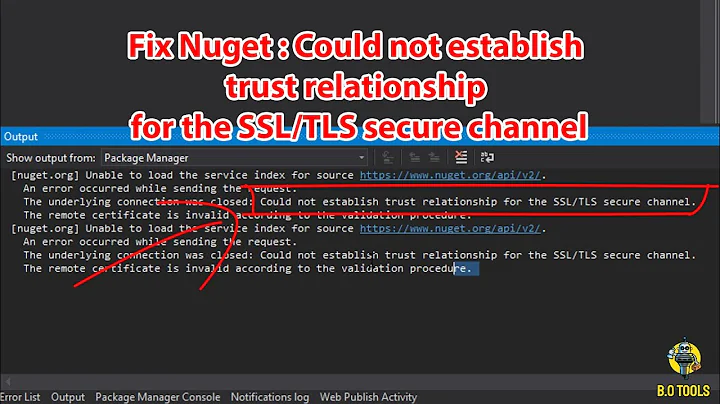
How to solve "Could not establish trust relationship for the SSL/TLS secure channel with authority"
Solution 1
As a workaround you could add a handler to the ServicePointManager's ServerCertificateValidationCallback on the client side:
System.Net.ServicePointManager.ServerCertificateValidationCallback +=
(se, cert, chain, sslerror) =>
{
return true;
};
but be aware that this is not a good practice as it completely ignores the server certificate and tells the service point manager that whatever certificate is fine which can seriously compromise client security. You could refine this and do some custom checking (for certificate name, hash etc). at least you can circumvent problems during development when using test certificates.
Solution 2
When I have this problem it is because the client.config had its endpoints like:
https://myserver/myservice.svc
but the certificate was expecting
https://myserver.mydomain.com/myservice.svc
Changing the endpoints to match the FQDN of the server resolves my problem. I know this is not the only cause of this problem.
Solution 3
Your problem arises because you're using a self signed key. The client does not trust this key, nor does the key itself provide a chain to validate or a certificate revocation list.
You have a few options - you can
turn off certificate validation on the client (bad move, man in the middle attacks abound)
use makecert to create a root CA and create certificates from that (ok move, but there is still no CRL)
create an internal root CA using Windows Certificate Server or other PKI solution then trust that root cert (a bit of a pain to manage)
purchase an SSL certificate from one of the trusted CAs (expensive)
Solution 4
the first two use lambda, the third uses regular code... hope you find it helpful
//Trust all certificates
System.Net.ServicePointManager.ServerCertificateValidationCallback =
((sender, certificate, chain, sslPolicyErrors) => true);
// trust sender
System.Net.ServicePointManager.ServerCertificateValidationCallback
= ((sender, cert, chain, errors) => cert.Subject.Contains("YourServerName"));
// validate cert by calling a function
ServicePointManager.ServerCertificateValidationCallback += new RemoteCertificateValidationCallback(ValidateRemoteCertificate);
// callback used to validate the certificate in an SSL conversation
private static bool ValidateRemoteCertificate(object sender, X509Certificate cert, X509Chain chain, SslPolicyErrors policyErrors)
{
bool result = false;
if (cert.Subject.ToUpper().Contains("YourServerName"))
{
result = true;
}
return result;
}
Solution 5
A one line solution. Add this anywhere before calling the server on the client side:
System.Net.ServicePointManager.ServerCertificateValidationCallback += delegate { return true; };
This should only be used for testing purposes because the client will skip SSL/TLS security checks.
Related videos on Youtube
Comments
-
JL. almost 2 years
I have a WCF service hosted in IIS 7 using HTTPS. When I browse to this site in Internet Explorer, it works like a charm, this is because I have added the certificate to the local root certificate authority store.
I'm developing on 1 machine, so client and server are same machine. The certificate is self-signed directly from IIS 7 management snap in.
I continually get this error now...
Could not establish trust relationship for the SSL/TLS secure channel with authority.
... when called from client console.
I manually gave myself permissions and network service to the certificate, using
findprivatekeyand usingcacls.exe.I tried to connect to the service using SOAPUI, and that works, so it must be an issue in my client application, which is code based on what used to work with http.
Where else can I look I seem to have exhausted all possibilities as to why I can't connect?
-
 jww almost 10 yearspossible duplicate of Could not establish trust relationship for SSL/TLS secure channel -- SOAP
jww almost 10 yearspossible duplicate of Could not establish trust relationship for SSL/TLS secure channel -- SOAP -
 granadaCoder over 7 yearsIf you have control of the creation of the certificates, don't forget about "Alternate Subject Name". Like you could put a wild card in "*.full.domainname.com". See digicert.com/subject-alternative-name.htm
granadaCoder over 7 yearsIf you have control of the creation of the certificates, don't forget about "Alternate Subject Name". Like you could put a wild card in "*.full.domainname.com". See digicert.com/subject-alternative-name.htm
-
-
Luke Puplett almost 14 yearsI think most public setups will use a purchased cert but during dev use the above code within conditional #if statements. Enterprise devs should generally setup an internal CA server >> technet.microsoft.com/en-us/library/cc875810.aspx
-
Roger Willcocks about 13 yearsHelped me figure out how to get my SSL WCF call working with Fiddler2 for debugging.
-
 Mike Cheel over 11 yearsI just had this issue again and this time it had to with the wrong certificate being used. It seems like in both cases it has to do with matching up names properly.
Mike Cheel over 11 yearsI just had this issue again and this time it had to with the wrong certificate being used. It seems like in both cases it has to do with matching up names properly. -
VoodooChild about 11 years//Trust all certificates System.Net.ServicePointManager.ServerCertificateValidationCallback += (se, cert, chain, sslerror) => { return true; }; // trust sender System.Net.ServicePointManager.ServerCertificateValidationCallback += (se, cert, chain, sslerror) => { return cert.Subject.Contains("ca-l-9wfvrm1.ceridian.ca"); };
-
moodboom about 11 yearsRegarding (4), StartSSL will actually give you a free Class 1 certificate that works in all major browsers. They work great for me for my half a dozen low bandwidth sites.
-
 knightscharge almost 11 yearsMy auto generated configuration had <endpoint address="localhost/myservice.svc" changing this to <endpoint address="mymachine.mydoman.com/myservice.svc" resolved this.
knightscharge almost 11 yearsMy auto generated configuration had <endpoint address="localhost/myservice.svc" changing this to <endpoint address="mymachine.mydoman.com/myservice.svc" resolved this. -
Rich C almost 10 years@karank Consider putting it in the Application_Start method in the Global.asax (see stackoverflow.com/a/12507094/1175419). I would strongly recommend using a #if DEBUG compiler directive or something similar as mentioned in Luke's comment.
-
daveD over 9 yearsThis answer isn't very good, as it does not explain the risks associated with the code.
-
 Dhanuka777 about 8 yearsAwesome! you can use lambda expression as System.Net.ServicePointManager.ServerCertificateValidationCallback += (se, cert, chain, sslerror) => true;
Dhanuka777 about 8 yearsAwesome! you can use lambda expression as System.Net.ServicePointManager.ServerCertificateValidationCallback += (se, cert, chain, sslerror) => true; -
 granadaCoder over 7 yearsA little extra explanation can be found here : blog.effectivemessaging.com/2015_09_01_archive.html
granadaCoder over 7 yearsA little extra explanation can be found here : blog.effectivemessaging.com/2015_09_01_archive.html -
 granadaCoder over 7 yearsI think #2 on this list...this url might help : blogs.technet.microsoft.com/jhoward/2005/02/02/… "How-to use MakeCert for trusted root certification authority and SSL certificate issuance"
granadaCoder over 7 yearsI think #2 on this list...this url might help : blogs.technet.microsoft.com/jhoward/2005/02/02/… "How-to use MakeCert for trusted root certification authority and SSL certificate issuance" -
aruno about 7 yearsNote: StartCom is no longer trustworthy - and has just been removed from Chrome en.wikipedia.org/wiki/StartCom
-
markaaronky over 6 yearsA brilliant workaround for testing. We are consuming a service whose provider has made security a living hell with a convoluted chain of security certificates and until we can get their wonky certs and chaining to work properly, this workaround is the only thing allowing us to continue development.
-
Vipin Dubey over 6 yearsGreat, thanks for this answer ! Solved the issues without making any code changes.
-
 Bjartur Thorlacius over 6 yearsAny cracker could forge a certificate passing all the above tests. This is unsecure.
Bjartur Thorlacius over 6 yearsAny cracker could forge a certificate passing all the above tests. This is unsecure. -
Sergey about 6 yearsin my case accepted answer didn't help me, but this one did a trick
-
Tolga almost 6 yearsThis is the only answer which corrected the error in my case.
-
Alexander over 5 yearsThanks, it works. But it has nothing to do with .net core. It's an universal recipe :)
-
 tom redfern over 5 yearsOP: be aware this is not good practise. Developers of the world: we don't care gives me teh codez!11...
tom redfern over 5 yearsOP: be aware this is not good practise. Developers of the world: we don't care gives me teh codez!11... -
 AussieJoe about 4 yearsThis was absolutely my issue and it took me two days to find your answer. +1, I would give you +1000 if I could.
AussieJoe about 4 yearsThis was absolutely my issue and it took me two days to find your answer. +1, I would give you +1000 if I could. -
Swinkaran about 4 yearsThis is a good workaround (or you call Bypass) for the time being. But yeah really need to get the certificate.
-
Marco Barbero almost 4 yearsOn Net Core 3.1 I soved the problem with this solution:stackoverflow.com/questions/52908503/…
-
Metalogic over 3 yearsThis didn't work for me initially. I had to make one modification to the steps above: When dragging the certificate, make sure to hold down the Ctrl key so that the certificate is copied, not moved from Personal/Certificates to Trusted Root Certification Authorities/Certificates.
-
 phifi over 3 yearsAlso this was the trick that helped me, although with .Net 4.7.2
phifi over 3 yearsAlso this was the trick that helped me, although with .Net 4.7.2



![[SOLVED] Could not establish trust relationship for the SSL/TLS secure channel | Driver Easy](https://i.ytimg.com/vi/O8t_DIDDYAs/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLCoY9m-Jdti3u2oPxjX5ACx1GIkDQ)
