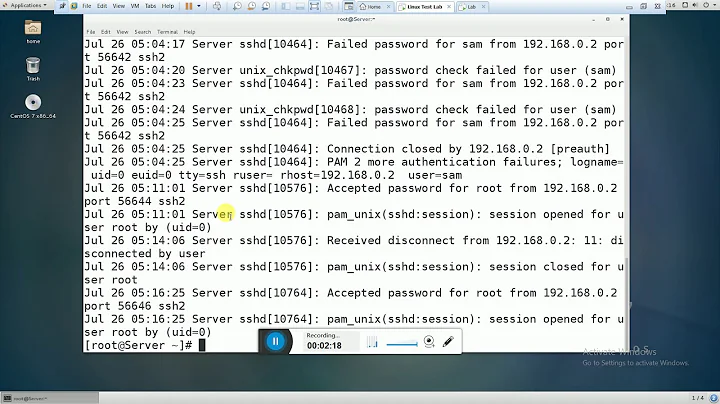
Limiting Failed SSH Logins
Solution 1
You might be interested in fail2ban.
Solution 2
Simply modify your /etc/ssh/sshd_config file; add
MaxAuthTries 5
and restart sshd.
Solution 3
I use an iptables rule that limits SSH connections to no more than 10 per minute. After 10 connections (or attempts), new incoming connections from that IP are dropped, which is usually enough to make the would-be crackers go away.
iptables -A INPUT -p tcp --dport 22 -m state --state NEW -m recent --update --seconds 60 --hitcount 10 --rttl --name SSH -j DROP
Solution 4
Another dynamic connection blocker based on failed login attempts is DenyHosts. It functions similarly to fail2ban, but specifically targets ssh login attempts. The last time I set it up, I found it very easy to configure.
Related videos on Youtube
Comments
-
nitins over 1 year
I would like to limit failure retries on my Fedora machine to 5. I think I can accomplish it with PAM. But was unable to to do this.
I have referred to this article to do this
http://www.puschitz.com/SecuringLinux.shtml
Please provide suggestions
-
nitins almost 14 yearsbut which one will have overrding effect? PAM or MaxAuthTries in sshd_config ?
-
Govindarajulu almost 14 yearsI second this. If you want to secure your box, you do not just want to limit loging retries. You want to block the attempting IP for a prolonged period of time. Fail2ban does this automatically and just plain rocks at it. Try it out.
-
 artifex almost 14 yearsI like the iptables approach. Mainly because after awhile denyhosts and similiar tools get huge databases which takes, in some cases, dire CPU cycles. iptables is much more efficient this way. In 150 days, denyhosts has taken 37 cpu hours on a machine with 7k plus entries in its database.
artifex almost 14 yearsI like the iptables approach. Mainly because after awhile denyhosts and similiar tools get huge databases which takes, in some cases, dire CPU cycles. iptables is much more efficient this way. In 150 days, denyhosts has taken 37 cpu hours on a machine with 7k plus entries in its database. -
 Sharjeel Aziz almost 14 years+1 DenyHosts has worked for me too.
Sharjeel Aziz almost 14 years+1 DenyHosts has worked for me too. -
user1807902 almost 14 yearsEven more.. it's not limited to ssh. Actually it's not limited at all! With this handy tool you can do the same for FTP, Apache, and whatever you want (read - whatever provides logs).
-
 warren almost 14 yearslooks like this answer, in conjunction with serverfault.com/questions/143323/limiting-failed-ssh-logins/… would be pretty good
warren almost 14 yearslooks like this answer, in conjunction with serverfault.com/questions/143323/limiting-failed-ssh-logins/… would be pretty good -
user9517 almost 10 yearsAs the accepted answer says, fail2ban is the goto solution for this.
-
Ben Penwell almost 10 yearsagree, this is a very good tool for this
-
 Mike Waters almost 10 yearsThanks. What I have is much simpler, but I'll give fail2ban a closer look.
Mike Waters almost 10 yearsThanks. What I have is much simpler, but I'll give fail2ban a closer look. -
Sergei G over 6 yearsdenyhosts is a simple and good alternative github.com/denyhosts/denyhosts