Install Mod_Security for Nginx without need to recompile
You can do it by adding ModSecurity as dynamic module or using Dockerized and hardened Nginx container.
Use ModSecurity with Docker
Run HTTP server with default settings
docker run -p 80:80 -v /path/to/web/files:/www bunkerity/bunkerized-nginx
Run HTTPS server with automated Let's Encrypt
docker run -p 80:80 -p 443:443 -v /path/to/web/files:/www -v /where/to/save/certificates:/etc/letsencrypt -e SERVER_NAME=www.yourdomain.com -e AUTO_LETS_ENCRYPT=yes -e REDIRECT_HTTP_TO_HTTPS=yes bunkerity/bunkerized-nginx
Certificates are stored in the /etc/letsencrypt directory, you should save it on your local drive.
If you don't want your webserver to listen on HTTP add the environment variable LISTEN_HTTP with a "no" value. But Let's Encrypt needs the port 80 to be opened so redirecting the port is mandatory.
Here you have three environment variables :
-
SERVER_NAME: define the FQDN of your webserver, this is mandatory for Let's Encrypt (www.yourdomain.com should point to your IP address) -
AUTO_LETS_ENCRYPT: enable automatic Let's Encrypt creation and renewal of certificates -
REDIRECT_HTTP_TO_HTTPS: enable HTTP to HTTPS redirection
Docker Hub : bunkerized-nginx
Requirement:NGINX 1.11.5 and later.
Step 1 : Installing needed packages
apt-get install -y apt-utils autoconf automake build-essential git libcurl4-openssl-dev libgeoip-dev liblmdb-dev libpcre++-dev libtool libxml2-dev libyajl-dev pkgconf wget zlib1g-dev
##Step 2 : Download and Compile the ModSecurity 3 Source Code##
git clone --depth 1 -b v3/master --single-branch https://github.com/SpiderLabs/ModSecurity
cd ModSecurity
git submodule init
git submodule update
./build.sh
./configure
make
make install
Note: The compilation takes about 15 minutes, depending on the processing power of your system. #Step 3 : Download the NGINX Connector for ModSecurity and Compile It as a Dynamic Module#
git clone --depth 1 https://github.com/SpiderLabs/ModSecurity-nginx.git
wget http://nginx.org/download/nginx-1.13.7.tar.gz
tar zxvf nginx-1.13.7.tar.gz
cd nginx-1.13.7
./configure --with-compat --add-dynamic-module=../ModSecurity-nginx
make modules
cp objs/ngx_http_modsecurity_module.so /etc/nginx/modules
##Step 4 : Load the NGINX ModSecurity Connector Dynamic Module ## Add this line to /etc/nginx/nginx.conf
load_module modules/ngx_http_modsecurity_module.so;
##Step 5 : Configure and Enable## Set up the appropriate ModSecurity configuration file. Here we’re using the recommended ModSecurity configuration provided by TrustWave Spiderlabs, the corporate sponsors of ModSecurity.
mkdir /etc/nginx/modsec
wget -P /etc/nginx/modsec/ https://raw.githubusercontent.com/SpiderLabs/ModSecurity/v3/master/modsecurity.conf-recommended
wget -P /etc/nginx/modsec/ https://raw.githubusercontent.com/SpiderLabs/ModSecurity/v3/master/unicode.mapping
mv /etc/nginx/modsec/modsecurity.conf-recommended /etc/nginx/modsec/modsecurity.conf
Change the SecRuleEngine directive in the configuration to change from the default “detection only” mode to actively dropping malicious traffic.
sed -i 's/SecRuleEngine DetectionOnly/SecRuleEngine On/' /etc/nginx/modsec/modsecurity.conf
Configure one or more rules. For the purposes of this blog we’re creating a single simple rule that drops a request in which the URL argument called testparam includes the string test in its value. Put the following text in /etc/nginx/modsec/main.conf
# From https://github.com/SpiderLabs/ModSecurity/blob/master/\
# modsecurity.conf-recommended
#
# Edit to set SecRuleEngine On
Include "/etc/nginx/modsec/modsecurity.conf"
# Basic test rule
SecRule ARGS:testparam "@contains test" "id:1234,deny,status:403"
Add the modsecurity and modsecurity_rules_file directives to the NGINX configuration to enable ModSecurity:
server {
# ...
modsecurity on;
modsecurity_rules_file /etc/nginx/modsec/main.conf;
}
source : nginx.com
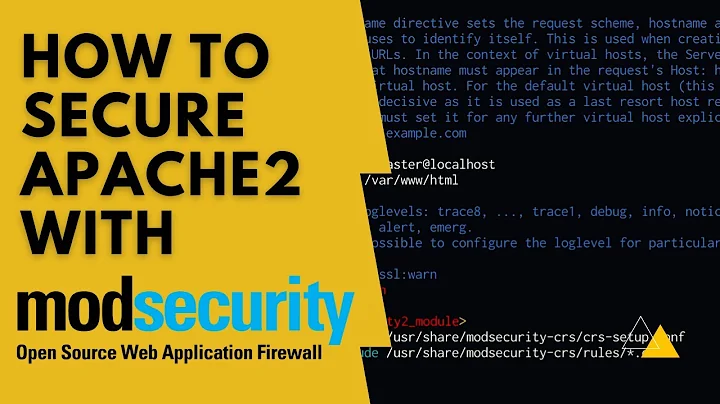
Related videos on Youtube
julio
* There are 10 types of people in the world: those who understand binary, and those who don’t. *
Updated on September 18, 2022Comments
-
julio almost 2 years
I've got LEMP all setup. Now I would like to add mod_security.
I tried to research but all I could find are instructions on how to recompile nginx. Is there a way to add mod_security without needing to recompile?
I'm currently running nginx/1.9.15 installed with PPA because I was after HTTP/2. I don't have experience in compiling nginx and I don't know if ever I recompile I would break nginx since I got it from PPA.
Hope you can help.
Thank you.
-
 Michael Hampton about 8 yearsSince 1.10 nginx can now load modules dynamically, so in principle it's no longer necessary to compile them with nginx. Contact the mod_security developers and ask them when they will take advantage of this.
Michael Hampton about 8 yearsSince 1.10 nginx can now load modules dynamically, so in principle it's no longer necessary to compile them with nginx. Contact the mod_security developers and ask them when they will take advantage of this.
-
-
Dan Bolser over 5 yearsIs there a PPA for this (xenial)?
-
 Jenny D about 5 yearsI strongly suggest adding some error checking to your script. For instance, on line 12, you're assuming that the
Jenny D about 5 yearsI strongly suggest adding some error checking to your script. For instance, on line 12, you're assuming that thecd $OPT_DIRwill work - if it doesn't, thegit cloneon line 16 is going to clone stuff into whatever directory you started in. Don't just assume that commands will succed. -
 Chetan Patil about 5 yearsok. Thank you for suggestion, will definitely add those checks.
Chetan Patil about 5 yearsok. Thank you for suggestion, will definitely add those checks. -
 womble about 5 years"Without need to recompile" is in the question title.
womble about 5 years"Without need to recompile" is in the question title. -
 Jenny D about 5 yearsApart from that, it's a nice script... but I've been bitten badly a couple of times by writing and running scripts without error checking - I'm hoping to let others learn from my mistakes, nobody has time to do all mistakes on their own :-)
Jenny D about 5 yearsApart from that, it's a nice script... but I've been bitten badly a couple of times by writing and running scripts without error checking - I'm hoping to let others learn from my mistakes, nobody has time to do all mistakes on their own :-) -
 Swarup Golui about 5 yearsChetan Patil serverfault.com/users/520010/chetan-patil Fix The Line 62 ./configure --with-compatadd-dynamic-module=/opt/ModSecurity-nginx With ./configure --with-compat --add-dynamic-module=/opt/ModSecurity-nginx
Swarup Golui about 5 yearsChetan Patil serverfault.com/users/520010/chetan-patil Fix The Line 62 ./configure --with-compatadd-dynamic-module=/opt/ModSecurity-nginx With ./configure --with-compat --add-dynamic-module=/opt/ModSecurity-nginx -
 Chetan Patil about 5 years@SwarupGolui fixed it.
Chetan Patil about 5 years@SwarupGolui fixed it. -
Vahid Nameni over 4 yearsYes there is (available on another answer) but it's better use latest Ubuntu LTS version.