Is anyone using access.conf and netgroup authentication with sssd?
Solution 1
I have Red Hat 6 authenticating against AD using Netgroups successfully. I am trying to get it authenticating against an old Sun LDAP server and am not having luck. I can see the netgroups, I can see the user with "getent netgroup {name of netgroup} and I can su to the user. However when I attempt to login it does not work.
What I can tell you from my AD authentication is taht your netgroup statement is the opposite of what you want. When you begin with a - it means DO NOT allow them to login. Try switching that to a + meaning DO allow the users in this netgroup to login.
Also use the getent command to check to see if you can see your users and netgroup proprely. getent passwd {username} getent netgroup {name of netgroup}
Remember getent also looks at your local files (as defined in nsswitch.conf) for this information so be sure the information is only available via LDAP.
Hope this helps,
Dan
Solution 2
Not an expert on pam but if you're using access.conf you need a reference to pam_access.so. perhaps: account required pam_access.so
Just keep a root shell open while you test. I've managed to lock out the root user with a bad pam edit.
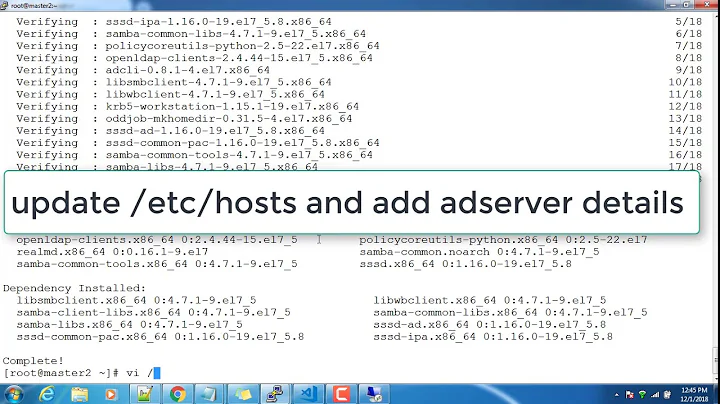
Related videos on Youtube
mr.zog
Updated on September 18, 2022Comments
-
 mr.zog almost 2 years
mr.zog almost 2 yearsI want to be able to authenticate users (via ssh) to specific groups of hosts based on the users' LDAP netgroup membership. The LDAP server is dsee7. The distro is OEL 6.5 with openldap as the client.
The only account we don't want to authenticate using LDAP is root.
sssd.conf looks like this:
[sssd] config_file_version = 2 services = nss,pam,autofs domains = default [nss] filter_groups = root filter_users = root reconnection_retries = 3 entry_cache_timeout = 300 entry_cache_nowait_percentage = 75 [pam] [domain/default] auth_provider = ldap ldap_id_use_start_tls = True chpass_provider = ldap cache_credentials = True ldap_search_base = dc=e-durp,dc=com id_provider = ldap ldap_uri = ldaps://lvl1.lvs01.edurp.com/ ldaps://lvl1.lvs01.edurp.com/ ldap_tls_cacertdir = /etc/openldap/cacertsThe /etc/openldap/ldap.conf looks like this:
URI ldaps://ldap.edurp.com/ ldaps://ldap1.edurp.com ldaps://ldap2.edurp.com BASE dc=edurp,dc=com TLS_CACERTDIR /etc/openldap/cacerts TLS_CACERT /etc/openldap/cacerts/ldap_ca.cert TLS_REQCERT nevernsswitch.conf looks like this:
passwd: files compat shadow: files compat passwd_compat: sss shadow_compat: sss group: files sss hosts: files dns bootparams: nisplus [NOTFOUND=return] files ethers: files netmasks: files networks: files protocols: files rpc: files services: files sss netgroup: sss files publickey: nisplus automount: files ldap aliases: files nisplusAnd /etc/pam.d/system-auth reads:
auth required pam_env.so auth sufficient pam_fprintd.so auth sufficient pam_unix.so nullok try_first_pass auth requisite pam_succeed_if.so uid >= 500 quiet auth sufficient pam_sss.so use_first_pass auth required pam_deny.so account required pam_unix.so broken_shadow account sufficient pam_localuser.so account sufficient pam_succeed_if.so uid < 500 quiet account [default=bad success=ok user_unknown=ignore] pam_sss.so account required pam_permit.so password requisite pam_cracklib.so try_first_pass retry=3 type= password sufficient pam_unix.so md5 shadow nullok try_first_pass use_authtok password sufficient pam_sss.so use_authtok password required pam_deny.so session optional pam_keyinit.so revoke session required pam_limits.so session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid session required pam_unix.so session optional pam_sss.soSo I tried adding a netgroup to /etc/security/access.conf like so:
#- : ALL : ALL -:@eeederp: ALLand restarted sssd just in case . . .
My user belongs to the netgroup eeederp and is still able to get in using his LDAP password.
Any clues would be appreciated.
-
 mr.zog almost 10 yearsI just realized I could add "debug" to any line in /etc/pam.d/system-auth. Perhaps I'll get some answers there.
mr.zog almost 10 yearsI just realized I could add "debug" to any line in /etc/pam.d/system-auth. Perhaps I'll get some answers there. -
 mr.zog almost 10 years
mr.zog almost 10 years16:24:35 node00 sshd[55306]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=10.65.4.38 user=eeederp16:24:36 node00 sshd[55306]: pam_sss(sshd:auth): authentication success; logname= uid=0 euid=0 tty=ssh ruser= rhost=10.65.4.38 user=eeederp16:24:36 node00 sshd[55306]: pam_access(sshd:account): access denied for usereeederp' from '10.65.4.38'`16:24:36 node00 sshd[55307]: fatal: Access denied for user eeederp by PAM account configuration16:24:36 node00 sshd[55306]: Failed password for eeederp from 10.65.4.38 port 56330 ssh2
-
-
 Scottie H almost 5 yearsYes. pam_access.so needs to be in /etc/pam.d/password-auth-ac an systemauth-ac. I would double check the syntax of your access.conf file. I have Red Hat 7 and it is a different format than what you have shown here. I have - : @eeederp ...
Scottie H almost 5 yearsYes. pam_access.so needs to be in /etc/pam.d/password-auth-ac an systemauth-ac. I would double check the syntax of your access.conf file. I have Red Hat 7 and it is a different format than what you have shown here. I have - : @eeederp ...