Port can't open on Ubuntu 16.04
In my case, the issue was not running the service on the port. Actually the port was not listening with any application or service.
As you see in following output of netstat -tanp, there was no port on listening:
# netstat -tanp
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN 1121/mysqld
tcp 0 0 127.0.0.1:6379 0.0.0.0:* LISTEN 1127/redis-server 1
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 1096/sshd
tcp 0 332 172.31.1.100:22 5.116.231.153:28282 ESTABLISHED 7506/0
tcp6 0 0 :::443 :::* LISTEN 1158/apache2
tcp6 0 0 :::80 :::* LISTEN 1158/apache2
tcp6 0 0 :::22 :::* LISTEN 1096/sshd
tcp6 0 0 172.31.1.100:80 155.94.88.138:54138 TIME_WAIT -
I didn't consider this fact, because I believed the service is running as usual and I've got no errors!
Special thanks to Michael Hampton & Nasir Riley for their helpful comments under the question.
Related videos on Youtube
Saeed Sepehr
Updated on September 18, 2022Comments
-
 Saeed Sepehr over 1 year
Saeed Sepehr over 1 yearI have a Ubuntu 16 installed on a Hetzner's VPS. I want to open port 11121 which I did it several times before on other VPSs.
I've tried ufw & iptables but when I check, I see the port is still closed!
Hint: The only thing that happened for this VPS but not the previous one, was a checkmark for RDNS on Hetzner management panel, then I've typed the reversed public IP on a textbox and saved. But I wasn't sure about this and I deleted it again. The only thing that I guess is this action and its effect on NAT configs.
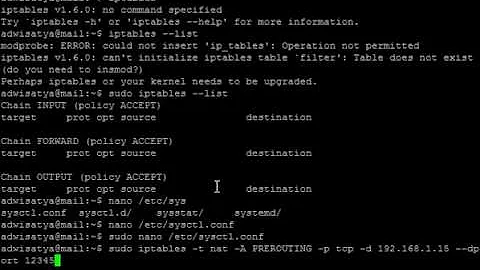
Even I entered allow command via iptables but it returned below status after that:
#iptables -L -nv Chain INPUT (policy ACCEPT 10248 packets, 4165K bytes) pkts bytes target prot opt in out source destination Chain FORWARD (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destination Chain OUTPUT (policy ACCEPT 10260 packets, 4288K bytes) pkts bytes target prot opt in out source destinationThen I installed UFW and I tried to open some ports manually, then enable the UFW and below is the status:
# ufw status Status: active To Action From -- ------ ---- 11121 ALLOW Anywhere 22 ALLOW Anywhere 80 ALLOW Anywhere 443 ALLOW Anywhere 11121 (v6) ALLOW Anywhere (v6) 22 (v6) ALLOW Anywhere (v6) 80 (v6) ALLOW Anywhere (v6) 443 (v6) ALLOW Anywhere (v6)and the status of iptables is showing as below now:
# iptables -S -P INPUT DROP -P FORWARD DROP -P OUTPUT ACCEPT -N ufw-after-forward -N ufw-after-input -N ufw-after-logging-forward -N ufw-after-logging-input -N ufw-after-logging-output -N ufw-after-output -N ufw-before-forward -N ufw-before-input -N ufw-before-logging-forward -N ufw-before-logging-input -N ufw-before-logging-output -N ufw-before-output -N ufw-logging-allow -N ufw-logging-deny -N ufw-not-local -N ufw-reject-forward -N ufw-reject-input -N ufw-reject-output -N ufw-skip-to-policy-forward -N ufw-skip-to-policy-input -N ufw-skip-to-policy-output -N ufw-track-forward -N ufw-track-input -N ufw-track-output -N ufw-user-forward -N ufw-user-input -N ufw-user-limit -N ufw-user-limit-accept -N ufw-user-logging-forward -N ufw-user-logging-input -N ufw-user-logging-output -N ufw-user-output -A INPUT -j ufw-before-logging-input -A INPUT -j ufw-before-input -A INPUT -j ufw-after-input -A INPUT -j ufw-after-logging-input -A INPUT -j ufw-reject-input -A INPUT -j ufw-track-input -A FORWARD -j ufw-before-logging-forward -A FORWARD -j ufw-before-forward -A FORWARD -j ufw-after-forward -A FORWARD -j ufw-after-logging-forward -A FORWARD -j ufw-reject-forward -A FORWARD -j ufw-track-forward -A OUTPUT -j ufw-before-logging-output -A OUTPUT -j ufw-before-output -A OUTPUT -j ufw-after-output -A OUTPUT -j ufw-after-logging-output -A OUTPUT -j ufw-reject-output -A OUTPUT -j ufw-track-output -A ufw-after-input -p udp -m udp --dport 137 -j ufw-skip-to-policy-input -A ufw-after-input -p udp -m udp --dport 138 -j ufw-skip-to-policy-input -A ufw-after-input -p tcp -m tcp --dport 139 -j ufw-skip-to-policy-input -A ufw-after-input -p tcp -m tcp --dport 445 -j ufw-skip-to-policy-input -A ufw-after-input -p udp -m udp --dport 67 -j ufw-skip-to-policy-input -A ufw-after-input -p udp -m udp --dport 68 -j ufw-skip-to-policy-input -A ufw-after-input -m addrtype --dst-type BROADCAST -j ufw-skip-to-policy-input -A ufw-after-logging-forward -m limit --limit 3/min --limit-burst 10 -j LOG --log-prefix "[UFW BLOCK] " -A ufw-after-logging-input -m limit --limit 3/min --limit-burst 10 -j LOG --log-prefix "[UFW BLOCK] " -A ufw-before-forward -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT -A ufw-before-forward -p icmp -m icmp --icmp-type 3 -j ACCEPT -A ufw-before-forward -p icmp -m icmp --icmp-type 4 -j ACCEPT -A ufw-before-forward -p icmp -m icmp --icmp-type 11 -j ACCEPT -A ufw-before-forward -p icmp -m icmp --icmp-type 12 -j ACCEPT -A ufw-before-forward -p icmp -m icmp --icmp-type 8 -j ACCEPT -A ufw-before-forward -j ufw-user-forward -A ufw-before-input -i lo -j ACCEPT -A ufw-before-input -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT -A ufw-before-input -m conntrack --ctstate INVALID -j ufw-logging-deny -A ufw-before-input -m conntrack --ctstate INVALID -j DROP -A ufw-before-input -p icmp -m icmp --icmp-type 3 -j ACCEPT -A ufw-before-input -p icmp -m icmp --icmp-type 4 -j ACCEPT -A ufw-before-input -p icmp -m icmp --icmp-type 11 -j ACCEPT -A ufw-before-input -p icmp -m icmp --icmp-type 12 -j ACCEPT -A ufw-before-input -p icmp -m icmp --icmp-type 8 -j ACCEPT -A ufw-before-input -p udp -m udp --sport 67 --dport 68 -j ACCEPT -A ufw-before-input -j ufw-not-local -A ufw-before-input -d 224.0.0.251/32 -p udp -m udp --dport 5353 -j ACCEPT -A ufw-before-input -d 239.255.255.250/32 -p udp -m udp --dport 1900 -j ACCEPT -A ufw-before-input -j ufw-user-input -A ufw-before-output -o lo -j ACCEPT -A ufw-before-output -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT -A ufw-before-output -j ufw-user-output -A ufw-logging-allow -m limit --limit 3/min --limit-burst 10 -j LOG --log-prefix "[UFW ALLOW] " -A ufw-logging-deny -m conntrack --ctstate INVALID -m limit --limit 3/min --limit-burst 10 -j RETURN -A ufw-logging-deny -m limit --limit 3/min --limit-burst 10 -j LOG --log-prefix "[UFW BLOCK] " -A ufw-not-local -m addrtype --dst-type LOCAL -j RETURN -A ufw-not-local -m addrtype --dst-type MULTICAST -j RETURN -A ufw-not-local -m addrtype --dst-type BROADCAST -j RETURN -A ufw-not-local -m limit --limit 3/min --limit-burst 10 -j ufw-logging-deny -A ufw-not-local -j DROP -A ufw-skip-to-policy-forward -j DROP -A ufw-skip-to-policy-input -j DROP -A ufw-skip-to-policy-output -j ACCEPT -A ufw-track-output -p tcp -m conntrack --ctstate NEW -j ACCEPT -A ufw-track-output -p udp -m conntrack --ctstate NEW -j ACCEPT -A ufw-user-input -p tcp -m tcp --dport 11121 -j ACCEPT -A ufw-user-input -p udp -m udp --dport 11121 -j ACCEPT -A ufw-user-input -p tcp -m tcp --dport 22 -j ACCEPT -A ufw-user-input -p udp -m udp --dport 22 -j ACCEPT -A ufw-user-input -p tcp -m tcp --dport 80 -j ACCEPT -A ufw-user-input -p udp -m udp --dport 80 -j ACCEPT -A ufw-user-input -p tcp -m tcp --dport 443 -j ACCEPT -A ufw-user-input -p udp -m udp --dport 443 -j ACCEPT -A ufw-user-limit -m limit --limit 3/min -j LOG --log-prefix "[UFW LIMIT BLOCK] " -A ufw-user-limit -j REJECT --reject-with icmp-port-unreachable -A ufw-user-limit-accept -j ACCEPTEdit:
# netstat -tanp Active Internet connections (servers and established) Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN 1121/mysqld tcp 0 0 127.0.0.1:6379 0.0.0.0:* LISTEN 1127/redis-server 1 tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 1096/sshd tcp 0 332 172.31.1.100:22 5.116.231.153:28282 ESTABLISHED 7506/0 tcp6 0 0 :::443 :::* LISTEN 1158/apache2 tcp6 0 0 :::80 :::* LISTEN 1158/apache2 tcp6 0 0 :::22 :::* LISTEN 1096/sshd tcp6 0 0 172.31.1.100:80 155.94.88.138:54138 TIME_WAIT --
 Admin about 6 years@MichaelHampton thx Michael but I've installed Shadowsocks and it's running. Does it mean that is not working correctly?!
Admin about 6 years@MichaelHampton thx Michael but I've installed Shadowsocks and it's running. Does it mean that is not working correctly?! -
 Admin about 6 yearsYour own
Admin about 6 yearsYour ownnetstatoutput shows that nothing is listening on port 11121, and nothing named shadowsocks (or anything similar) is listening to any port. -
 Admin about 6 years@MichaelHampton so it's necessary to run something on a port, then we can find it Open from outside, right?
Admin about 6 years@MichaelHampton so it's necessary to run something on a port, then we can find it Open from outside, right? -
 Admin about 6 yearsYes. Your rules show that connections are allowed on port 11121 but it is necessary to have an application or service listening on it. After that, you will see the port appear when you run
Admin about 6 yearsYes. Your rules show that connections are allowed on port 11121 but it is necessary to have an application or service listening on it. After that, you will see the port appear when you runnetstat -tanp. -
 Admin about 6 yearsGuys, thanks you so much, you were right. My services is not running!! No I have to looking for another solution
Admin about 6 yearsGuys, thanks you so much, you were right. My services is not running!! No I have to looking for another solution -
 Admin about 6 yearsPlease don't put "SOLVED" or answers into the question. They belong below, as an answer.
Admin about 6 yearsPlease don't put "SOLVED" or answers into the question. They belong below, as an answer. -
 Admin about 6 years@MichaelHampton you're right. But I didn't want to post your answers as mine and leave the topic without clear answer.
Admin about 6 years@MichaelHampton you're right. But I didn't want to post your answers as mine and leave the topic without clear answer. -
 Admin about 6 yearsYou may happily write your own answers here. I have plenty of reputation points and I don't need many more :)
Admin about 6 yearsYou may happily write your own answers here. I have plenty of reputation points and I don't need many more :)
-