How to find source of 4625 Event ID in windows server 2012
Solution 1
Working solution i found here: https://github.com/DigitalRuby/IPBan
For Windows Server 2008 or equivalent, you should disable NTLM logins and only allow NTLM2 logins. On Windows Server 2008, there is no way to get the ip address of NTLM logins. Use secpol -> local policies -> security options -> network security restrict ntlm incoming ntlm traffic -> deny all accounts.
In RU version: Локальная политика безопасности -> Локальные политики -> Параметры безопасности -> Сетевая безопасность: ограничения NTLM: входящий трафик NTLM -> Запретить все учетные записи
Solution 2
I had the same type of events on a server. There were hundreds of login attempts with different user names but no process ID or IP address visible.
I'm pretty sure it was coming from RDP connections over the internet without network level authentication.
Solution 3
These are the hack attacks. Attackers' goal is to brute force your server's accounts/passwords.
I would suggest to install a simple Intrusion Detection System (IDS). You may want to consider RDPGuard (commercial), IPBan, evlWatcher. Myself I use Cyberarms IDDS. This one is simple, has an friendly interface (requires .NET Framework 4.0 though).
The idea is simple: IDS monitors your server's security log for the suspicious logon failure events. Then it soft-locks the IP address(es), the attempt came from. You can also configure a hard lock when the attempts from the soft-locked IPs continue.
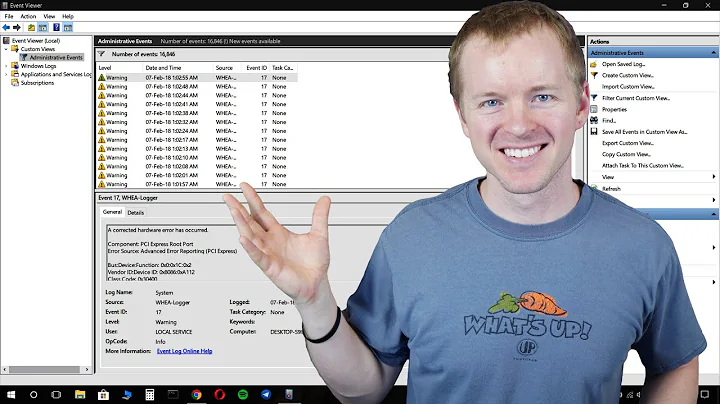
Related videos on Youtube
Mohsen Tavoosi محسن طاوسی
My job was about programing Microsoft Product(.NET,SQL Server) and PHP I can help you and also I may need your help. مشاوره تخصصی سئو توسط محسن طاوسی.در صورت نیاز به آموزش و خدمات و مشاوره و هرگونه راهنمایی درباره سئو، به وب سایت محسن طاوسی به آدرس Mohsentavoosi.com مراجعه نمایید.
Updated on September 18, 2022Comments
-
 Mohsen Tavoosi محسن طاوسی almost 2 years
Mohsen Tavoosi محسن طاوسی almost 2 yearsI have many audit failure with event ID 4625 and Logon type 3 in my event log.
Is this problem form my server(internal services or applications) ? Or this is brute force attack? Finally How can i find source of this logins and resolve problem?
This is detailed information in General tab:
An account failed to log on. Subject: Security ID: NULL SID Account Name: - Account Domain: - Logon ID: 0x0 Logon Type: 3 Account For Which Logon Failed: Security ID: NULL SID Account Name: aaman Account Domain: Failure Information: Failure Reason: Unknown user name or bad password. Status: 0xC000006D Sub Status: 0xC0000064 Process Information: Caller Process ID: 0x0 Caller Process Name: - Network Information: Workstation Name: test2 Source Network Address: - Source Port: - Detailed Authentication Information: Logon Process: NtLmSsp Authentication Package: NTLM Transited Services: - Package Name (NTLM only): - Key Length: 0 **And this is detailed information in Detail Tab:** + System - Provider [ Name] Microsoft-Windows-Security-Auditing [ Guid] {54849625-5478-4994-A5BA-3E3B0328C30D} EventID 4625 Version 0 Level 0 Task 12544 Opcode 0 Keywords 0x8010000000000000 - TimeCreated [ SystemTime] 2015-05-09T06:57:00.043746400Z EventRecordID 2366430 Correlation - Execution [ ProcessID] 696 [ ThreadID] 716 Channel Security Computer WIN-24E2M40BR7H Security - EventData SubjectUserSid S-1-0-0 SubjectUserName - SubjectDomainName - SubjectLogonId 0x0 TargetUserSid S-1-0-0 TargetUserName aaman TargetDomainName Status 0xc000006d FailureReason %%2313 SubStatus 0xc0000064 LogonType 3 LogonProcessName NtLmSsp AuthenticationPackageName NTLM WorkstationName test2 TransmittedServices - LmPackageName - KeyLength 0 ProcessId 0x0 ProcessName - IpAddress - IpPort --
Spongman about 9 yearssee here: serverfault.com/a/403638/242249
-
-
 Interface Unknown almost 7 yearsI wouldn't be so calm if I were you. These are the hack attempts.
Interface Unknown almost 7 yearsI wouldn't be so calm if I were you. These are the hack attempts. -
 Redoman about 6 yearscare to explain what those commands do?
Redoman about 6 yearscare to explain what those commands do? -
JoeCool over 4 yearsBlocked all NTLM attacks with your solution! Thank you even you brought it from that GitHub page. It's so charming you answered so!