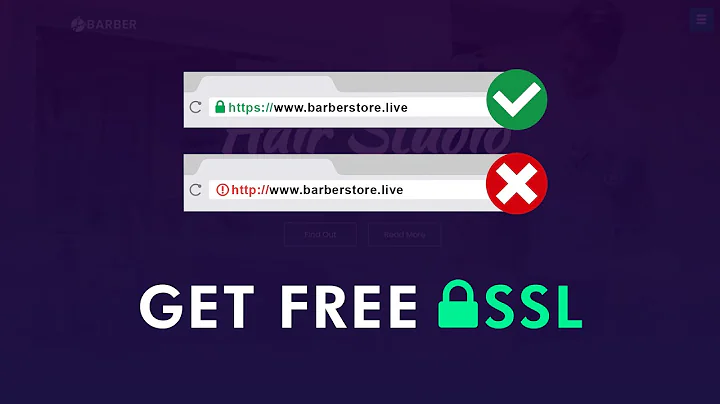
How to prevent access to website without SSL connection?
Solution 1
Unfortunately, the only general solution to this problem is to give your users the https:// only and make sure that they expect to use that only. It is ultimately the responsibility of the user to check that they are using SSL/TLS, as they expect.
Other solutions are vulnerable to man-in-the-middle attacks, even if the website only accepts SSL/TLS connections. Attackers could intercept the traffic to http://example.com (as requested by the user, even if example.com isn't even listening on that port) and replace it by making their own connection to https://example.com, proxy-ing it back to the user.
There was an OWASP rule against automatic redirections because of this. It was removed, probably be cause redirections are not a bad way to mitigate the risk (especially against passive eavesdroppers), but don't solve the fundamental problem.
There are various techniques you can use to guide the user to the HTTPS site, and it's not a bad idea to use them (although it won't protect them against active MITM attackers).
Firstly, if you don't have anything that should be served in plain HTTP at all on the webserver, turn off port 80 (e.g. remove Listen 80 in Apache Httpd's configuration). The users will have to use https:// at all times, which may be inconvenient.
Secondly, in your Apache Httpd configuration section for a particular path (either Location or Directory), use the SSLRequireSSL directive: it will require usage of SSL/TLS (even if you've configured it on an alternative port in fact). Other web servers probably have similar directives.
Thirdly, you can use an redirection, either using mod_rewrite or within your code (if it's an application). Something like this should do, for a specific location (see the HTTPS special variable; you can use 302 too, but 301 is better if this is to be more permanent):
RewriteEngine On
RewriteCond %{HTTPS} !=on
RewriteRule ^(samples/.*)$ https://example.com/$1 [R=301,L]
More importantly, make sure that all the links to that secure section use https://. Never rely on the automatic redirection to do the job for you. For this reason, I'd recommend not to use it at all during the development phase.
However, I have noticed that I can still access the website non-securely, ie. by using
httpinstead ofhttps.
This also sounds like you're using the same configuration for both http and https. If you're using Apache Httpd, I would suggest splitting the configuration into two distinct VirtualHosts: one for port 80 and one for port 443. They don't have to have exactly the same configuration: just don't put what's only for HTTPS in the HTTP virtual host at all.
A way to mitigate the problems mentioned above is to use HTTP Strict Transport Security, for browsers that support it (it applies to the entire host as far as I know). The very first connection may still be exposed if https:// isn't used without the redirection, but it's possible to have a pre-loaded list of sites expecting https:// anyway (and enabled for HSTS).
Solution 2
All you need to is redirect http traffic to https - see this article 'Redirect http to https Apache secure connection – force HTTPS Connections'.
For a sub-directory place this in a htaccess file in the directory itself.
RewriteEngine on
RewriteCondition %{SERVER_PORT} !^443$
RewriteRule ^(.*)$ https://www.maindomain.com/directory/$1 [R=301,L]
Related videos on Youtube
Yoh0xFF
Updated on September 18, 2022Comments
-
 Yoh0xFF over 1 year
Yoh0xFF over 1 yearI have a website that has an SSL certificate installed, so that if I access the website using
httpsinstead ofhttpI will be able to connect using a secure connection.However, I have noticed that I can still access the website non-securely, ie. by using
httpinstead ofhttps.How can I prevent people using the website in a non-secure manner?
If I have a directory on the website, eg.
samples/, can I prevent non-secure connections to just this directory? -
 Yoh0xFF about 12 yearsCan you make this happen only for certain sub-directories?
Yoh0xFF about 12 yearsCan you make this happen only for certain sub-directories? -
toomanyairmiles about 12 years@CraigJ sorry, missed the sub-directory part, answer updated.
-
Bruno about 12 yearsWhile this is reduces the risks slightly, this doesn't work against active MITM attackers.
-
toomanyairmiles about 12 yearsGood information, how does gmail do this? - from the look of things they force https.
-
Bruno about 12 yearsThey use a redirection. This works fine, provided that you, as the user expects it to be
https://mail.google.com. If, as a user, you see it work withhttp://mail.google.com, there probably is a MITM proxying the requests to the genuinehttps://mail.google.com. Unfortunately, Gmail can't do much about that if the users themselves don't check. Same principle as in real life: if Alice wants to talk to Bob, but talks to Chuck (who claims to be Bob) instead w/o verifying the ID, Bob won't know about this conversation and won't be able to do anything about it. It's Alice's responsibility. -
 Anonymous Penguin about 10 yearsI've seen some PHP scripts around that it will verify if connected with HTTPS and redirect if not using SSL to a HTTPS address. This is, of course, no easy task unless you are building your site now.
Anonymous Penguin about 10 yearsI've seen some PHP scripts around that it will verify if connected with HTTPS and redirect if not using SSL to a HTTPS address. This is, of course, no easy task unless you are building your site now. -
Bruno about 10 years@AnnonomusPerson, that's exactly the same principle and that's what the rewrite rule from HTTP to HTTPS does. Whether you do it programmatically or by configuration doesn't matter, it's still a redirection with an initial request in plain HTTP, which presents the same problem.