How to open port for a specific IP address with firewall-cmd on CentOS?
199,515
Solution 1
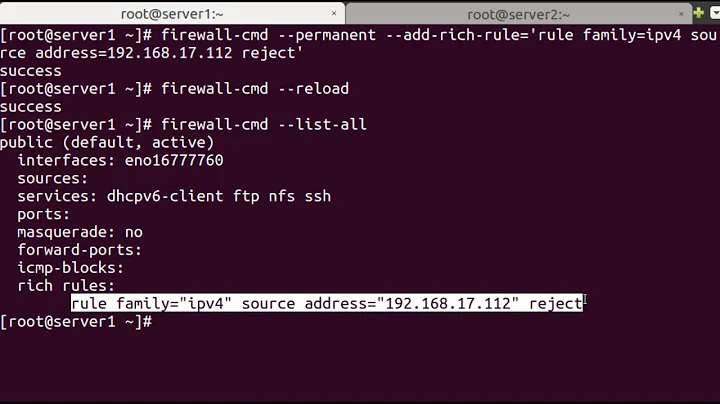
Try this command
firewall-cmd --permanent --zone=public --add-rich-rule='
rule family="ipv4"
source address="1.2.3.4/32"
port protocol="tcp" port="4567" accept'
Check the zone file later to inspect the XML configuration
cat /etc/firewalld/zones/public.xml
Reload the firewall
firewall-cmd --reload
Solution 2
Create a new zone to accommodate this configuration. FirewallD zones are defined by source addresses and by interfaces.
firewall-cmd --new-zone=special --permanent
firewall-cmd --reload
firewall-cmd --zone=special --add-source=192.0.2.4/32
firewall-cmd --zone=special --add-port=4567/tcp
Add --permanent of course to the latter two commands to make them permanent.
Related videos on Youtube
Author by
Michaël Perrin
Updated on September 18, 2022Comments
-
Michaël Perrin almost 2 years
I would like to open port
4567for the IP address1.2.3.4with thefirewall-cmdcommand on a CentOS 7.1 server.How can I achieve this, as the documentation I could find was too specific on this?
-
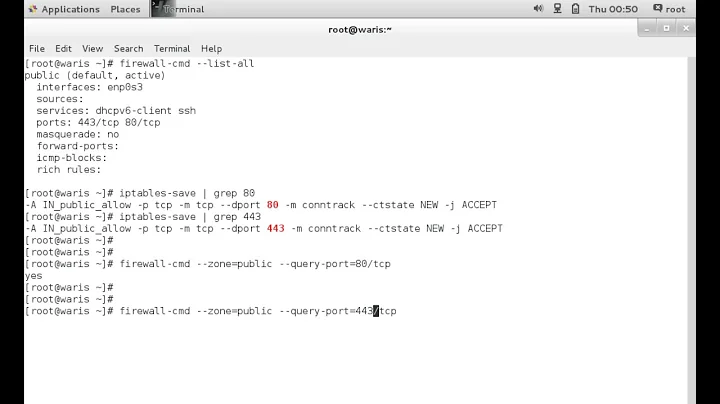
Takman over 3 yearsFirst install and start firewalld service
sudo yum install -y firewalld && sudo systemctl start firewalld. Then open port 80 and 443 (and ssh 22 for remote shell if needed) (use --permanent flag to keep changes after system reboot)sudo firewall-cmd --zone=public --permanent --add-port=80/tcp && sudo firewall-cmd --zone=public --permanent --add-port=443/tcp && sudo firewall-cmd --zone=public --permanent --add-port=22/tcp. Then reload firewalld service to activate new configurationsudo systemctl reload firewalld.
-
-
Michaël Perrin about 9 yearsThat's exactly what I was looking for, thanks for your useful and simple answer!
-
 Mike S about 8 yearsThe change won't take place immediately unless you subsequently run
Mike S about 8 yearsThe change won't take place immediately unless you subsequently runfilewall-cmd reload -
k00k about 8 yearsThe correct way to reload is actually:
firewall-cmd --reload -
 Basil A about 8 yearsI think you should be using single quotes after --add-rich-rule='rule family="ipv4" source address="1.2.3.4/32" port protocol="tcp" port="4567" accept'
Basil A about 8 yearsI think you should be using single quotes after --add-rich-rule='rule family="ipv4" source address="1.2.3.4/32" port protocol="tcp" port="4567" accept' -
 Brian Thomas over 7 yearsincidentally this is pretty much the ONLY WAY TO ADD IPV6 rules also, work to the wise, for those ready to dive in.
Brian Thomas over 7 yearsincidentally this is pretty much the ONLY WAY TO ADD IPV6 rules also, work to the wise, for those ready to dive in. -
totokaka over 6 yearsWhile this solution will work, @michael-hampton's solution is the most firewalld-esque way to do this. In my opinion, rich rules should be used as a last resort when there are no better ways to do something.
-
 Vasili Syrakis over 6 yearsI completed the RHCSA much after this answer, and I agree. Avoiding rich rules would lead to a more maintainable configuration down the line.
Vasili Syrakis over 6 yearsI completed the RHCSA much after this answer, and I agree. Avoiding rich rules would lead to a more maintainable configuration down the line. -
Achilles almost 6 yearsThis should be the accepted answer.
-
Orsiris de Jong about 5 yearsAgreed, this is the best answer IMHO. In order to list that zone, use
firewall-cmd --list-all-zones. Also, you may want to add--permanentto both --add statements. -
sykez about 4 yearsI agree with this as well, this should be the accepted answer.
-
Jesús Cota almost 4 yearsThis is perfect!
-
 Abdennour TOUMI over 2 yearsthis should be the accepted answer
Abdennour TOUMI over 2 yearsthis should be the accepted answer -
 Syco over 2 yearsI have a problem with this (maybe), the moment you add a source and a port to the special zone, it becomes active all the time for traffic coming from that source, doesn't matter if you are home, in the airport, or at starbucks. Does that make sense??
Syco over 2 yearsI have a problem with this (maybe), the moment you add a source and a port to the special zone, it becomes active all the time for traffic coming from that source, doesn't matter if you are home, in the airport, or at starbucks. Does that make sense?? -
basin about 2 yearsWhich set of rules would apply if source address is 192.0.2.4 and port is NOT 4567 ?
-
basin about 2 yearsI guess "default" which rejects connections even if "public" has some allowed ports. This is why "rich-rule" is a better answer.