Reading the program header contents of an ELF file
Quoting man elf (but you can find the same info from the ELF spec):
p_offset: This member holds the offset from the beginning of the file at which the first byte of the segment resides.
p_filesz: This member holds the number of bytes in the file image of the segment. It may be zero.
p_memsz: This member holds the number of bytes in the memory image of the segment. It may be zero.
To summarize:
p_offsetis the offset of the segment in the ELF file;p_memszis the size of segment in memory;p_fileszis the size of the segment in the file.
The size in the file may be smaller than than the size in memory p_memsz: in this case the remaining part of the segment is filled with zersos (on POSIX-ish systems this part is mmap-ped using MAP_ANONYMOUS).
References from GNU ld.so:
You might be interested in the code of elfcat (a tool I wrote) which dumps a given segment to stdout.
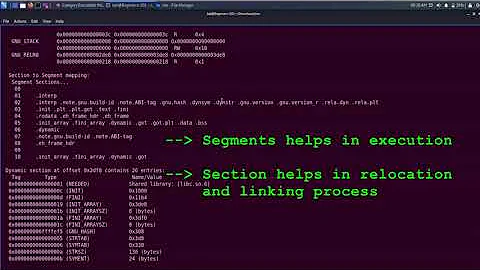
Related videos on Youtube
Sebi
Updated on September 18, 2022Comments
-
Sebi over 1 year
How is it possible to extract loadable program headers individually from ELF files? By examining a binary using readelf one can get output similar to:
$ readelf -l helloworld Elf file type is EXEC (Executable file) Entry point 0x400440 There are 9 program headers, starting at offset 64 Program Headers: Type Offset VirtAddr PhysAddr FileSiz MemSiz Flags Align PHDR 0x0000000000000040 0x0000000000400040 0x0000000000400040 0x00000000000001f8 0x00000000000001f8 R E 8 INTERP 0x0000000000000238 0x0000000000400238 0x0000000000400238 0x000000000000001c 0x000000000000001c R 1 [Requesting program interpreter: /lib64/ld-linux-x86-64.so.2] LOAD 0x0000000000000000 0x0000000000400000 0x0000000000400000 0x000000000000070c 0x000000000000070c R E 200000 LOAD 0x0000000000000e10 0x0000000000600e10 0x0000000000600e10 0x0000000000000230 0x0000000000000238 RW 200000 DYNAMIC 0x0000000000000e28 0x0000000000600e28 0x0000000000600e28 0x00000000000001d0 0x00000000000001d0 RW 8 NOTE 0x0000000000000254 0x0000000000400254 0x0000000000400254 0x0000000000000044 0x0000000000000044 R 4 GNU_EH_FRAME 0x00000000000005e4 0x00000000004005e4 0x00000000004005e4 0x0000000000000034 0x0000000000000034 R 4 GNU_STACK 0x0000000000000000 0x0000000000000000 0x0000000000000000 0x0000000000000000 0x0000000000000000 RW 10 GNU_RELRO 0x0000000000000e10 0x0000000000600e10 0x0000000000600e10 0x00000000000001f0 0x00000000000001f0 R 1 Section to Segment mapping: Segment Sections... 00 01 .interp 02 .interp .note.ABI-tag .note.gnu.build-id .gnu.hash .dynsym .dynstr .gnu.version .gnu.version_r .rela.dyn .rela.plt .init .plt .text .fini .rodata .eh_frame_hdr .eh_frame 03 .init_array .fini_array .jcr .dynamic .got .got.plt .data .bss 04 .dynamic 05 .note.ABI-tag .note.gnu.build-id 06 .eh_frame_hdr 07 08 .init_array .fini_array .jcr .dynamic .gotThis question answers how loadable headers are being mapped to memory(and where) but does not specify from where(from which offset and size) are the sections read within the given binary.
Is it determined by the current program header's fields p_offset and p_filesz?-
 Stark07 about 9 yearsI believe
Stark07 about 9 yearsI believereadlef -hs /bin/yourelfwill give you those details. Give it a try? -
gumenimeda over 8 years"Is it determined by the current program header's fields p_offset and p_filesz?" Yes it is :)
-