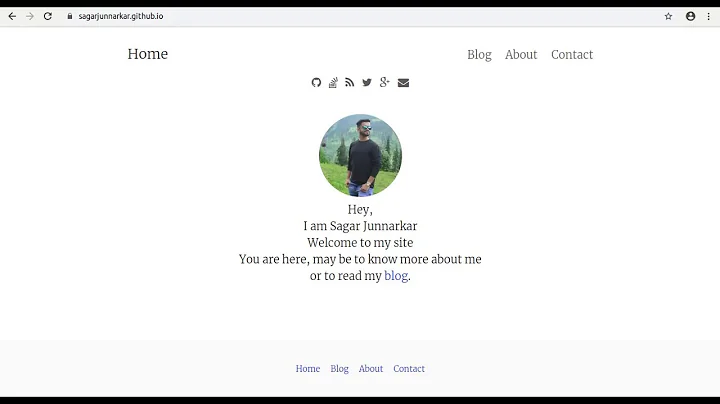
Multiple GitHub Accounts & SSH Config
Solution 1
Andy Lester's response is accurate but I found an important extra step I needed to make to get this to work. In trying to get two profiles set up, one for personal and one for work, my ~/.ssh/config was roughly as follows:
Host me.github.com
HostName github.com
PreferredAuthentications publickey
IdentityFile ~/.ssh/me_rsa
Host work.github.com
HostName github.com
PreferredAuthentications publickey
IdentityFile ~/.ssh/work_rsa
My work profile didn't take until I did a ssh-add ~/.ssh/work_rsa. After that connections to github used the correct profile. Previously they defaulted to the first public key.
For Could not open a connection to your authentication agent when using ssh-add,
check:
https://stackoverflow.com/a/17695338/1760313
Solution 2
I recently had to do this and had to sift through all these answers and their comments to eventually piece the information together, so I'll put it all here, in one post, for your convenience:
Step 1: ssh keys
Create any keypairs you'll need. In this example I've named me default/original 'id_rsa' (which is the default) and my new one 'id_rsa-work':
ssh-keygen -t rsa -C "[email protected]"
Step 2: ssh config
Set up multiple ssh profiles by creating/modifying ~/.ssh/config. Note the slightly differing 'Host' values:
# Default GitHub
Host github.com
HostName github.com
PreferredAuthentications publickey
IdentityFile ~/.ssh/id_rsa
# Work GitHub
Host work.github.com
HostName github.com
PreferredAuthentications publickey
IdentityFile ~/.ssh/id_rsa_work
Step 3: ssh-add
You may or may not have to do this. To check, list identity fingerprints by running:
$ ssh-add -l
2048 1f:1a:b8:69:cd:e3:ee:68:e1:c4:da:d8:96:7c:d0:6f stefano (RSA)
2048 6d:65:b9:3b:ff:9c:5a:54:1c:2f:6a:f7:44:03:84:3f [email protected] (RSA)
If your entries aren't there then run:
ssh-add ~/.ssh/id_rsa_work
Step 4: test
To test you've done this all correctly, I suggest the following quick check:
$ ssh -T [email protected]
Hi stefano! You've successfully authenticated, but GitHub does not provide shell access.
$ ssh -T [email protected]
Hi stefano! You've successfully authenticated, but GitHub does not provide shell access.
Note that you'll have to change the hostname (github / work.github) depending on what key/identity you'd like to use. But now you should be good to go! :)
Solution 3
Let's say alice is a github.com user, with 2 or more private repositories repoN.
For this example we'll work with just two repositories named repo1 and repo2
https://github.com/alice/repo1
https://github.com/alice/repo2
You need to be to pull from these repositories without entering a passwords probably on a server, or on multiple servers.
You want to perform git pull origin master for example, and you want this to happen without asking for a password.
You don't like dealing with ssh-agent, you have discovered (or you're discovering now) about ~/.ssh/config a file that let's your ssh client know what private key to use depending on Hostname and username, with a simple configuration entry that looks like this:
Host github.com
HostName github.com
User git
IdentityFile /home/alice/.ssh/alice_github.id_rsa
IdentitiesOnly yes
So you went ahead and created your (alice_github.id_rsa, alice_github.id_rsa.pub) keypair, you then also went to your repository's .git/config file and you modified the url of your remote origin to be something like this:
[remote "origin"]
url = "ssh://[email protected]/alice/repo1.git"
And finally you went to the repository Settings > Deploy keys section and added the contents of alice_github.id_rsa.pub
At this point you could do your git pull origin master without entering a password without issue.
but what about the second repository?
So your instinct will be to grab that key and add it to repo2's Deploy keys, but github.com will error out and tell you that the key is already being used.
Now you go and generate another key (using ssh-keygen -t rsa -C "[email protected]" without passwords of course), and so that this doesn't become a mess, you will now name your keys like this:
-
repo1keypair:(repo1.alice_github.id_rsa, repo1.alice_github.id_rsa.pub) -
repo2keypair:(repo2.alice_github.id_rsa, repo2.alice_github.id_rsa.pub)
You will now put the new public key on repo2's Deploy keys configuration at github.com, but now you have an ssh problem to deal with.
How can ssh tell which key to use if the repositories are hosted on the same github.com domain?
Your .ssh/config file points to github.com and it doesn't know which key to use when it's time to do the pull.
So I found a trick with github.com. You can tell your ssh client that each repository lives in a different github.com subdomain, in these cases, they will be repo1.github.com and repo2.github.com
So first thing is editing the .git/config files on your repo clones, so they look like this instead:
For repo1
[remote "origin"]
url = "ssh://[email protected]/alice/repo1.git"
For repo2
[remote "origin"]
url = "ssh://[email protected]/alice/repo2.git"
And then, on your .ssh/config file, now you will be able to enter a configuration for each subdomain :)
Host repo1.github.com
HostName github.com
User git
IdentityFile /home/alice/.ssh/repo1.alice_github.id_rsa
IdentitiesOnly yes
Host repo2.github.com
HostName github.com
User git
IdentityFile /home/alice/.ssh/repo2.alice_github.id_rsa
IdentitiesOnly yes
Now you are able to git pull origin master without entering any passwords from both repositories.
If you have multiple machines, you could copy the keys to each of the machines and reuse them, but I'd advise doing the leg work to generate 1 key per machine and repo. You will have a lot more keys to handle, but you will be less vulnerable if one gets compromised.
Solution 4
I have 2 accounts on github, and here is what I did (on linux) to make it work.
Keys
- Create 2 pair of rsa keys, via
ssh-keygen, name them properly, so that make life easier. - Add private keys to local agent via
ssh-add path_to_private_key - For each github account, upload a (distinct) public key.
Configuration
~/.ssh/config
Host github-kc
Hostname github.com
User git
IdentityFile ~/.ssh/github_rsa_kc.pub
# LogLevel DEBUG3
Host github-abc
Hostname github.com
User git
IdentityFile ~/.ssh/github_rsa_abc.pub
# LogLevel DEBUG3
Set remote url for repo:
For repo in Host
github-kc:git remote set-url origin git@github-kc:kuchaguangjie/pygtrans.gitFor repo in Host
github-abc:git remote set-url origin git@github-abc:abcdefg/yyy.git
Explaination
Options in ~/.ssh/config:
Hostgithub-<identify_specific_user>
Host could be any value that could identify a host plus an account, it don't need to be a real host, e.ggithub-kcidentify one of my account on github for my local laptop,When set remote url for a git repo, this is the value to put after
git@, that's how a repo maps to a Host, e.ggit remote set-url origin git@github-kc:kuchaguangjie/pygtrans.git- [Following are sub options of
Host] Hostname
specify the actual hostname, just usegithub.comfor github,Usergit
the user is alwaysgitfor github,IdentityFile
specify key to use, just put the path the a public key,LogLevel
specify log level to debug, if any issue,DEBUG3gives the most detailed info.
Solution 5
Use the IdentityFile parameter in your ~/.ssh/config:
Host github.com
HostName github.com
IdentityFile ~/.ssh/github.rsa
User petdance
Related videos on Youtube
radesix
A born software engineer influenced by German engineering, house music, and sky diving
Updated on February 21, 2021Comments
-
radesix over 3 years
I'm having some trouble getting two different SSH keys/GitHub accounts to play well together. I have the following setup:
Repos accessible from one account using
[email protected]:accountnameRepos accessible from another account using
[email protected]:anotheraccountEach account has its own SSH key. Both SSH keys have been added and I have created a config file. I don't believe the config file is correct though. I'm not quite sure how to specify that repos accessed using
[email protected]:accountnameshould useid_rsaand[email protected]:anotheraccountshould useid_rsa_anotheraccount.-
jgreen about 5 yearsI found this link helpful medium.freecodecamp.org/…
-
mc01 about 5 yearsI have 3 separate SSH identities in ~/.ssh/config. The one for school server has a passcode; the 2 for separate work/personal GitHub accts do not. Running
git pullkept failing & asking for the school passcode, despite separate Identity files, "IdentitiesOnly=yes," separate domains & Hostnames, all present inssh-add -l... The uni key was 'first' regardless of that setup. Had to move its section below the others in .ssh/config, and nowgit pullfrom both GitHub accts succeeds w/o asking for uni ssh password. -
 Julius Š. almost 4 yearsThat is answered in detail here superuser.com/questions/232373/…
Julius Š. almost 4 yearsThat is answered in detail here superuser.com/questions/232373/…
-
-
radesix almost 14 yearsThanks but this isn't quite accurate. I found the answer and shared below.
-
 Andy Lester almost 14 yearsI'm pretty sure my approach will work in your case. You can identify different users and different identity files. Just need to give each a different Host parameter on the config stanza.
Andy Lester almost 14 yearsI'm pretty sure my approach will work in your case. You can identify different users and different identity files. Just need to give each a different Host parameter on the config stanza. -
radesix almost 14 yearsAndy, according to the link I found below I needed to drop the .com from the host. Once I did that it worked fine.
-
sage over 12 yearsThanks! - the
ssh-addwas what I was missing. -
phatmann over 12 yearsBy using ssh-add, I could see that I did not have the file permissions for the key set correctly. Once I fixed that everything worked. So thanks!
-
BobS about 12 yearsSee also doblock.com/articles/…. The key new piece of info there is that you may need to add the username ("work", in this example) to the hostname in the remote URL, i.e., [email protected]:work/my_repo.git (as opposed to "[email protected]...")
-
Casey about 12 yearsThis works: superuser.com/questions/232373/…
-
 Mechanical snail about 12 yearsTo fix the problem that "they defaulted to the first public key", add
Mechanical snail about 12 yearsTo fix the problem that "they defaulted to the first public key", addIdentitiesOnly yesto theHost *section of your~/.ssh/configfile. This tells ssh to actually use the IdentityFiles you specify, rather than spamming the server with all of them. -
James Raitsev almost 12 yearsWhat does your private key look like?
-
dolmen over 10 yearsJust use my
github-keygentool:github-keygen me work(Yes, that's all!). -
Von over 10 yearsNote if you have a 'Host *' block with an 'IdentityFile' statement, to force a particular key, you need to negate the target hostname for that Host block - e.g. 'Host * !work.github.com' - that, in addition to IdentitiesOnly as @Mechanicalsnail suggests will force a particular key.
-
gaurav.singharoy about 10 yearsThis is a great response. I had to use ssh-add to add both the ssh keys to utilize the config file.. Thanks :)
-
soulmachine over 9 yearsThanks a lot, I missed ssh-add and kept failing
-
Tulio over 9 yearsDon't forget to run
chmod 600 ~/.ssh/configif you has just created your config file. I was having trouble here. -
lucacerone over 9 yearsHi everybody, do you know how I can have git to use differente emails for different accounts? e.g. i would like to push to me.github.com using [email protected] and to work.github.com using [email protected]
-
 Admin over 9 years@lucacerone, you just need to change the user/email in the project scope. Change to the directory and type
Admin over 9 years@lucacerone, you just need to change the user/email in the project scope. Change to the directory and typegit config user.name 'John Smith'and thengit config user.email [email protected]. This will override your global config which can be seen bygit config --global user.name. -
JaskeyLam over 8 yearswhat is the "Host" and "Host" name should be set if I am not using github but gitlab set up at company?
-
 Saraschandraa over 8 yearsWhen i run ~/.ssh/config I get permission denied.
Saraschandraa over 8 yearsWhen i run ~/.ssh/config I get permission denied. -
JHH about 8 years@Saraschandraa It shouldn't be run. It's a config (text) file you create.
-
Mark Chackerian about 8 yearslovely -- did not need
ssh-add path_to_private_key-- probably because the agent isn't required in this case. The config file is explicitly defining the path to the keys. -
Daniel Viglione over 7 yearsThe only thing I like to add is when you run ssh-keygen -t rsa, it will give you a default file name, that is where you enter your custom file name.
-
Ashhar Hasan over 7 years@MarkChackerian I think you don't need
ssh-addbecause your keys aren't password protected or (if you're on a Mac) the OSX keychain is handling it for you.ssh-addprevents you from needing to enter the passphrase every time you access your keys. -
 Barry over 7 yearsOn a related note, is it possible to add a comment in the .ssh/config file without messing it up? Just curious. I assume you can add some with
Barry over 7 yearsOn a related note, is it possible to add a comment in the .ssh/config file without messing it up? Just curious. I assume you can add some with#. -
Paulo over 6 yearsbut what if there isn't a separate work doman like
work.github.com? -
cezar over 6 yearsThanks for the link to the turorial! You have a typo: the key names
id_rsa_proj1andproj1_id_rsashould actually be same. You could also add the part about.git/configsettings from the tutorial to your answer. -
cezar over 6 yearsYou still have a typo:
proj1.id_rsavs.proj1_id_rsa -
 TestingWithArif over 6 yearsOne of best answers. Also this video helped me. youtube.com/watch?v=fnSRBRiQIU8&feature=youtu.be
TestingWithArif over 6 yearsOne of best answers. Also this video helped me. youtube.com/watch?v=fnSRBRiQIU8&feature=youtu.be -
Val about 6 yearsI setup 3 hosts and this worked like a charm. I'm using Mac OSx High Sierra 10.13.
-
 Mike Miller about 6 yearsSpecifying the subdomain that matches the host in
Mike Miller about 6 yearsSpecifying the subdomain that matches the host in.ssh/configis the crucial step - thanks a lot for that -
basin almost 6 yearsThis can be improved with
insteadOf: Use different ssh keys for different github repos -
Dave Engineer over 5 yearsGood post, would be nice if this post included setting your git config 'email': help.github.com/articles/…
-
Anders almost 5 years@Paulo, as I understand this,
Hostis used to tell which configurations to use. It is the name you use on the command line. ButHostnamewill tellsshwhich machine to actually connect to. That is why they point/use the sameHostnamein bothHostStanzas. So,ssh me.github,comwill actually connect togithub.com, but use configurations fromme.github,com. -
 Tom N Tech over 3 yearsI find it very frustrating that all the answers to this and related questions omit the last part: the git clone command to run to checkout the project using the git CLI and the ~/.ssh/config file! :(
Tom N Tech over 3 yearsI find it very frustrating that all the answers to this and related questions omit the last part: the git clone command to run to checkout the project using the git CLI and the ~/.ssh/config file! :( -
uniquegino over 3 yearsIf anyone else is getting "error connecting to agent" when doing "ssh-agent", check this out stackoverflow.com/questions/52113738/…
-
 Dhaval over 3 yearsGreat, to the point and what I was looking for. Thanks
Dhaval over 3 yearsGreat, to the point and what I was looking for. Thanks -
CodeIntern about 3 yearsIs there any documentation that talks about appending
-account1to the github domain? After testing it, it definitely works, but it caught me by surprise because I haven't read about it anywhere. -
 Keshav Aggarwal almost 3 yearsssh-add ~/.ssh/work_rsa did the Trick, thanks a tonn!!!!
Keshav Aggarwal almost 3 yearsssh-add ~/.ssh/work_rsa did the Trick, thanks a tonn!!!! -
Des over 2 yearsNice explanation of the
Hostcomponent, thanks