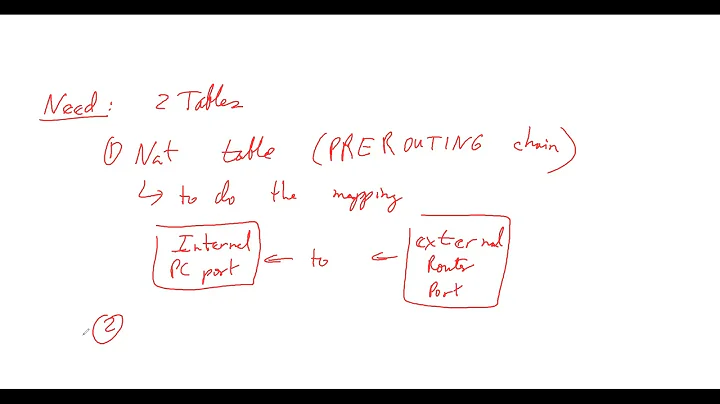
LXC, Port forwarding and iptables
Solution 1
Seems you have blocked 7002 port on 10.0.3.1 as your default policy is DROP
Try adding it to INPUT rules:
iptables -A INPUT -p tcp --dport 7002 -j ACCEPT
Solution 2
I ran into the same problem. I have not found solution yet, but following I note down some observations.
I have a host ${host} machine (Ubuntu 12.04) and it runs a guest machine via LXC. The guest is on IP 10.0.3.248 and gateway is 10.0.3.1. I run a web server in the guest and want to port forward traffic from ${host}:8888 to 10.0.3.248:80. Following is the relevant iptables entries:
-A PREROUTING -p tcp --dport 8888 -j DNAT --to-destination 10.0.3.248:80
-A POSTROUTING -j MASQUERADE
With the current configuration, I can successfully visit the web server on 10.0.3.248:80 from another physical machine. However, it fails when I try to visit 10.0.3.248:80 from ${host}. Maybe you can try to visit that service inside LXC from another machine.
My understanding is that, when I visit from ${host}, the packet go through loopback interface and enters the INPUT chain directly. Although I allow everything on INPUT, there is no service listening at ${host}:8888. From wireshark, I see a RST is sent received. When I visit from another physical machine, the packet goes into PREROUTING chain and was DNAT-ed as expected.
One related post:
Related videos on Youtube
Roberto Aloi
Because of my academic career, I’m interested in software engineering, human - computer interaction, user interfaces, graphics, databases, web applications and more. As the final thesis for my Bachelor's degree, I implemented a garbage collector for a Java Virtual Machine (named Juice) targeted to embedded systems with real time requirements. As the final thesis for my Master's degree, I designed an access control mechanism for the Content Management System Joomla (www.joomla.org). It was successfully used for an e-learning solution. I spent my last years discovering the Erlang language and getting addicted to it.
Updated on September 18, 2022Comments
-
Roberto Aloi over 1 year
I have a LXC container (
10.0.3.2) running on a host. A service is running inside the container on port7000.From the host (
10.0.3.1,lxcbr0), I can reach the service:$ telnet 10.0.3.2 7000 Trying 10.0.3.2... Connected to 10.0.3.2. Escape character is '^]'.I'd love to make the service running inside the container accessible to the outer world. Therefore, I want to forward port
7002on the host to port7000on the container:iptables -t nat -A PREROUTING -p tcp --dport 7002 -j DNAT --to 10.0.3.2:7000Which results in (
iptables -t nat -L):DNAT tcp -- anywhere anywhere tcp dpt:afs3-prserver to:10.0.3.2:7000Still, I cannot access the service from the host using the forwarded port:
$ telnet 10.0.3.1 7002 Trying 10.0.3.1... telnet: Unable to connect to remote host: Connection refusedI feel like I'm missing something stupid here. What things should I check? What's a good strategy to debug these situations?
For completeness, here is how
iptablesare set on the host:iptables -F iptables -F -t nat iptables -F -t mangle iptables -X iptables -P INPUT DROP iptables -P FORWARD ACCEPT iptables -P OUTPUT ACCEPT iptables -A INPUT -p tcp --dport 22 -j ACCEPT iptables -A INPUT -p icmp --icmp-type echo-request -j ACCEPT iptables -A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE iptables -t nat -A POSTROUTING -o lxcbr0 -j MASQUERADE iptables -t nat -A PREROUTING -p tcp --dport 7002 -j DNAT --to 10.0.3.2:7000-
Michael Härtl about 11 yearsDid you check the
INPUTchain? Maybe the policy isREJECTthere. -
Roberto Aloi about 11 yearsPolicy is
ACCEPT -
Roberto Aloi about 11 years
ip_forwardis set to1 -
Roberto Aloi about 11 years
FORWARDpolicy is alsoACCEPT -
Michael Härtl about 11 yearsNext things i would try: Check if any packet makes it to the LXC, e.g with
tcpdump. Also watch the different counters in your iptables, whenever you try to connect. It usually gives you a hint, where a packet is lost. If packets arrive at LXC then check/etc/hosts.allowand/etc/hosts.denyand your telnet configuration. Maybe it's blocking IPs outside your network. -
Roberto Aloi about 11 yearsAdded the complete specs for
iptables. -
Roberto Aloi about 11 years
tcpdump(used on-i lo) shows a rejection. No packets reach the LXC, apparently. -
Roberto Aloi about 11 years
-
Laurentiu Roescu almost 11 yearsI think this is causing you troubles: iptables -t nat -A POSTROUTING -o lxcbr0 -j MASQUERADE. Why do you need that?
-
 andresgongora about 6 yearsMight be related to this: serverfault.com/questions/475065/iptables-port-forwarding-a-b-a have you tried accessing port 7002 from another computer as the host? i.e telnet $HOSTIP 7002 (where $HOSTIP is the IP of the machine hosting the LXC contianer, say 192.168.1.15 if you are on a common LAN).
andresgongora about 6 yearsMight be related to this: serverfault.com/questions/475065/iptables-port-forwarding-a-b-a have you tried accessing port 7002 from another computer as the host? i.e telnet $HOSTIP 7002 (where $HOSTIP is the IP of the machine hosting the LXC contianer, say 192.168.1.15 if you are on a common LAN). -
thistleknot almost 3 yearsall I needed was the last line
-