Problems importing own CA Certificate
Try placing your certificates in /usr/share/ca-certificates
Then modify /etc/ca-certificates.conf to include a reference to your new certificate.
Then run
update-ca-certificates
Update:
So done some more digging on this. It seems that firefox does not honour the /etc/ssl/certs database. Found this - its quite old but I believe it still to be the case.
As far as I can tell each user has their own cert database held in the cert8.db file in their profile directory. This can be updated using firefox directly (is their a reason for wanting to do this command line?) - but obviously each individual user will have to do this. Alternatively there is a command line way of doing this see here and here. You could build a script to go through each user profile directory to do this (yuk!). Doesn't seem to be a "nice" way to do this for all users as far as I can tell.
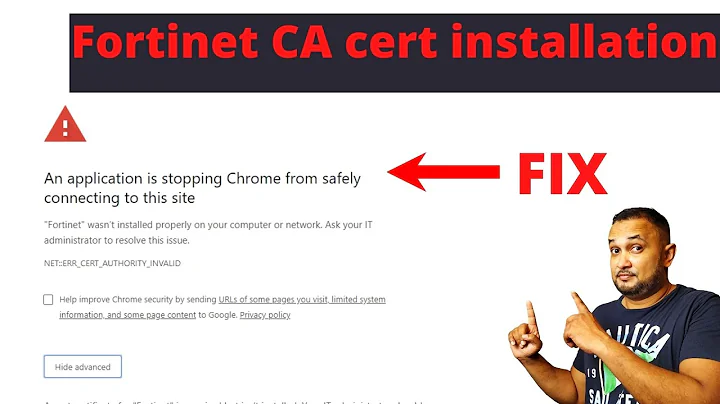
Related videos on Youtube
Sounix Souleke
Updated on September 18, 2022Comments
-
Sounix Souleke almost 2 years
So, I have created my own little CA for my own purposes (inside my network, etc) and I know that the setup works (I can directly import the key into applications, and they connect to the server using the key fine).
But! When I tried to import the CA Certificate so that all applications can use it, they don't (firefox and chromium)
I have
Placed the cacert.pem in /etc/ssl/certs and ran update-ca-certificates and dpkg-reconfigure ca-certificates
Directly placed the cert inside the ca-certificates.crt file (As it wasn't being placed in there inspite of the previous commands)
I'm stumped.
Info:
Ubuntu Desktop, 12.04 x64
cat cacert.pem
-----BEGIN CERTIFICATE----- MIIDCDCCAnG--snip--8guKJUzT -----END CERTIFICATE-----openssl x509 -in cacert.pem -noout -text
Certificate: Data: Version: 3 (0x2) Serial Number: 1xxxxxxxxxxxxxxxxxx3 (0xXXXXXXXXXXXXXX9) Signature Algorithm: sha1WithRSAEncryption Issuer: C=AU, ST=Western Australia, L=xx, O=xx, OU=Webmasters, CN=haven/emailAddress=xx Validity Not Before: Dec 8 11:47:37 2012 GMT Not After : Dec 6 11:47:37 2022 GMT Subject: C=AU, ST=Western Australia, L=xx, O=xx, OU=Webmasters, CN=haven/emailAddress=xx Subject Public Key Info: Public Key Algorithm: rsaEncryption Public-Key: (1024 bit) Modulus: 00:xx:5b Exponent: 65537 (0x10001) X509v3 extensions: X509v3 Subject Key Identifier: 38:xx:95 X509v3 Authority Key Identifier: keyid:38:xx:95 X509v3 Basic Constraints: CA:TRUE Signature Algorithm: sha1WithRSAEncryption 7b:xx:d3Thanks in advance!
-
 Mark E. Haase over 10 yearsYou might find this answer on SU helpful: superuser.com/questions/437330/…
Mark E. Haase over 10 yearsYou might find this answer on SU helpful: superuser.com/questions/437330/…
-
Sounix Souleke over 11 yearsNo go, not showing in firefox's CA list. (did restart firefox)
-
Sounix Souleke over 11 yearsHowever, while running an apt-get update for something else I saw that it wasn't complaining about my server's certificate being off... EDIT: Nope, chrome and FF not picking it up...
-
Sounix Souleke over 11 yearsOkay, thanks. The guide I was following was giving me the impression that there was a global location for CA certificates to be stored. Thanks anyways!