ldap_modify: Insufficient access (50) when changing password
In order to admin the 'cn=config' database you need the 'cn=config' admin, not the admin of the data DB. In debian such admin is root with SASL TLS External. Try
sudo ldapsearch -H ldapi:/// -Y EXTERNAL -b 'cn=config'
Once you've confirmed the above works, you can change the password. First, hash the value:
slappasswd -h {SSHA} -s "my_password"
Then, paste the hashed value into an ldif file such as ./change_ldap_password.ldif:
dn: olcDatabase={0}config,cn=config
changetype: modify
add: olcRootPW
olcRootPW: {SSHA}cZbRoOhRew8MBiWGSEOiFX0XqbAQwXUr
Finally, apply the ldif file:
sudo ldapmodify -H ldapi:/// -Y EXTERNAL -D 'cn=config' -f ./change_ldap_password.ldif
Changing passwords with ldapmodify is discouraged. If user exists (it is not this case), ldappasswd is way better.
Related videos on Youtube
Leo
I’m a Senior Site Reliability Engineer at Autonomic. I do Golang, Ruby, JS, Python, Elixir, as well as web scale devops with Terraform, Ansible, Kubernetes and Docker.
Updated on September 18, 2022Comments
-
Leo over 1 year
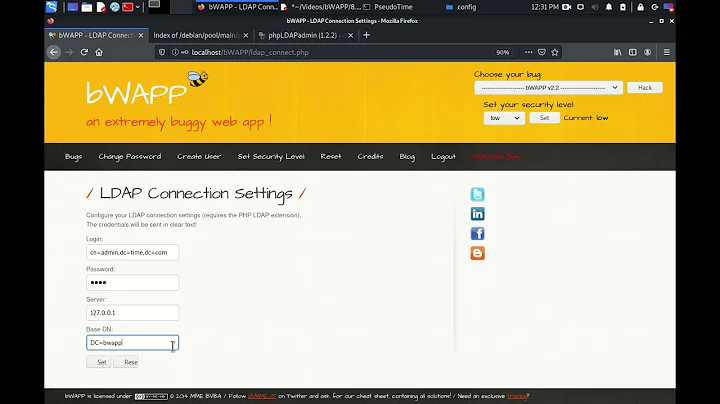
I'm trying to modify the LDAP admin password on a fresh OpenLDAP install on CentOS 6.7 (similar to RHEL 6.7).
I created a file called
change_ldap_password.ldif:# Hash your password: # slappasswd -h {SSHA} -s "my_password" # I also tried {1}hdb instead of {0}config dn: olcDatabase={0}config,cn=config changetype: modify add: olcRootPW olcRootPW: {SSHA}YP8q2haCD1POSzQC3GAuBdrfaHh+/Y49When I run the following command as root, I get an access error:
# ldapmodify -x -W -D "cn=admin,dc=my_domain,dc=com" -f ./change_ldap_password.ldif Enter LDAP Password: modifying entry "olcDatabase={0}config,cn=config" ldap_modify: Insufficient access (50)Here's the output of ldapwhoami:
# ldapwhoami -x -W -D "cn=admin,dc=my_domain,dc=com" Enter LDAP Password: dn:cn=admin,dc=my_domain,dc=comHere's the result of grepping for olcRoot in cn=config:
# grep -R olcRoot /etc/openldap/slapd.d/cn=config /etc/openldap/slapd.d/cn=config/olcDatabase={1}hdb.ldif:olcRootDN: cn=admin,dc=my_domain,dc=com /etc/openldap/slapd.d/cn=config/olcDatabase={1}hdb.ldif:olcRootPW:: ...Here's the debug info for ldapmodify:
# ldapmodify -x -W -D "cn=admin,dc=my_domain,dc=com" -f ./change_ldap_password.ldif -d1 ldap_create Enter LDAP Password: ldap_sasl_bind ldap_send_initial_request ldap_new_connection 1 1 0 ldap_int_open_connection ldap_connect_to_host: TCP localhost:389 ldap_new_socket: 4 ldap_prepare_socket: 4 ldap_connect_to_host: Trying 127.0.0.1:389 ldap_pvt_connect: fd: 4 tm: -1 async: 0 attempting to connect: connect errno: 111 ldap_close_socket: 4 ldap_int_open_connection ldap_connect_to_path ldap_new_socket: 4 ldap_connect_to_path: Trying /var/run/ldapi ldap_connect_timeout: fd: 4 tm: -1 async: 0 ldap_ndelay_on: 4 ldap_close_socket: 4 ldap_int_open_connection ldap_connect_to_host: TCP localhost:636 ldap_new_socket: 4 ldap_prepare_socket: 4 ldap_connect_to_host: Trying 127.0.0.1:636 ldap_pvt_connect: fd: 4 tm: -1 async: 0 attempting to connect: connect success TLS: certdb config: configDir='/etc/openldap/certs' tokenDescription='ldap(0)' certPrefix='' keyPrefix='' flags=readOnly TLS: using moznss security dir /etc/openldap/certs prefix . TLS: certificate [CN=my_server.my_domain.com] is valid TLS certificate verification: subject: CN=my_server.my_domain.com, issuer: CN=my_server.my_domain.com, cipher: AES-256, security level: high, secret key bits: 256, total key bits: 256, cache hits: 0, cache misses: 0, cache not reusable: 0 ldap_open_defconn: successful ldap_send_server_request ber_scanf fmt ({it) ber: ber_scanf fmt ({i) ber: ber_flush2: 50 bytes to sd 4 ldap_result ld 0x184a340 msgid 1 wait4msg ld 0x184a340 msgid 1 (infinite timeout) wait4msg continue ld 0x184a340 msgid 1 all 1 ** ld 0x184a340 Connections: * host: (null) port: 636 (default) refcnt: 2 status: Connected last used: Fri Oct 30 14:04:24 2015 ** ld 0x184a340 Outstanding Requests: * msgid 1, origid 1, status InProgress outstanding referrals 0, parent count 0 ld 0x184a340 request count 1 (abandoned 0) ** ld 0x184a340 Response Queue: Empty ld 0x184a340 response count 0 ldap_chkResponseList ld 0x184a340 msgid 1 all 1 ldap_chkResponseList returns ld 0x184a340 NULL ldap_int_select read1msg: ld 0x184a340 msgid 1 all 1 ber_get_next ber_get_next: tag 0x30 len 12 contents: read1msg: ld 0x184a340 msgid 1 message type bind ber_scanf fmt ({eAA) ber: read1msg: ld 0x184a340 0 new referrals read1msg: mark request completed, ld 0x184a340 msgid 1 request done: ld 0x184a340 msgid 1 res_errno: 0, res_error: <>, res_matched: <> ldap_free_request (origid 1, msgid 1) ldap_parse_result ber_scanf fmt ({iAA) ber: ber_scanf fmt (}) ber: ldap_msgfree modifying entry "olcDatabase={0}config,cn=config" ldap_modify_ext ldap_send_initial_request ldap_send_server_request ber_scanf fmt ({it) ber: ber_scanf fmt ({) ber: ber_flush2: 102 bytes to sd 4 ldap_result ld 0x184a340 msgid 2 wait4msg ld 0x184a340 msgid 2 (timeout 100000 usec) wait4msg continue ld 0x184a340 msgid 2 all 1 ** ld 0x184a340 Connections: * host: (null) port: 636 (default) refcnt: 2 status: Connected last used: Fri Oct 30 14:04:24 2015 ** ld 0x184a340 Outstanding Requests: * msgid 2, origid 2, status InProgress outstanding referrals 0, parent count 0 ld 0x184a340 request count 1 (abandoned 0) ** ld 0x184a340 Response Queue: Empty ld 0x184a340 response count 0 ldap_chkResponseList ld 0x184a340 msgid 2 all 1 ldap_chkResponseList returns ld 0x184a340 NULL ldap_int_select read1msg: ld 0x184a340 msgid 2 all 1 ber_get_next ber_get_next: tag 0x30 len 12 contents: read1msg: ld 0x184a340 msgid 2 message type modify ber_scanf fmt ({eAA) ber: read1msg: ld 0x184a340 0 new referrals read1msg: mark request completed, ld 0x184a340 msgid 2 request done: ld 0x184a340 msgid 2 res_errno: 50, res_error: <>, res_matched: <> ldap_free_request (origid 2, msgid 2) ldap_parse_result ber_scanf fmt ({iAA) ber: ber_scanf fmt (}) ber: ldap_msgfree ldap_err2string ldap_modify: Insufficient access (50) ldap_free_connection 1 1 ldap_send_unbind ber_flush2: 7 bytes to sd 4 ldap_free_connection: actually freedIf I enter a wrong password, the error changes from Insufficient Access to Invalid Credentials:
ldap_bind: Invalid credentials (49)I saw this ServerFault question, but that one was about a user with limited privileges rather than admin or root.
How do I get past the
ldap_modify: Insufficient access (50)error?Why does root identifying as LDAP admin not have access to change the password?
I'm ok reinstalling slapd if that's the recommended solution. I'd like to resolve this error before moving further.
Edit: Going to cn=config on ldapi:/// gives the following error:
# ldapsearch -H ldapi:/// -Y EXTERNAL -b 'cn=config' -d1 ldap_url_parse_ext(ldapi:///) ldap_create ldap_url_parse_ext(ldapi:///??base) ldap_sasl_interactive_bind: user selected: EXTERNAL ldap_int_sasl_bind: EXTERNAL ldap_new_connection 1 1 0 ldap_int_open_connection ldap_connect_to_path ldap_new_socket: 3 ldap_connect_to_path: Trying /var/run/ldapi ldap_connect_timeout: fd: 3 tm: -1 async: 0 ldap_ndelay_on: 3 ldap_close_socket: 3 ldap_msgfree ldap_err2string ldap_sasl_interactive_bind_s: Can't contact LDAP server (-1)I think I have
ldapi://defined in/etc/openldap/ldap.conf, but I'm not sure aboutldapi:///# # LDAP Defaults # # See ldap.conf(5) for details # This file should be world readable but not world writable. BASE dc=my_domain,dc=com #URI ldap://ldap.example.com ldap://ldap-master.example.com:666 URI ldap:// ldapi:// ldaps:// #SIZELIMIT 12 #TIMELIMIT 15 #DEREF never TLS_CACERTDIR /etc/openldap/certsEdit 2: I get the same
ldap_sasl_interactive_bind_s: Can't contact LDAP server (-1)error after stopping the firewall (service iptables stop), so the firewall is not the issue. -
Leo over 8 years
ldapsearch -d1 -b "cn=config" -Y EXTERNALgivesldap_sasl_interactive_bind_s: Unknown authentication method (-6) additional info: SASL(-4): no mechanism available: -
Leo over 8 years
ldapsearch -d1 -b "cn=config" -Wgivesldap_sasl_interactive_bind_s: Local error (-2) additional info: SASL(-1): generic failure: GSSAPI Error: Unspecified GSS failure. Minor code may provide more information (Credentials cache file '/tmp/krb5cc_0' not found) -
Leo over 8 years
ldapsearch -d1 -b "cn=config" -xgivesresult: 32 No such object -
Leo over 8 yearsVerbatim, I get
ldap_sasl_interactive_bind_s: Can't contact LDAP server (-1). I've added the full details to the question. -
 84104 over 8 yearsMinor correction: That's external peercred. External TLS uses certificates and will work over tcp connections.
84104 over 8 yearsMinor correction: That's external peercred. External TLS uses certificates and will work over tcp connections. -
 473183469 over 8 years@Leons: first of all I would start a new question as it is unrelated to access to 'cn=config'. Next: I would check presence of unix socket file
473183469 over 8 years@Leons: first of all I would start a new question as it is unrelated to access to 'cn=config'. Next: I would check presence of unix socket file/var/run/ldapi(from your logs) with correct ownership. Then, is your slapd started with-h [ldap or ldaps or both] ldapi:///' (i.e. isldapi:///` present)? Checking logs on slapd starting, does it report to communicate on the same unix socket client lib searches for? Maybe a new question is not a bad idea! -
Leo over 8 years@473183469: Follow-up question with diagnostics: serverfault.com/questions/733637/…
-
Leo over 8 yearsThanks everyone! After fixing my
/etc/sysconfig/ldapconfiguration to enableldapi:///per serverfault.com/questions/733637/… , I was able to runldapmodify -H ldapi:/// -Y EXTERNAL -D 'cn=config' -f ./change_ldap_password.ldifand change the admin password.