conf
Solution 2
You can use a filter to match the program sending the message, in this case PFILTER-DROP, like this:
filter f_pfilterdrop {
program("PFILTER-DROP");
};
Then you include this filter in the log statement that writes to this log.
Solution 3
How can I extend this excluding rule to filter only those lines that contain: "DST=192.168.202.255" AND uses "udp" AND "PFILTER-DROP"?
Use something like:
filter demo_filter { program("PFILTER-DROP") and match("DST=192.168.202.255") and match("PROTO=UDP"); };
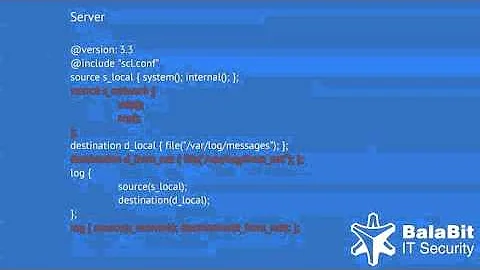
Related videos on Youtube
Author by
gasko peter
Updated on September 18, 2022Comments
-
gasko peter almost 2 years
I need to exclude a given line in the messages file:
Oct 25 04:09:23 SERVERNAME PFILTER-DROP: IN=ifeth4 OUT= MAC=ff:ff:ff:ff:ff:ff:AA:AA:AA:AA:AA:AA:AA:AA SRC=192.168.202.4 DST=192.168.202.255 LEN=238 TOS=0x00 PREC=0x00 TTL=64 ID=0 DF PROTO=UDP SPT=32776 DPT=705 LEN=218 Oct 25 04:09:23 SERVERNAME PFILTER-DROP: IN=ifeth4 OUT= MAC=ff:ff:ff:ff:ff:ff:AA:AA:AA:AA:AA:AA:AA:AA SRC=192.168.202.6 DST=192.168.202.255 LEN=183 TOS=0x00 PREC=0x00 TTL=64 ID=0 DF PROTO=UDP SPT=32770 DPT=700 LEN=163 Oct 25 04:09:23 SERVERNAME PFILTER-DROP: IN=ifeth4 OUT= MAC=ff:ff:ff:ff:ff:ff:AA:AA:AA:AA:AA:AA:AA:AA SRC=192.168.202.8 DST=192.168.202.255 LEN=176 TOS=0x00 PREC=0x00 TTL=64 ID=0 DF PROTO=UDP SPT=32768 DPT=714 LEN=156 Oct 25 04:09:23 SERVERNAME PFILTER-DROP: IN=ifeth4 OUT= MAC=ff:ff:ff:ff:ff:ff:AA:AA:AA:AA:AA:AA:AA:AA SRC=192.168.202.10 DST=192.168.202.255 LEN=175 TOS=0x00 PREC=0x00 TTL=64 ID=0 DF PROTO=UDP SPT=33628 DPT=715 LEN=155 Oct 25 04:09:23 SERVERNAME PFILTER-DROP: IN=ifeth4 OUT= MAC=ff:ff:ff:ff:ff:ff:AA:AA:AA:AA:AA:AA:AA:AA SRC=192.168.202.30 DST=192.168.202.255 LEN=185 TOS=0x00 PREC=0x00 TTL=64 ID=0 DF PROTO=UDP SPT=32770 DPT=713 LEN=165 Oct 25 04:09:23 SERVERNAME PFILTER-DROP: IN=ifeth4 OUT= MAC=ff:ff:ff:ff:ff:ff:AA:AA:AA:AA:AA:AA:AA:AA SRC=192.168.202.34 DST=192.168.202.255 LEN=237 TOS=0x00 PREC=0x00 TTL=64 ID=0 DF PROTO=UDP SPT=32781 DPT=704 LEN=217they are afaik heartbeat udp messages, but they aren't needed in the logs.
# rpm -qa | grep -i syslog-ng Security.syslog-ng-1.6.8.0-1 # uname -a Linux SERVERNAME 2.6.5-7.325-bigsmp #1 SMP Tue Jan 18 23:36:49 UTC 2011 i686 i686 i386 GNU/Linux # cat /etc/SuSE-release SUSE LINUX Enterprise Server 9 (i586) VERSION = 9 PATCHLEVEL = 4Q: How can I exclude these kind of messages from the /var/log/messages?
-
gasko peter over 11 yearsHow can I extend this excluding rule to filter only those lines that contain: "DST=192.168.202.255" AND uses "udp" AND "PFILTER-DROP"?
-
 Jenny D over 11 yearsI see somebody else already answered that - glad it seems to be working for you!
Jenny D over 11 yearsI see somebody else already answered that - glad it seems to be working for you! -
gasko peter over 11 yearsI tested it and didn't worked, sorry:D
-
devarni over 10 yearsI found that I needed to enclose those matches in parentheses to apply the AND condition properly, e.g.
not (match("PFILTER-DROP") and match("DST=192.168.202.255") and match("PROTO=UDP"));. Otherwise it seems to have more of an OR effect.