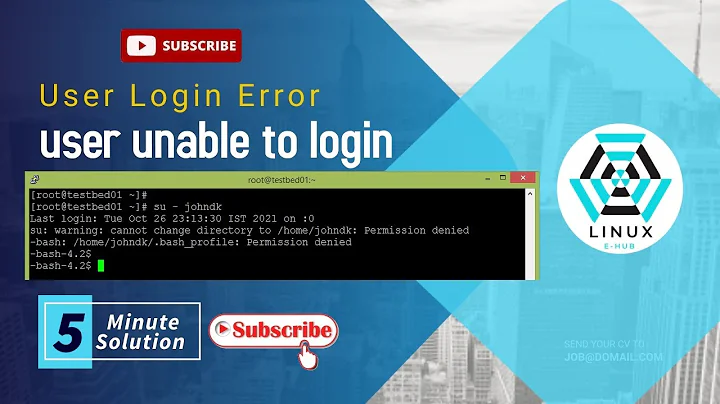
Linux User not able to login
Solution 1
look for any relevant entries under /var/log/secure or /var/log/auth.log. Also, make sure that you don't have custom rules added under /etc/security/access.conf which might access to the server for that user.
Those logs will contain information about failed logins and may indicate clearly what went wrong.
The /etc/security/access.conf file specifies (user/group, host), (user/group, network/netmask) or (user/group, tty) combinations for which a login will be either accepted or refused.
Solution 2
Before trying these commands, either you need to become root user or you will have to run commands with sudo.
After each change in file /etc/ssh/sshd_config, you need to restart ssh service. Command is:
systemctl restart sshd.service
Any new user with which you want to do ssh login with password, you need to add that user to AllowUsers with space as separator for each user.
Eg:
AllowUsers root testUser
For root user to be active in login through ssh, you need to check PermitRootLogin, its value should be yes in file /etc/ssh/sshd_config
For Example: check the below sshd_config file. With this configuration you can also do ssh login using testUser and root user:
# $OpenBSD: sshd_config,v 1.100 2016/08/15 12:32:04 naddy Exp $
# This is the sshd server system-wide configuration file. See
# sshd_config(5) for more information.
# This sshd was compiled with PATH=/usr/bin:/bin:/usr/sbin:/sbin
# The strategy used for options in the default sshd_config shipped with
# OpenSSH is to specify options with their default value where
# possible, but leave them commented. Uncommented options override the
# default value.
#Port 22
#AddressFamily any
#ListenAddress 0.0.0.0
#ListenAddress ::
#HostKey /etc/ssh/ssh_host_rsa_key
#HostKey /etc/ssh/ssh_host_ecdsa_key
#HostKey /etc/ssh/ssh_host_ed25519_key
# Ciphers and keying
#RekeyLimit default none
# Logging
#SyslogFacility AUTH
#LogLevel INFO
# Authentication:
#LoginGraceTime 2m
PermitRootLogin yes
#StrictModes yes
#MaxAuthTries 6
#MaxSessions 10
#PubkeyAuthentication yes
# Expect .ssh/authorized_keys2 to be disregarded by default in future.
#AuthorizedKeysFile .ssh/authorized_keys .ssh/authorized_keys2
#AuthorizedPrincipalsFile none
#AuthorizedKeysCommand none
#AuthorizedKeysCommandUser nobody
# For this to work you will also need host keys in /etc/ssh/ssh_known_hosts
#HostbasedAuthentication no
# Change to yes if you don't trust ~/.ssh/known_hosts for
# HostbasedAuthentication
#IgnoreUserKnownHosts no
# Don't read the user's ~/.rhosts and ~/.shosts files
#IgnoreRhosts yes
# To disable tunneled clear text passwords, change to no here!
#PasswordAuthentication yes
#PermitEmptyPasswords no
# Change to yes to enable challenge-response passwords (beware issues with
# some PAM modules and threads)
ChallengeResponseAuthentication no
# Kerberos options
#KerberosAuthentication no
#KerberosOrLocalPasswd yes
#KerberosTicketCleanup yes
#KerberosGetAFSToken no
# GSSAPI options
#GSSAPIAuthentication no
#GSSAPICleanupCredentials yes
#GSSAPIStrictAcceptorCheck yes
#GSSAPIKeyExchange no
# Set this to 'yes' to enable PAM authentication, account processing,
# and session processing. If this is enabled, PAM authentication will
# be allowed through the ChallengeResponseAuthentication and
# PasswordAuthentication. Depending on your PAM configuration,
# PAM authentication via ChallengeResponseAuthentication may bypass
# the setting of "PermitRootLogin without-password".
# If you just want the PAM account and session checks to run without
# PAM authentication, then enable this but set PasswordAuthentication
# and ChallengeResponseAuthentication to 'no'.
UsePAM yes
#AllowAgentForwarding yes
#AllowTcpForwarding yes
#GatewayPorts no
X11Forwarding yes
#X11DisplayOffset 10
#X11UseLocalhost yes
#PermitTTY yes
PrintMotd no
#PrintLastLog yes
#TCPKeepAlive yes
#UseLogin no
#UsePrivilegeSeparation sandbox
#PermitUserEnvironment no
#Compression delayed
#ClientAliveInterval 0
#ClientAliveCountMax 3
#UseDNS no
#PidFile /var/run/sshd.pid
#MaxStartups 10:30:100
#PermitTunnel no
#ChrootDirectory none
#VersionAddendum none
# no default banner path
#Banner none
# Allow client to pass locale environment variables
AcceptEnv LANG LC_*
# override default of no subsystems
Subsystem sftp /usr/lib/openssh/sftp-server
# Example of overriding settings on a per-user basis
#Match User anoncvs
# X11Forwarding no
# AllowTcpForwarding no
# PermitTTY no
# ForceCommand cvs server
AllowUsers root testUser
Solution 3
Next to adding the user on the Linux machine, you'll have to generate a key (protocol type 2, preferably RSA) for that user as well. You can find instructions for that using Putty's key generator here.
Select all of the text in the ‘Public key for pasting into authorized_keys file’ box in putty's key generator, paste it into a text editor and save it under the name authorized_keys.
In the home directory of the new user on the Linux machine, create a .ssh directory if it doesn't exist. This directory should be owned by the user, and only that user should have access to it (chmod 700 .ssh) Copy the authorized_keys file to this directory. You should change the permissions of that file with chmod 0600, and change ownership to the user.
Now the user should be able to log in.
Related videos on Youtube
Ankit Vashistha
Updated on September 18, 2022Comments
-
 Ankit Vashistha over 1 year
Ankit Vashistha over 1 yearI am trying to create new users using
useraddcommand using root credentials it is getting created properly but when I log in with the newly created user with its credentials using a PuTTY Console, I am able to enter the username but when I give the password, it hangs there for a long time until the PuTTY window session timeout happens and the window is closed. However when I use root credentials, it quickly enters the session.I tried checking the
AllowUsersunder file/etc/ssh/sshd_configbut I didn't find any matching entry, so, I manually tried addingAllowUsers temipuserwheretemipuseris the username I created. Post making this change from another PuTTY Console I again tried entering this username but it is again the same. I am totally clueless why is this happening.Another thing is, if I add any user, say just
temipuser, to theAllowUsersentry in thesshd_configfile, will the root user still have access or will it not get access? I don't want to screw the things here. I understandAllowUserslets only the specified users and denies others.-
 Admin about 11 years
Admin about 11 years/var/log/auth.logshould use some useful information. Can you add anything you find to your question? -
 Admin about 11 yearsAgreed. Also adjust
Admin about 11 yearsAgreed. Also adjust/etc/ssh/sshd_configto setLogLeveltoDebugwhile you try logging in to get as much information as possible. -
 Admin about 11 yearsSome Unix stuff chokes on usernames longer than 8 characters, your
Admin about 11 yearsSome Unix stuff chokes on usernames longer than 8 characters, yourtemipuseris 9... Can you log in locally (i.e., not over ssh)? BTW, I don't know offhand ifsshdreads its configuration each time, you might have to restart it (or force it to reread configuration) after changes. -
 Admin about 11 yearsAre you able to ssh locally? I.e. what happens if you log in as root and then run
Admin about 11 yearsAre you able to ssh locally? I.e. what happens if you log in as root and then runssh temipuser@localhostand enter the user's password when prompted? -
 Admin about 11 yearsWhen i run ssh temipuser@<ip_of_server>, the same happens, it accepts username but hangs when i give password.
Admin about 11 yearsWhen i run ssh temipuser@<ip_of_server>, the same happens, it accepts username but hangs when i give password. -
 Admin about 11 yearsI cannot see any /var/log/auth.log file. Ok, after changing the
Admin about 11 yearsI cannot see any /var/log/auth.log file. Ok, after changing the/etc/ssh/sshd_configLogLeveltoDEBUG, i restarted sshd. I cannot see any auth.log file still. -
 Admin about 11 yearsThe RHEL distribution is: Red Hat Enterprise Linux Server release 5.5 (Tikanga). I tried the ssh command and the same happens for it too, it take username and then hangs after i give password.
Admin about 11 yearsThe RHEL distribution is: Red Hat Enterprise Linux Server release 5.5 (Tikanga). I tried the ssh command and the same happens for it too, it take username and then hangs after i give password. -
 Admin about 11 yearsok, I tried tail -f /var/log/secure and from another window i tried logging in to the ssh using the new username/pass and i can see the following messages:
Admin about 11 yearsok, I tried tail -f /var/log/secure and from another window i tried logging in to the ssh using the new username/pass and i can see the following messages:debug1: PAM: setting PAM_TTY to "ssh" debug1: temporarily_use_uid: 778/516 (e=0/0) debug1: trying public key file /home/tuser/.ssh/authorized_keys debug1: restore_uid: 0/0 debug1: temporarily_use_uid: 778/516 (e=0/0) debug1: trying public key file /home/tuser/.ssh/authorized_keys2 debug1: restore_uid: 0/0 Failed publickey for tuser from <ip_of_server> port 32352 ssh2
-
-
user3850506 about 11 yearsYou do not need a key in order to login via SSH. Password login is enabled by default and if the OP had disabled it, he/she would probably remember