How to properly setup squid3 as HTTPS proxy?
Solution 1
May be you need to consider usinghttp_port directive with ssl-bump and not https_port, since you have your browsers configured with proxy (CONNECT method).
Intercept mode is appropriate for transparent proxy (no browser settings needed), when packets are automatically forwarded to the proxy using iptables. https_port directive is used to intercept and handle such traffic arriving at proxy.
ssl-bump: http://www.squid-cache.org/Doc/config/ssl_bump/
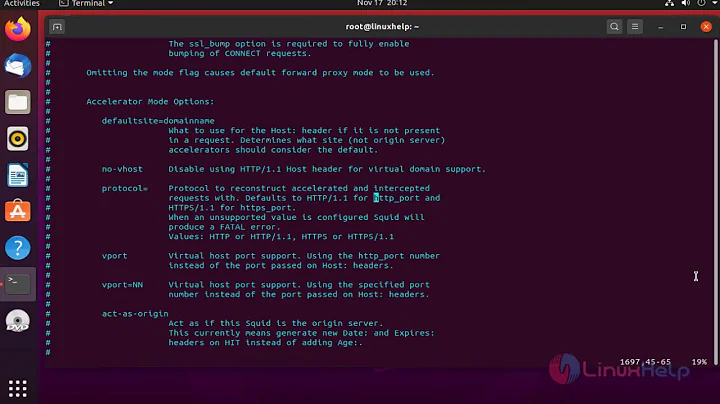
This option is consulted when a CONNECT request is received on an
http_port(or a new connection is intercepted at anhttps_port), provided that port was configured with an ssl-bump flag. The subsequent data on the connection is either treated as HTTPS and decrypted OR tunneled at TCP level without decryption, depending on the first matching bumping "action".
For ssl-bump example: http://wiki.squid-cache.org/ConfigExamples/Intercept/SslBumpExplicit
Solution 2
The error "NF getsockopt(SO_ORIGINAL_DST)" is a NAT error. It has nothing to do with the encryption.
Since you have configured your browser to use the proxy explicitly:
you are not intercepting anything. Using the "intercept" option is wrong and leads to the NAT error.
the browser would not be using TLS to connect to the proxy. That is the real reason why https_port is wrong to use.
the browser will be sending CONNECT messages to port 3127 of the proxy. These are what need to be "bumped".
So what you need to do to is simply to move the ssl-bump settings to your existing http_port line. It should become like this:
http_port 3127 ssl-bump \ generate-host-certificates=on \ dynamic_cert_mem_cache_size=4MB \ key=/etc/squid3/example.com.private \ cert=/etc/squid3/example.com.cert
Other things you should do to correctly setup SSL-Bump is remove the following lines:
sslproxy_flags DONT_VERIFY_PEER sslproxy_cert_error deny all always_direct allow all
They do more harm than good and are not even useful for debugging.
Also, upgrade your proxy to the latest upstream release. TLS and SSL-Bump are involved in a fast changing arms race to do better security, and to decrypt that better security. Using older versions than latest is guaranteed to hit problems one way or another. Squid-3.3 specifically has issues with Elliptic Curve and other recent ciphers, breaks when TLS session resume is used, cannot bypass cert pinning using SNI, generates SHA-1 certificates, etc.
Related videos on Youtube
jobin
Updated on September 18, 2022Comments
-
jobin over 1 year
I am trying to setup squid3 as an HTTPS proxy using the tutorial given here. I have properly setup the proxy settings in my browser and when I try to hit HTTP web sites, I am able to connect successfully. However, I keep getting a "Connection timed out error" whenever I hit an HTTPS protocol web site and the following error in my
/var/log/squid3/cache.log:2016/06/20 19:12:47| NF getsockopt(SO_ORIGINAL_DST) failed on local=<local_ip_address>:3129 remote=<remote_ip_address>:55209 FD 8 flags=33: (92) Protocol not availableHere is my
/etc/squid3/squid.conffile (commented lines removed for brevity):auth_param basic program /usr/lib/squid3/basic_ncsa_auth /usr/etc/passwd auth_param basic casesensitive off auth_param basic credentialsttl 2 hours acl user_auth proxy_auth REQUIRED http_access allow user_auth acl SSL_ports port 443 acl Safe_ports port 80 # http acl Safe_ports port 21 # ftp acl Safe_ports port 443 # https acl Safe_ports port 70 # gopher acl Safe_ports port 210 # wais acl Safe_ports port 1025-65535 # unregistered ports acl Safe_ports port 280 # http-mgmt acl Safe_ports port 488 # gss-http acl Safe_ports port 591 # filemaker acl Safe_ports port 777 # multiling http acl CONNECT method CONNECT http_access allow localhost http_access allow all http_port 3127 https_port 3129 intercept ssl-bump generate-host-certificates=on dynamic_cert_mem_cache_size=4MB key=/etc/squid3/example.com.private cert=/etc/squid3/example.com.cert ssl_bump server-first all sslproxy_flags DONT_VERIFY_PEER sslproxy_cert_error deny all sslcrtd_program /usr/lib/squid3/ssl_crtd -s /var/lib/ssl_db -M 4MB sslcrtd_children 8 startup=1 idle=1 coredump_dir /var/spool/squid3 refresh_pattern ^ftp: 1440 20% 10080 refresh_pattern ^gopher: 1440 0% 1440 refresh_pattern -i (/cgi-bin/|\?) 0 0% 0 refresh_pattern (Release|Packages(.gz)*)$ 0 20% 2880 refresh_pattern . 0 20% 4320 always_direct allow allHere is the output of my
squid3 -v:Squid Cache: Version 3.3.8 (Ubuntu) configure options: '--build=i686-linux-gnu' '--prefix=/usr' '--includedir=${prefix}/include' '--mandir=${prefix}/share/man' '--infodir=${prefix}/share/info' '--sysconfdir=/etc' '--localstatedir=/var' '--libexecdir=${prefix}/lib/squid3' '--srcdir=.' '--disable-maintainer-mode' '--disable-dependency-tracking' '--disable-silent-rules' '--datadir=/usr/share/squid3' '--sysconfdir=/etc/squid3' '--mandir=/usr/share/man' '--enable-inline' '--enable-async-io=8' '--enable-ssl' '--enable-ssl-crtd' '--enable-storeio=ufs,aufs,diskd,rock' '--enable-removal-policies=lru,heap' '--enable-delay-pools' '--enable-cache-digests' '--enable-underscores' '--enable-icap-client' '--enable-follow-x-forwarded-for' '--enable-auth-basic=DB,fake,getpwnam,LDAP,MSNT,MSNT-multi-domain,NCSA,NIS,PAM,POP3,RADIUS,SASL,SMB' '--enable-auth-digest=file,LDAP' '--enable-auth-negotiate=kerberos,wrapper' '--enable-auth-ntlm=fake,smb_lm' '--enable-external-acl-helpers=file_userip,kerberos_ldap_group,LDAP_group,session,SQL_session,unix_group,wbinfo_group' '--enable-url-rewrite-helpers=fake' '--enable-eui' '--enable-esi' '--enable-icmp' '--enable-zph-qos' '--enable-ecap' '--disable-translation' '--with-swapdir=/var/spool/squid3' '--with-logdir=/var/log/squid3' '--with-pidfile=/var/run/squid3.pid' '--with-filedescriptors=65536' '--with-large-files' '--with-default-user=proxy' '--enable-linux-netfilter' 'build_alias=i686-linux-gnu' 'CFLAGS=-g -O2 -fPIE -fstack-protector --param=ssp-buffer-size=4 -Wformat -Werror=format-security -Wall' 'LDFLAGS=-Wl,-Bsymbolic-functions -fPIE -pie -Wl,-z,relro -Wl,-z,now' 'CPPFLAGS=-D_FORTIFY_SOURCE=2' 'CXXFLAGS=-g -O2 -fPIE -fstack-protector --param=ssp-buffer-size=4 -Wformat -Werror=format-security'I have spent a lot of time googling this error but could not arrive at a solution which would configure squid as an HTTP proxy. How do I get this working?
-
jobin almost 8 yearsI tried this but ran into the same exception as before (on browser as well as in the
/var/log/squid3/cache.logfile). You may be right, but for some reason, many of the tutorials on the web are usinghttps_portforssl-bump! -
Diamond almost 8 yearsCan you check the syslog while restarting squid? You will surely get a hint if there is any error. You can also try:
squid3 -k parse. Well, surely you cant declare http_port twice. So, with the https_port may be you can restart squid and check syslog. Also see if the port you have assignend for https_port is available withnetstatcommand. -
Diamond almost 8 yearsYou can also try with only one
http_portdeclaration with ssl-bump and see if it works, if you have not tried already. Both http and https should work. -
jobin almost 8 yearsI am now using only
http_port 3129 intercept ssl-bump generate-host-certificates=on dynamic_cert_mem_cache_size=4MB key=/etc/squid3/example.com.private cert=/etc/squid3/example.com.certand restarted squid3 but don't see any exception coming up in/var/log/syslog. I have pasted the output ofsquid3 -k parsehere: pastebin.com/j16MSMjf -
Diamond almost 8 yearsYou are also using intercept mode, which means it is a transparent proxy so take note of that. Also make sure your proxy server can connect to the world on port 443.
-
jobin almost 8 yearsYes, the server can connect to internet using port 443 (I tried
telnet google.com 443and it connects). Also,I tried removinginterceptand restarted squid3 and see that my browser is now asking for the username & password (which was not the case before) but then failed withSecure Connection Failed. The connection to the server was reset while the page was loading. The page you are trying to view cannot be shown because the authenticity of the received data could not be verified. Please contact the website owners to inform them of this problem. -
Amos Jeffries over 7 yearsthis answer is wrong. ssl-bump is available on https_port and when intercepting port 443 that is the correct directive to receive the traffic with.
-
Diamond over 7 years@AmosJeffries, you are correct, I have updated my answer.