How to query EFI signature
Solution 1
It depends on what kind of signature you're talking about. If you have an EFI system, you can have signed EFI executables (*.efi) and force your EFI firmware to only execute those with a known signature. This is known as Secure Boot. To check an EFI binary for a signature you can use the tool sbverify:
$ sbverify --no-verify signed-binary.efi
Signature verification OK
$ sbverify --no-verify unsigned-binary.efi
No signature table present
Unable to read signature data from unsigned-binary.efi
Signature verification failed
Unfortunately I didn't see an easy way of extracting and displaying the EFI signature. :(
What's more likely what you are looking for is GRUB's own ability to check its modules and kernels to be booted for valid signatures (Secure Boot just affects the GRUB binary itself, everything GRUB loads does not necessarily need to be EFI-signed). Those are (as far as I understand) plain old detached GPG signatures (so for example for a kernel called vmlinuz-1.2.3 you'd have a file vmlinuz-1.2.3.sig with the signature). Those can simply be displayed and verified with
$ gpg --verify vmlinuz-1.2.3.sig vmlinuz-1.2.3
gpg: Signature made Tue Apr 1 12:34:56 2014 CEST using RSA key ID d3adb33f
gpg: Good signature from "John Doe <[email protected]>"
If you don't have a *.sig file to your kernel, it is obviously not signed.
You can disable signature checking in GRUB by entering set check_signature=no at the GRUB command prompt. You can get more information on that topic here (this functionality is rather new and the official GRUB website only has the manual for version 2.00 online, which lacks this feature). This also explains how to sign your modules and kernel with your own key and to tell GRUB about it.
Solution 2
You can use sbverify , for instance:
# sbverify --list /efi/EFI/refind/shimx64.efi.signed
warning: data remaining[1159744 vs 1322936]: gaps between PE/COFF sections?
signature 1
image signature issuers:
- /C=US/ST=Washington/L=Redmond/O=Microsoft Corporation/CN=Microsoft Corporation UEFI CA 2011
image signature certificates:
- subject: /C=US/ST=Washington/L=Redmond/O=Microsoft Corporation/CN=Microsoft Windows UEFI Driver Publisher
issuer: /C=US/ST=Washington/L=Redmond/O=Microsoft Corporation/CN=Microsoft Corporation UEFI CA 2011
- subject: /C=US/ST=Washington/L=Redmond/O=Microsoft Corporation/CN=Microsoft Corporation UEFI CA 2011
issuer: /C=US/ST=Washington/L=Redmond/O=Microsoft Corporation/CN=Microsoft Corporation Third Party Marketplace Root
or:
# sbverify --list /boot/vmlinuz-5.7.11-amd64
signature 1
image signature issuers:
- /CN=morfikov's kernel-signing key
image signature certificates:
- subject: /CN=morfikov's kernel-signing key
issuer: /CN=morfikov's kernel-signing key
Solution 3
Using the information provided by Andreas, I was able to figure out the following:
On the working system, both Grub-EFI itself and the Linux kernel are signed with the same key. On the non-working system, neither Grub nor the Linux kernel are signed. When I try to copy the Linux kernel from one system to the other, Grub complains that the kernel is not signed. There is no detatched GPG signature; it appears Grub is looking for the same thing that Secure Boot is looking for - an internal PE signature.
Now, if I can just figure out how to get OpenSUSE to sign their 32-bit version of the Linux kernel...
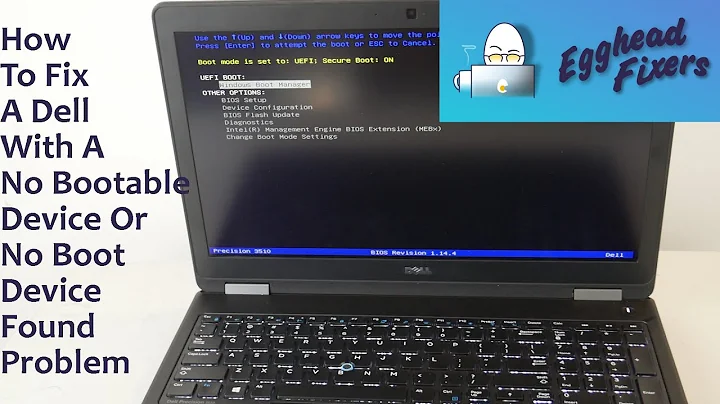
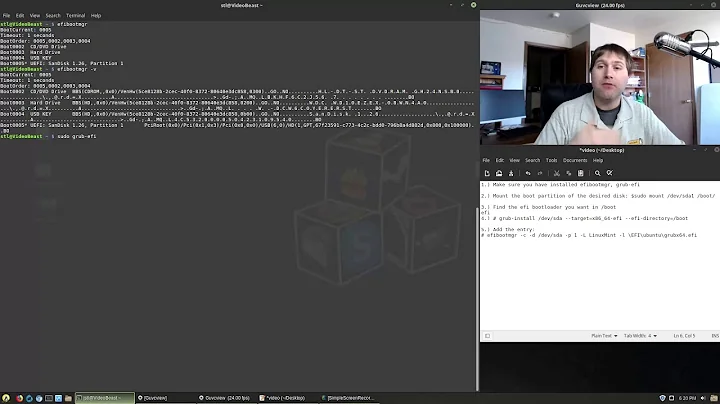
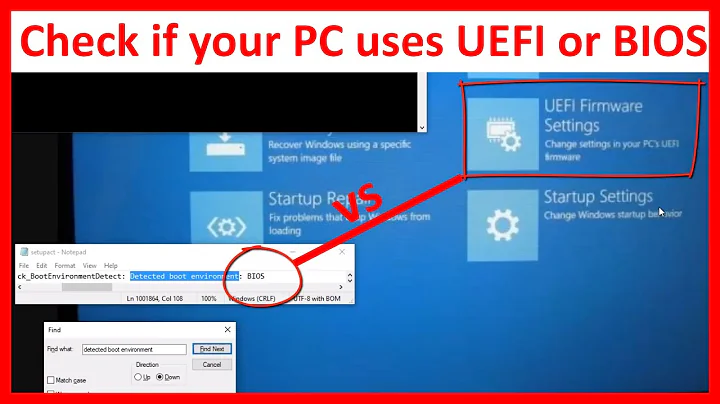
Related videos on Youtube
MathematicalOrchid
Updated on September 18, 2022Comments
-
 MathematicalOrchid 11 months
MathematicalOrchid 11 monthsIt appears that Grub-EFI will only boot a "signed" Linux kernel. Is there some command that will allow me to query a given kernel image to find out what signatures (if any) are present on it?
-
 MathematicalOrchid over 9 yearsAny idea which package contains
MathematicalOrchid over 9 yearsAny idea which package containssbverify? (OpenSUSE, in case it matters.) -
 Andreas Wiese over 9 yearsHave a look here.
Andreas Wiese over 9 yearsHave a look here. -
 MathematicalOrchid over 9 yearsThe
MathematicalOrchid over 9 yearsThesbsigntoolspackage is only available from nonstandard repos, but I was able to install thepesignpackage. It refused to do anything until I created an NSS database (even though I'm not going to use it), but I was then able to verify signatures - which is what the question asked.