Keycloak-gatekeeper: 'aud' claim and 'client_id' do not match
Solution 1
With recent keycloak version 4.6.0 the client id is apparently no longer automatically added to the audience field 'aud' of the access token. Therefore even though the login succeeds the client rejects the user. To fix this you need to configure the audience for your clients (compare doc [2]).
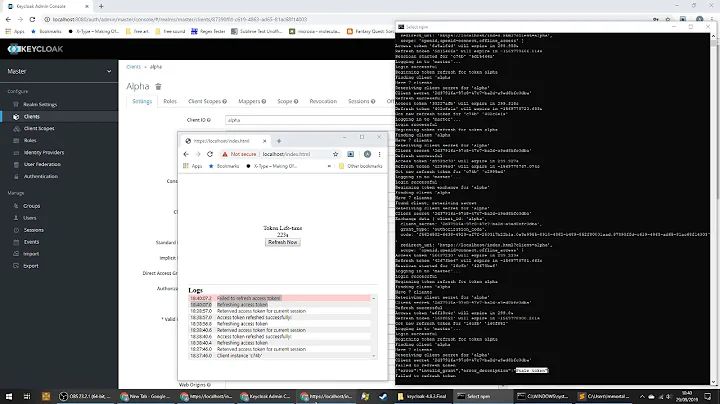
Configure audience in Keycloak
- Add realm or configure existing
- Add client my-app or use existing
- Goto to the newly added "Client Scopes" menu [1]
- Add Client scope 'good-service'
- Within the settings of the 'good-service' goto Mappers tab
- Create Protocol Mapper 'my-app-audience'
- Name: my-app-audience
- Choose Mapper type: Audience
- Included Client Audience: my-app
- Add to access token: on
- Create Protocol Mapper 'my-app-audience'
- Configure client my-app in the "Clients" menu
- Client Scopes tab in my-app settings
- Add available client scopes "good-service" to assigned default client scopes
If you have more than one client repeat the steps for the other clients as well and add the good-service scope. The intention behind this is to isolate client access. The issued access token will only be valid for the intended audience. This is thoroughly described in Keycloak's documentation [1,2].
Links to recent master version of keycloak documentation:
- [1] https://github.com/keycloak/keycloak-documentation/blob/master/server_admin/topics/clients/client-scopes.adoc
- [2] https://github.com/keycloak/keycloak-documentation/blob/master/server_admin/topics/clients/oidc/audience.adoc
Links with git tag:
- [1] https://github.com/keycloak/keycloak-documentation/blob/f490e1fba7445542c2db0b4202647330ddcdae53/server_admin/topics/clients/oidc/audience.adoc
- [2] https://github.com/keycloak/keycloak-documentation/blob/5e340356e76a8ef917ef3bfc2e548915f527d093/server_admin/topics/clients/client-scopes.adoc
Solution 2
This is due to a bug: https://issues.jboss.org/browse/KEYCLOAK-8954
There are two workarounds described in the bug report, both of which appear to do basically the same thing as the accepted answer here but can be applied to the Client Scope role, so you don't have to apply them to every client individually.
Solution 3
If, like me, you want to automate the keycloak config, you can use kcadm
/opt/jboss/keycloak/bin/kcadm.sh \
create clients/d3170ee6-7778-413b-8f41-31479bdb2166/protocol-mappers/models -r your-realm \
-s name=audience-mapping \
-s protocol=openid-connect \
-s protocolMapper=oidc-audience-mapper \
-s config.\"included.client.audience\"="your-audience" \
-s config.\"access.token.claim\"="true" \
-s config.\"id.token.claim\"="false"
Related videos on Youtube
arkadiy kraportov
Updated on April 07, 2020Comments
-
arkadiy kraportov about 4 years
What is the correct way to set the
audclaim to avoid the error below?unable to verify the id token {"error": "oidc: JWT claims invalid: invalid claims, 'aud' claim and 'client_id' do not match, aud=account, client_id=webapp"}I kinda worked around this error message by hardcoding
audclaim to be the same as myclient_id. Is there any better way?Here is my
docker-compose.yml:version: '3' services: keycloak-proxy: image: "keycloak/keycloak-gatekeeper" environment: - PROXY_LISTEN=0.0.0.0:3000 - PROXY_DISCOVERY_URL=http://keycloak.example.com:8181/auth/realms/realmcom - PROXY_CLIENT_ID=webapp - PROXY_CLIENT_SECRET=0b57186c-e939-48ff-aa17-cfd3e361f65e - PROXY_UPSTREAM_URL=http://test-server:8000 ports: - "8282:3000" command: - "--verbose" - "--enable-refresh-tokens=true" - "--enable-default-deny=true" - "--resources=uri=/*" - "--enable-session-cookies=true" - "--encryption-key=AgXa7xRcoClDEU0ZDSH4X0XhL5Qy2Z2j" test-server: image: "test-server"-
xxSwordy over 5 yearsDid you ever find a solution? I am facing the same problem and have no idea how to fix this
-
-
christopher clark about 5 yearsI'm still receiving the same error, it looks like gatekeeper is still checking for client_id, even though I have confirmed that the token has the scope of the good-service.
-
popcorny almost 5 yearsWorks for me. Actually, the steps can be simpler. Client Scopes are shared mappers and roles. Here we can just add a mapper for my client. 1. edit my client 2. open the
mappertab 3. Create Protocol Mapper 'my-app-audience'. The value is just the same as this reply. -
 martin_wun over 2 yearsThanks a lot, the solution worked fine for me as described and saved my day. :)
martin_wun over 2 yearsThanks a lot, the solution worked fine for me as described and saved my day. :) -
Stealth Rabbi over 2 yearsWhen I add the mapper, my
audbecomes a list of [account,my-custom-client], and the audience validation still fails. -
 Max R. about 2 years@StealthRabbi you need to remove the audience resolve in Client Scopes -> roles -> Mappers
Max R. about 2 years@StealthRabbi you need to remove the audience resolve in Client Scopes -> roles -> Mappers